Home » New Homes (Page 22)
Category Archives: New Homes
They Out There in the Parking Lot Doing Something Unholy!

If one believes that satisfaction of all physiological needs is enough to provide for a feeling of well-being in an animal (and in man), their zoo existence should make them very content. However, this parasitic existence deprives them of stimuli that would permit an active expression of their physical and mental faculties; hence they often become bored, dull, and apathetic. This disposition can lead to deviance in man. When men are engaged in deviant behavior, they are often involved in criminal activity. There is much more to understanding criminal behavior than simply mapping out the pattered aspects of the behaviors in question. For starters, one must consider the thoughts and cognitions that underlie the behaviors. Appreciating how different criminals think is anything but exact science. After all, we are talking about trying to figuratively crawl inside the heads of criminals in an effort to tap their state of mind and decision-making process across whole categories of offenders. Nonetheless, there are important issues that must be considered. First, one must tackle the issue of criminal motivation. As mentioned, criminal definitions expressly indicate that the criteria must be satisfied before an act can be considered a crime. For the legal scholar, criminal motivation is a relatively simple concept referring narrowly to the individual’s state of mind (men reus) at the time of the crime. For the criminologist who seeks to better understand criminal behavior, criminal motivation is a broad and complex concept that speaks to the totality of the offender’s mental state, in that time period preceding the crime, during the actual commission of the crime, and in the post-offense aftermath. #RandolphHarris 1 of 21

Criminal motivation must thus be approached as a complex, situationally based phenomenon in need of careful consideration. Moreover, a full treatment of this concept must also take into account the ways that the expected victim and setting roles can shape the mindset of the offender. For example, the issue of criminal motivation, as it applies to the mindset of street thugs (id est, stick up artist). Criminal planning is yet another important part of the criminal thought process. Once the prospective criminal decides that it is beneficial to commit an offense, the individual must settle on what constitutes the most effective and efficient set of behavioral processes to achieve said act. Planning refers to the rational decision-making processes that map out target selection and the way in which the individual(s) intend to commit the crime. For instance, burglary crews often implement a system of planning that includes a clearly established division of labor, event simulations, and contingency plans. Whereas juvenile car thieves use limited amounts of pre-event planning with offenders engaging more haphazard target selection method and operate with little concern for police intervention. Having a clear conscience is a hallmark of the contemporary human psyche. We as Americans have developed a near instinctual desire or need to think of ourselves as good people. In effect, there appears to be no wrongful behavior that the human mind is unable to cognitively reconstitute as normal or acceptable. Normative neutralizations are part and parcel to the cognitive dimension of crime. When their behavior is called into question by themselves or others, criminals are compelled to generate a cognitive neutralization that excuses or justifies their actions. #RandolphHarris 2 of 21

In effect, when persons do wrong, they feel the need to convince themselves and others that it was not so bad. They make believe that victims of intimate partner violence deserved their abusive situation. Also, rapists often vilify their victims and downplay personal wrongdoing, and men and women of the evening come to think and talk about their careers and clients. All criminal events are social phenomena. As mentioned, they occur in a given social situation or what is termed a “situated criminal transaction.” The form of that transaction is often patterned for any given offense and may even appear to be scripted. While the habitual interactions of victims and audience members is worthy of notice, criminologists are also interested in the routinized behavior of the offender. We have come to realize that the patterning of offender attitudes, beliefs, and behaviors can be a by-product of the behavior and sentiments that exist in the larger criminal subculture. In a noncriminological context, we acknowledge that cultural-based learning is a force to be reckoned with. Few would question the influence that a place of employment, say a law firm, has on the attitudes, beliefs, and behaviors of, say, a new attorney who seeks partner status. The same can be said of criminal subculture. A large part of a criminal’s normative and behavioral makeup can be fostered though interactions with fellow offenders. Significant relationships and scripted roles can be developed and these relationships often play a significant role in the way that the offenders think and behave. For example, there is often a complex web of roles and relationships that exist within the Sacramento sex-for-crack market. #RandolphHarris 3 of 21

It is useful to conceive of a criminal subculture as having two central features: organizational alignment and socialization scripts. Organizational alignment refers to the networking or structuring of interactions that shape a given criminal subculture. Membership plays an importance in the roles and position in criminal outcomes. Criminals typically carry out their misdeeds within the context of one of the following organizational forms: loners, colleagues, peers, teams, and formal organizations. Loners work alone, relying on no one to assist them in their misdeeds. They manipulate and/or adapt the behavioral and cognitive aspects of their legitimate (noncriminal) Worlds as a means of developing and refining their criminal repertoire. When it comes to the term “therapeutic self-medicators” they are described as pharmacists who misappropriate their pharmacological expertise en route to developing their own private drug abuse patterns. These insolent professionals use drugs alone and slowly manipulate their legitimate training and professional roles until they have in effect taught themselves how to think and act as a drug addict. We term other drug-using pharmacists “recreational abusers.” These individuals often operate within a colleague-based organizational alignment. Colleagues offend alone but look to the misdeeds and rationalizations of other deviants to shape thoughts and behaviors associated with their illicit behavior. Those organizational alignment that fit into the peer category take on a slightly different social format. #RandolphHarris 4 of 21

Peers take on co-offenders and openly interaction with other perpetrators in a loose and transient social setting. For example, hard-core heroin addicts comingle and draw upon the collective experience of the junkie subculture to refine their drug-related skills and attitudes. Criminal subcultures can also take on an organizational alignment that is referred to as teams. A term structure is defined by its consistent and patterned interactions. Here, the offender comes to interact and offend with the same group of individuals. Consistent relationships are seen as mutually beneficial, s offenders gain proficiency from a patterned division of labor and loosely structure mentoring. For example, the loose social organization of marijuana grower in Kentucky blue grass country has a growth and distribution system that is held together by informal norms and behaviors. The mot advanced of criminal subcultures manifest itself as formal organizations. By operating in a membership-like format, these criminals serve fixed roles, with some sort of formal or informal mentoring system to recruit and retain the membership base. Organized crime “families” are the best example of this organizational form. An example of the organized crime family is demonstrated by the way in which Adolph Hitler used the Nazi regime to carry out the Holocaust. Organizational alignment represents the structural dimension of a criminal subculture as it describes the context in which criminal interactions occur. This structural, dimension gives way to a process-oriented aspect of criminal subcultures termed socialization scripts. #RandolphHarris 5 of 21

When it comes to socialization scripts, the actual content of subcultural messages and interactions is placed center stage as we seek to ascertain the process through which criminal learning occurs. There is evidence that the cultural message and cues within our nation’s universities can serve to shape the motives and behaviors of college men to engage in gang rape. We often find an illuminating way that the content and dynamics of the learning process comes to produce a socialization script that is somewhat unique to gang rapists. Criminal acts are, by definition, prohibited by law, and the laws of this democratic country are supposed to represent the collective conscious of the collective conscious of the populous. As such, in theory, that which is defined as a potential harm or offense to the state should be defined as a potential harm or offense to the average citizen. Reactions to criminal behaviors can take on one or two forms: formal or informal. Formal reactions to criminal events take the shape of institutional responses. In most cases, the institution in questions is the criminal justice system (id est, law enforcement, courts, and corrections). When a mother openly beats a child in public, law enforcement officials are quick to reference existing criminal statues and cite the mother with child abuse. This matter is then forwarded to the court system where the courtroom workgroup (id est, prosecutor, defense attorney, judge) sets out to determine if in fact a crime has been committed and, if so, what should be the appropriate punishment. Once a sentence has been handed down, members of the correctional system impose the prescribed punishment. To this end, a full understanding of crime begs consideration of the way that institutions such as law enforcement, the courts, and our correctional system respond to the various types of criminal offenses. #RandolphHarris 6 of 21

Institutional (formal) contacts are not the only form of societal rection that can potentially shape the thoughts and behaviors of those involved in the criminal event. Informal reactions are also important. These are the perceived or real responses from audience members and/or valued relations that help shape criminal event. On a most fundamental level, audience members may intervene or choose not to intervene in a criminal event, thereby altering its existence. In fact, the mere existence of an audience changes the nature of the offense. For instance, the group dynamic plays an important role in the occurrence of gang rape on university campuses. Whereas the one-on-one dynamic of marital rape produces a significant different series of events. Informal reactions also serve as important precursors to a criminal event. Namely, the perceived responses of valued relations (id est, friends, family members, role models) can and do effect both the decision to commit a crime and the accounts and justifications that are constructed once the event has transpired. Scholars once again observe that these perceptions often become pattered for a given type of crime. This is even applied to audience roles in the murder event. There often times a subtle spirit of treachery in a system. Some crime families are suave and unctuously polite. As one man puts it: “If we wish to kill a man we approach him, we ear, drink, sleep, work and rest with him, it may be for several moons. We bide our time. We call him friend.” As a result, in the not infrequent cases of murder, suspicion falls on those who have tried to be friends with the victim. #RandolphHarris 7 of 21

That is one reason some people do not trust others who start hovering around them, act as if they know them, or sit around watching one. When an individual is infrequently seen, and varies one’s times of outings, always seeing the same people in the vicinity is a sign to be cautious. It is not statistically probable that they all are on the same varied and infrequent schedule, so chances are these individuals are up to something unholy. Therefore, it is important to pay attention to engagement disloyalty. During an encounter of three or more participants, it is possible for a subset of participants to form a byplay, a noninclusive engagement that is carried on simultaneously with the first but in a way carefully calculated not to interfere with it too openly. These byplays may be carried on relatively openly when they appear to be in the interests of the business at hand—as when a speaker quietly asks some questions of the chairman before turning to speak—or relatively furtively when byplay is patently not in the interests of the dominant interaction. This kind of disaffection seems especially common in large engagements where the presence of manly loyal participants guarantees that the dominant engagement will be sustained. Disaffection is especially treacherous in clusters of three or four, where the participants remaining loyal may be in a numerical minority, subjected to pointed insult by the byplay of others. As might be expected, when an encounter must be sustained by persons unable to use their eyes to scan and monitor what is occurring, byplays employing physical acts become difficult to control and constitute a special threat to the integrity of the encounter. #RandolphHarris 8 of 21

For instance, consternation was felt by visually impaired man in an engagement of three men and one woman, when he heard rustling and suppressed giggling that did not seem to arise from what was being stalked about by the full company at the time. In many instances, these subordinate byplays involve only members of the dominant encounter, and involve them in such a way as not to broadcast to the company at large—to the situation—that disloyalty is occurring. I do not propose to consider this phenomenon here, since it could just as well be considered solely in terms of the dynamics of the engagement itself. Relevant, however, as those byplays that draw some of their membership from persons officially excluded from the dominant engagement, for here disloyalty is made visible to bystanders, and the doings of the betrayed engagement are “opened up,” to at least some of the nonparticipants present. An extreme form of disloyalty is fond where an individual, in the process of being led into the role of the butt, is brought into an engagement maliciously, just so the instigator can be disloyal to the engagement that results. The perpetrator makes a pretense to the butt that he is treating him as a coparticipant, while at the same time openly using the interaction thus created as a source of amusement for oneself and others. The model here, perhaps, is the kind of baiting of animals that people engage in at a zoon, where one individual interacts with an animal until the animal responds, and then uses the animals response as a source of fun between himself and a second individual. #RandolphHarris 9 of 21

People can spend their lives studying systems and system word and never come to real things. In fact, 90 percent of our ordinary knowledges does not really exist; it exists only in imagination. Realization of sleep is the only one thing. It is necessary to find ways to awaken, but before that you must realize that you are asleep. Compare sleep and waking. All ideas of the work begin with the idea of sleep and the possibility of waking. All other ideas—life ideas—may be clever or elaborate but they are all ideas of sleeping people produced for other sleeping people. Sleep is the result of many things: division of personalities, different “I”s, contradictions, identifications and so on. However, the first of all, just pure without any theory, is the realization of sleep. Currently, life is not long enough for changing our being if we work on it as we do at everything else in life. Something can be attained only if one uses a more perfected kind of method. The first condition is understanding. All the rest is proportionate to understanding. There must also be efforts in connection with emotions and will. One must be able to go against oneself to give up one’s will. First you must ask yourself: What is will? We have no will, so how are we to give up what we do not have? This mean, first, that you never agree that you have no will; you only agree in words. Secondly, we do not always have will but only at times. Will means a strong desire. If there is no strong desire, there is nothing to give up; there is no will. At another moment, we have a strong desire that it is against work, and if we stop, it means that we give up will. #RandolphHarris 10 of 21

It is not at every moment that we can give up will but only at special moments. And what does it mean “against work”? It means against rules and principles of the work or against something you are personally told to do or not to do. There are certain general rules and principles of the work or against something you are personally told to do or not to do. There are certain general rules and principles, and there may be personal conditions for different people. “Should one ask for further personal directions?” Yes, but if one asks one must obey. One is not obliged to do anything if one does not ask, so before asking one must think twice. In common home accidents, a dangerous product is wrongly applied, spilled, or consumed. Homes today are full of corrosive and toxic materials, for cleaning drains, dissolving stains, poisoning insects, and so forth. All too often, children dink them and die. With advanced technology, none of these tasks will require such harsh, crude chemicals. Cleaning could be performed by selective nanomachines instead of corrosive chemicals; insects could be controlled be devices like ecosystem protectors that know the difference between a cockroach and a person or a ladybug. There will doubtless be room for deadly accidents, but with care and hard work, it should be possible to ensure that nanotechnologies for the home are safer than what they replace, saving many lives. It is, of course, possible to imagine safety nightmares: nanotechnology could be used to make products far more destructive than anything we have seen because it could be used to extend almost any ability further then we have seen. #RandolphHarris 11 of 21

Such products presumably will not be commonplace: even today, nerve gas would make a potent pesticide, but it is not sold for home use. Thinking realistically about hazards requires common sense. We have already seen how post-breakthrough technologies can eliminate oil spills by eliminating oil consumption. A similar story could be told of almost any class of industrial accident today. However, what about accidents—spills and the like—with the new technologies? Rather than trying to paint a picture of a future technology, of how it could fail and what the responses could be, it seems better to try a thought experiment. What could be done to deal with oil spills, if oil were still in use? This will show how nanotechnologies can be used to cope with accidents: If there were a spill and oil on the shore, advanced nanomechanisms could do an excellent job of separating oil from sand, removing oil from rocks, and cleaning crude oil from feathers on birds and the feathery legs of barnacles. Oil contamination is a pollution problem, and nanotechnology will be a great aid in cleaning up pollution. But why should the oil reach the shore? Economical production would make it easy to stockpile cleanup equipment near all the major shipping routes, along with fleets of helicopters to deliver it at the first distress call from a tanker. Oil cleanup equipment built with nanotechnology could surely do an excellent job of scooping oil from the water before it could reach the shore. #RandolphHarris 12 of 21

But why should the oil leave the tanker? Economical production of strong materials could make seamless hulls of fibrous material far tougher than steel, with double, triple, or quadruple layers. Smart materials could even make punctures self-sealing. Hulls like this could be run into rocks at highway speeds without spilling oil. But why should anyone be shipping crude oil across the sea? Even if oil were still being pumped (despite inexpensive solar energy and solar-derived fuels), efficient molecule-processing systems could refine it into pure, fuels at the wellhead, and inexpensive tunneling machines could provide routes for deeply buried pipelines. Any one of these advances would shrink or eliminate today’s problem with oil spills, and all of them are feasible. This example suggests a general pattern. If nanotechnology can provide so many different ways to avoid or deal with an oil spill—one of the largest and most environmentally destructive accidents caused by today’s industry—it can probably do likewise for industrial accidents in general. The most direct approach is the most basic: the elimination of anything resembling today’s bulk industrial plants and processes. The shifts from messy frilling activities and huge tankers to small-scale distributed systems based on solar cells is characteristic of the style in which nanotechnology can be used. #RandolphHarris 13 of 21

The chemical industry today typically relies on plants full of large, pressurized tanks of chemicals. Not surprisingly, these occasionally spill, explode, or burn. With nanotechnology, chemical plants will be unnecessary because molecules can be transformed in smaller numbers, as needed and where needed, with no need for high temperatures, high pressures, or big tanks. This will not only avoid polluting by-products, but reduce the risk of accidents. Now, given that the United States of America wanted the Soviets to pull their missiles out of Cuba, during the Cuban missile crisis, why could Kennedy not have threatened that he would annihilate Moscow unless Khrushchev removed the missiles? This would be a compellent threat; it must specify the precise conditions of compliance (missiles back to Russia, or in crates on a ship in Havana harbor?) and a deadline for compliance. The problem is that in practice such a threat would not be believed, either by Khrushchev or by anyone else. The threatened action, surely leading to a global thermonuclear war, is simply too drastic to be credible. If the missiles were not out by the deadline, rather than annihilate the World, Kennedy would surely be tempted to extend the deadline by a day, and then another day. There are several ways of lending credibility to threats. The use of an automatic device seems the most promising in this context. (Reputation will not work, because after the threat is carried out there is no tomorrow. Contracts will not work, because everyone will face the overwhelming temptation to renegotiate. And so on.) #RandolphHarris 14 of 21

The use of an automatic device is an approach basis for the movies Failsafe and Dr. Strangelove. In Dr. Strangelove the Soviets have installed a “doomsday machine” that monitors American transgressions and automatically launches Soviet retaliation under circumstances specified in a tamperproof computer program. In Failsafe it is the Americans who have the doomsday machine. Those who have seen these movies (which we recommend highly) know why Kennedy should not use a similar device to make his threat credible. In theory, under ideal circumstances, everything works just as planned. The very knowledge that an automatic device is in place makes the threat credible. Khrushchev backs down, the threat does not have to be carried out, and all is well. If a threat is sure to succeed, it need never be carried out, and it does not matter how big or dire it is, or how much it would hurt you too to carry it out. However, in practice, you cannot be absolutely sure that it will work as planned. There are in fact two kinds of errors that can occur. First, the threat may not succeed. Suppose Kennedy has totally misjudged Khrushchev’s mindset. Then Khrushchev does not back down, and the doomsday device annihilates the World just as Kennedy is regretting having installed it. Second, the threat may be carried out even when it should not. Suppose the Soviets back down, but the news reaches the doomsday computer just too late. Because such errors are always possible, Kennedy does not want to rely on threats that are too costly to carry out. Knowing this, Khrushchev will not believe the threats, and they will not deter or compel him. #RandolphHarris 15 of 21

Kennedy may claim that an automatic launcher has the sole authority to fire at Moscow if the Soviet missiles are not out of Cuba by Monday, but Khrushchev can be sure that Kennedy controls and override button. Although the threat of certainty of war is not credible, one of a risk or probability of war can be credible. If Khrushchev fails to comply, there is a risk, but not a certainty, that the missiles will fly. The uncertainty scales down the threat. The scaling down makes the threat more tolerable to the United States of America, and therefore more credible to the Soviets. This is a lot like another device for credibility we mentioned in the past, namely moving in small steps. There we considered breaking up a large promise into a succession of small ones. If I am trying to sell you a valuable piece of information for a thousand dollars, I may not be willing to disclose it in return for your promise to pay, but may be willing to reveal installments one by one in return for corresponding payments. A similar principle applies to threats. And here the steps consist of degrees of risk. Each stage of escalation by the United States of America or the Soviet Union increases the risk of global war; each small concession reduces the risk. The calculation for each side is how far to proceed or retreat alone this route. If Kennedy is willing to go farther than Khrushchev, then Kennedy’s brinkmanship will succeed. Kennedy cannot credibly threaten an immediate all-out nuclear strike, but he can credibly raise the risks to some degree by taking some confrontational actions. For example, he may be willing to risk one chance is six of nuclear war to ensure the removal of the missiles. #RandolphHarris 16 of 21

Then Khrushchev can no longer conclude that Kennedy’s threat is vacuous; it is in Kennedy’s interest to expose himself to this risk if it will motivate the Soviets to remove the missiles. If Khrushchev finds this degree of risk intolerable, then the brinkmanship has accomplished its objective: to allow Kennedy to choose a more appropriately sized threat, one big enough to work and yet small enough to be believed. We still have to ask how Kennedy can go about threatening a risk of war, short of a certainty. Moving forward, in the spring of 1989, when Dr. James T. Hansen chief of NASA’s Goddard Institute for Space Studies, prepared to testify before the U.S. Congress on the “greenhouse effect”—the overheating of the global climate—he submitted his text for clearance to the White House Office of Management and Budget (OBM). Hansen firmly believed that the time had come for the U.S.A. government to take significant action to prevent drought and other severe effects of climatic warming. When he got his text back, however, he discovered that the OBM had come for the U.S.A. government to take significant action to prevent drought and other sever effects of climatic warming. When he got his text back, however, he discovered that the OMB had added a paragraph throwing doubt on the scientific evidence about planetary warming, and considerably softening his position. He protested, lost the internal battle, and then made his personal views public through the press. Behind this collision between the administration and one of the government’s top scientists lay a little-noticed bureaucratic battle. #RandolphHarris 17 of 21

The U.S.A. Department and the Environmental Protection Agency both wanted the United States of America to take the international lead in combating the greenhouse problem. By contrast, the OMB and the Department of Energy backed a go-slow approach. When Hansen took his protest to the media, Senator Al Gore, one of the few technologically sophisticated members of the U.S.A. Congress, demanded that OBM “testify about the basis for their conclusions. I want to determine…the climatic models they have used.” This reference to “models” is a sure tip-off that the struggle would be waged at the meta-tactical level. For more and more government programs and policies are shaped by the assumptions and sub-assumptions buried inside complex computer models. Thus while Gore in the Senate was questioning the models relied on by the go-slow camp, Sununu in the White House was challenging the reliability of the models that provided ammunition for the other side. He was on top of the scientific literature and thought the computer models predicting significant warming were too primitive to form a reliable basis for action. Today, whether dealing with the economy, health costs, strategic arms, budget deficits, toxic waste, or tax policy, behind almost every major political issue we find teams of modelers and counter-modelers supplying the raw materials for this kind of political controversy. A systematic model can help us visualize complex phenomena. It consists of a list of variables, each of which is assigned a weight based on its presumed significance. #RandolphHarris 18 of 21

Computers make it possible to build models with much larger numbers of variables than the unaided intellect alone. They also help us to study what happens when the variables are given different weights or are interrelated in alternative ways. However, no matter how “hard” the final output may appear, all models are ultimately, and inescapably, based on “soft” assumptions. Moreover, decisions about how much importance to assign to any given variable, or its weighting, are frequently “soft,” intuitive or arbitrary. As a result, political in-fighters, skilled at meta-tactics, battle fiercely over weights, variables, and the way they are linked. Despite the political pressures that tilt and bias the outcome, the results of which conflicts normally come packaged in impressive, seemingly neutral and value-free computer printout. Models are used in developing and choosing policies, in evaluating program effectiveness, and in asking “what is…” questions. However, as we learn from Data Wars, a recent study of government modeling, they can also be used to “obscure an issue or two lend credence to a previously made policy position…to delay decision-making; to give symbolic rather than real attention to a decision; to confuse or obfuscate decision-making,” and so on. “Model use occurs as much for political and ideological need as for technical [substantive decision] need.” This, they note, is necessarily so because “computer models influence ‘who gets what.’” A study by the U.S.A. Congressional Research Service, for example, pointed out that government cuts in social programs during the 1980s, threw at least 557,000 Americans into poverty. The number provided ammunition to politicians who opposed such cuts. However, this figure was not based on counting the poor. #RandolphHarris 19 of 21

Instead, like an increasing number of other statistics, it was a result of politically contentious premises built into a model that attempted to show what might have happened had the budget cuts not taken place. Just how rarefied meta-tactics become as computer data spreads in government is illustrated by the controversy that broke out over missing people and what the Census Bureau technicians called “hot deck imputation.” In November 1988 the cities of New York, Huston, Chicago, and Los Angeles field a lawsuit against the U.S. Bureau of the Census to force a change in the way it counts. They were joined by civil rights groups, the Conference of Mayors, and other organizations. In any census, some groups are undercounted. Poor, transient, and homeless groups are harder to count. Undocumented aliens may not wish to be counted. Other escape the information net for other reasons. Whatever its reason, undercounting can have potent political consequences. Because Washington sends billions of tax dollars back to the cities and states, cities can be deprived of federal funds to which they might otherwise be entitled. Since seats in the House of Representatives are apportioned on the basis of population, states with large uncounted populations may be cheated of full representation. This, in turn, can cost them many other benefits. Inadequate information can thus shift power. To compensate for undercounting, the Census Bureau’s computers, on finding a house for which information is lacking, are now programmed to assume that the unaccounted-for people have characteristics similar to people who live nearby. The computers then fill in the missing data, as though it had been provided by the missing people. #RandolphHarris 20 of 21

The result is that millions of persons, presumed to exist, are really a phantom population whose characteristics we are guessing at. Hot deck imputing may be a better way of compensating for the unknown than previously used statistical methods, but, as with all such techniques, its assumptions are open to challenge. On the strength of these assumptions—informed as they might be—voters in Indiana lost one member in Congress whose seat was reassigned to Florida instead. “Hot deck imputation” shifted political power. In sum, therefore, a new stage of political conflict is developing—a battle over the assumptions that lie behind still other assumptions, often embedded in complex computer software. It is a conflict over meta-questions. It reflects the rise of the super-symbolic economy. This new economy could not run for a second without human contact, imagination, intuition, care, compassion, psychological sensitivity, and other qualities we still identify with people rather than machines. However, it also requires ever more complex and abstract knowledge, based on vast avalanches of data and information—all of which is subject to increasingly refined political manipulation. What this look at info-tactics, and especially the new meta-tactics, teaches us is that laws set limits on governmental secrecy only touch the outermost skin of democracy’s knowledge problem. The new economy, by its very nature, requires a free exchange of ideas, innovative theories, and a questioning of authority. And yet…despite glasnost, despite “freedom of information” legislation, despite leaks, and the difficulty of today’s governments face in keeping things secret—despite all of these and more—the actual operations of those who hold power may well be growing more, not less, opaque. That is the “meta-secret” of power. #RandolphHarris 21 of 21

Cresleigh Homes

Open concept means freedom. 😍 It means flexibility. And it means the whole family (and lots of friends!) can all chill in the same space. 🎉

We love showing off our floor plans at #PlumasRanch! There’s so much to enjoy (and so much space to enjoy it in!)

Learn more about #CresleighHomes on our website.
I’m Going to Target

Love keeps the soul on the track of its fate and keeps consciousness at the edge of the abyss of the infinity that is the rage of the soul. However, as a result of the human condition, sometimes the soul becomes disjointed with its reality. This is why we need to understand how and why people commit different varieties of criminal behaviour, and use this tact to provide insights into what can be done to remedy the situation. That is why scholars adopt a crime typology or criminal behaviour system approach to crime. Typology scholars rely on logic-based conceptual frameworks to categorize and theorize about crime. In effect, he or she constructs ad defines a set of underlying dimensions that allows one to justify and substantiate a given typology of crime. Keep in mind that the differences or similarities on any or all of the theoretical dimensions need not be complete. Instead, it is tacitly implied that partial or conditional similarities or differences can exist across or with the framework of the typology. It is argued that this more focused approach to the study of criminal behaviour affords us a fuller understanding of the patterns and dynamics of criminal behaviour. It allows us to speak to the unique factors associated with a given category of crime. At the same time, we can identify similarities that exist between homicide and aggravated assault, rape, or even burglary. When speaking of criminal behaviour systems, it is useful to adopt the criminal events as the unit of analysis. #RandolphHarris 1 of 19

The criminal event is the social context in which the crime occurs, with every criminal event being comprised of an offender, a victim (or target), and a setting. By way of example, the average date rape involves a male offender and a female victim, and takes place in a leisure setting such as the offender’s house. Too often, typology scholars focus exclusively on the offender (criminal) or offense (crime) and lose sight of the meaningful roles that the victim and/or contextual norms of a given setting play in the criminal outcome. Criminal events are best understood when viewed in light of four organizing principles or sensitizing concepts: behavioural aspects, cognitive aspects, cultural aspects and societal reactions. These sensitizing concepts specifically direct one’s attention toward common themes or criteria by which one can compare and contrast the offender, victim, and setting roles across different types of crime and thus serve as the underlying dimensions of the present seven-part classification scheme. In other words, these organizing principles stress the multifaceted aspects of the criminal event (id est, the offender, victim, situation, and legal distinctions) and allow for a more complete appreciation for the category or type of crime in question. Human beings have a knack for patterning and regimenting their behaviour over time. Crime is no different Much like the common behavioural components to swimming, there are common behavioural aspects to homicide. Swimming involves the act of propelling one’s self through water, whereas a homicide manifest itself as the unlawful killing of a human being. #RandolphHarris 2 of 19

Likewise, there are different techniques, patterns, and skills that delineate the various swimming strokes (exempli gratia, breaststroke, backstroke). There are also different techniques, patterns, and skills associated with different subtypes of homicide (exempli, stranger homicide, intimate homicide, serial homicide). The concepts of crime and criminal behaviour have their humble beginnings in the legal definitions, or necessary conditions that are set forth by the criminal code. Most fundamentally, a crime is defined as an act committed or omitted in violation of a law or statue that expressly forbids or commands it and is accompanied by some form of state-sanctioned punishment. In order for the state to establish that said crime has occurred, it must be shown that the event in question satisfies the actus reus (guilty act) and the mens reus (guilty mind) aspects of a particular criminal statue. These two critical components detail the behavioural and mental states required for an event to be defined as criminal. For example, most jurisdictions define burglary as the unlawful entry of a structure (actus reus) with the intent to commit a felony or theft (mens reus). The behavioural aspects of a given type of crime also encompass the skills and techniques that are used by offenders. In the case of homicide, this means that one must speak to the manner in which the offender brings about the death of the victim (exempli gratia, strangulation, blunt-force trauma, gunshot wound). #RandolphHarris 3 of 19

Many crime oblige or even require the offender to master the use of various mechanisms or tools that serve to assist in the commission of the offense. The “tools of the trade” for a murderer might include a wide variety of weapons (exempli gratia, guns, knives, toxins, bare hands). Burglar are often obliged to use deception or disguises, enlist the assistance of various power tools, or simply peer through windows en route to gaining entry into a targeted residence. Collectively, the patterned skills, techniques, and tools of the trade make up the “nuts and bolts” of how offenders effectively yet efficiently perpetrate their criminal acts. Recall all criminal events are comprised of an offender, a victim, and a setting. Criminal events do not occur when these three elements spontaneously combust. Instead, they occur in transactional manner whereby the offender, victim, and audience members negotiate the criminal outcome. Homicide event are “situated transactions” in which the pressure, volatility, and eventual lethal violence progresses through a series of interactional stages that are collectively negotiated by the offender, victim, and audience member. Criminal transaction often takes on a given “form.” For example, some transactions involve a lone offender and a lone victim in an isolated environment. Other criminal transactions involve multiple offenders, multiple victims, and interactive audience member. A full understanding of the patterned form of the criminal transaction is necessary if one is to comprehend the behavioural aspects of a given offense type. #RandolphHarris 4 of 19

There also exists a patterned “process” to criminal transactions whereby stable actions and roles emerge among the offender, victim, and audience member. For example, there are patterned interactions that exist between burglars, illegitimate pawn shop operators (id est, fences), and the pawn shop customers. The behavioural aspects of criminal offending are patterned on yet another, more broadly defined level Namely, offenders tend to progress through what is called a criminal career. Criminal careers are measured in terms of recidivism rates (rates of re-offending) as well as career trajectories (offending routines that emerge as individuals enter into, persist through, and exit their criminal lifestyles). Criminals can specialize in a given type of crime or behave as generalists who engage in a wide variety of criminal behaviours. Both of these career variations, for example, show how female burglars tend to focus their offending in a select few offense categories, while their male counterparts tend to be less discriminatory and adopt more of a “jack of all trades” orientation. The severity of an offender’s wrongdoings may remain relatively stable or they may intensify. #RandolphHarris 5 of 19

Similarly, a criminal career can be short and erratic or it can be long and tightly routinized. The individuals may have frequent contact with the criminal justice system or might be able to allude suspicion and apprehension for extended periods of time. Past research suggests that there tends to be a patterned aspect of criminal career trajectory within a given criminal behaviour system. There are other types of behaviour that are important to focus on, that tend to be more conducive to society. Participation in an accessible engagement not only directly exposes the individual to linguistic and expressive communication with the other participants in the encounter but also opens up the possibility that they will expressively communicate something about one to bystanders. Seeking some degree of intimacy with potential fellow participants in the encounter, the individual can find oneself spurned or otherwise mistreated in a way that is visible to bystanders. Given these potential exposures, we find regulations to safeguard the individual. These constraints appear in two-person engagements as expressions of loyalty to the encounter. In both cases we deal with a participant’s obligation to stay within “his” engagement. One form of containment is found in the obligation of participants to withhold attention from matters occurring outside of the engagement. We can appreciate the operation of this norm by nothing the various context in which the norm is not adhered to. #RandolphHarris 6 of 19

Quite momentary and minor disaffection constantly occurs, as when an individual turns away from a moment to see who has entered the situation, or to find a suitable chair, expressing by one’s manner and by the arts of shielding involvement that somehow one’s spirit is still attached to the engagement. Where individuals do not have to worry about each other’s small slights because of a long-standing relation of familiarity and intimacy—as between some husbands and wives—one participant may hold the engagement together while the other scans the room in search of useful information. When a couple eats at what is for them a “good” restaurant, the member with one’s back to the assembled others may be annoyed to find one’s partner giving attention to the other tables instead of to the talk at hand. Such disloyalty can of course become excessive, by middle-class standards, suggesting a demoralization (or at least an altered understanding) regarding what is ordinarily owed one’s fellow participants. Hollywood restaurants provide good illustrations. There was a stir in Dave Chasen’s Restaurant in Beverly Hills when Dore Schary walked in. Chasen’s is run by the former stage comedian whose name it bears, and it is popular with people in the motion-picture industry…All the other patrons focused their attention of Schary. They seemed to be looking around at everybody except the people they were with and with whom they were managing to carry on conversations. #RandolphHarris 7 of 19

Schary was not a bit self-concious…He was almost the only man in Chasen’s who was not at the moment looking around at someone other than the person he was talking to. More extreme forms of disloyalty are very commonly found among the mentally ill; it is often because of such delicts that persons are identified as mentally ill in the first place. For example, I observed a female psychotic, strongly attached to her mother and to her psychiatrist, who would, in the midst of a conversation, allow all of her steps. At the approach of either her mother or her therapist, the patient’s body would remain in the talk but her head and interest would turn elsewhere. After a few weeks, as she “recovered” from an “episode,” this interaction indelicacy gradually disappeared until it was possible for either of these figures to walk by without causing the patient visible perturbation. Although these figures no doubt still brained away some of her attention, she was able or willing to disguise the fact. The same patient, while “in” a psychotic break, would play ping-pong with one person while allowing her attention to rest openly on a nearby foursome of her age-mates playing bridge. Gradually, as weeks went by and she “came out” of the psychotic break, she increasingly paid deference to her ping-pong game by according it her cognitive and visual attention, and increasingly during play she exhibited civil inattention to neighbouring engagements. #RandolphHarris 8 of 19

“Is there a place in the static triad where a group of ‘I’s unconnected with magnetic center is active and false personality passive?” Certain group of “I”s or personalities become active, and they are centered round magnetic center. First magnetic center itself, and then those “I”s that range themselves round magnetic center are opposed to false personality. Then, at a certain moment, magnetic center becomes active and false personality passive. Magnetic center is a combination of a certain group of interests. Magnetic center does not lead you, for leading would mean progress and you remain in one place. However, when things come, then with the help of magnetic center you will be able to see which is which or whether you are interested or not interested in a thing. You can make a choice. Before one comes into the work, magnetic center has reached a certain point which transforms it into a certain group of interests When one meets the work it becomes interested in school-work and then it disappears as magnetic center, because magnetic center is a weak thing. For instance, in the first triangle of the triad, it is composed of body, soul and essence (=), false personality (+), and “I”s (-). Now supposing that these “I” are already divided into certain groups, maybe not attached, but still not hostile to the magnetic center, which can exist and eventually develop into something better. The groups of “I”s which are always hostile and always harmful are false personality itself. #RandolphHarris 9 of 19

Somebody asked whether the change from one form of the static triad to another depended on change being. Yes, every small change is a change of being although this expression is generally applied to bigger, more serious changes. When we speak about change of being we speak about change from men nos 1, 2, and 3 to man no. 4 for instance. This is change of being, but of course this big jump consists of many small jumps. The static triad represents you. It shows the state of your being, what you are at a given moment. One of the points, body and essence, is always the same, but the relation of the other two points changes. If body and essence are normal they are impartial and do not take one side or the other, but if there is something wrong in them they are on the side of false personality. When in a state of doubt remember to try and bring up other “I”s which have a certain valuation. This is the only way to conquer doubts. In order to develop you must have some capacity for valuation They only practical approach is to think of the different sides of yourself and to find the sides that can work and the sides that cannot. Some people have real values, some have false values and some have no values at all. It is the same with different “I”s; some value real things, some wrong things and some value nothing. People can spend their lives studying systems and system words and never come to real thing. Three-quarter or nine-tenths of our ordinary knowledge does not really exist; it exists only in imagination. #RandolphHarris 10 of 19

In October 1962, the Cuban missile crisis brought the World to the brink of nuclear war. The Soviet Union, under its mercurial leader Nikita Khrushchev, had begun to install nuclear missiles on Cuba, 90 miles from the American mainland. On tographs of missile sites under construction. After a week of tense discussions within his administration, on October 22 President John F. Kennedy announced a navel quarantine of Cuba. Had the Soviet Union taken up the challenge, the crisis could have escalated to the point of all-out nuclear war between the superpowers. Kennedy himself estimated the probability of this as “between one out of three and even.” However, after a few anxious days of public posturing and secret negotiation, Khrushchev shied away from the confrontation. In return for a face-saving compromise involving eventual withdrawal of U.S.A. missiles in Turkey, he ordered the Soviet missiles in Cuba dismantled and shipped back. Khrushchev looked over the nuclear brink, did not like what he saw, and pulled back. The name “brinkmanship” seems apt for the strategy of taking your opponent to the brink of disaster, and compelling one to pull back. (Many people erroneously say “brinksmanship”—which sounds more like the art of robbing an armored truck.) Kennedy’s action in the Cuban missile crisis is generally accepted as an instance of successful exercise of brinkmanship. The rest of us also practice brinkmanship, but with less than global stakes. #RandolphHarris 11 of 19

A management team and trade union facing a devastating strike, stubborn spouses whose failure to compromise is leading toward divorce, and a divided Congress risking a government shutdown if it fails to ratify a budget are all engaged in brinkmanship. They are deliberately creating and manipulating the risk of a mutually bad outcome in order to induce the other party to compromise. Brinkmanship is a subtle strategy fraught with dangers, and if you want to practice it successfully, you must first understand it thoroughly. We aim to help your grasp the subtleties, using the Cuban missile crisis as a case study. Upon discovering that the Soviets had secretly places missiles in Cuba, the Kennedy administration contemplated a range of options: do nothing, take a complaint to the United Nations (in practice, almost the same thing as doing nothing); impose a quarantine or blockade (the course actually adopted); launch an air strike on the missile sites in Cuba; or—at the extreme end—make an immediate preemptive total nuclear strike on the Soviet Union. After the United States of America imposed a navel quarantine, the Soviets had many possible responses. They could back down and remove the missiles; stop their ships carrying missiles in mid-Atlantic (the course actually adopted); try to run the blockade either without or with navel support; or take the extreme step of launching a preemptive strike on the United States of America. #RandolphHarris 12 of 19

In this spectrum of moves and countermoves, some of the possible actions were clearly safe (such as the United States of America doing nothing or the Soviet removing the missiles) while others were clearly dangerous (such as launching an air strike on Cuba). However, in the large middle range, where does safety end and danger begin? In other words, just where was the brink in the Cuban missile crisis? Was there a borderline such that the World was safe to the one side of it, and doomed as soon as the line was crossed? The answer, of course, is that there was no such precise point, only a gradually increasing risk of uncontrollable future escalation. Had the Soviets tried to defy the blockage, for example, the United States of America was unlikely to launch its strategic missiles at once. However, events and tempers would have heated up another notch, and the risk of Armageddon would have increased perceptibly. The key to understanding brinkmanship I to realize that the brink is not a sharp precipice, but a slippery slope, getting gradually steeper. Kennedy took the World some way down this slope; Khrushchev did not risk going father, and then the two arranged a pullback to the safe ground above. This this was the effect of Kennedy’s actions, it is at least plausible that it was also his intention. Let us examine the strategy of brinkmanship in this light. The essence of brinkmanship is the deliberate creation of risk. This risk should be sufficiently intolerable to your opponent to induce him to eliminate the risk by following your wishes. This makes brinkmanship a strategic move. #RandolphHarris 13 of 19

Like any strategic move, it aims to influence the other’s actions by altering his expectations. In fact brinkmanship is a threat, but of a special kind. To use it successfully, you must understand it special features. Governments rely increasingly on computer-stored data bases. While Sununu’s withholding of access to data is an example of ordinary info-tactics at work, subtle tampering with the data base is an example of meta-tactics. Meta-tacticians attack the data base not by controlling access to it, but by determining what may or may not be included in it in the first place. The ten-year census questionnaire used in the United States of America must be approved by Congress. Says a senior Census official: “Congress puts various pressures on us. We do a sample survey on farm finance. We’ve been directed by Congress not to collect that data because it might have been used to cut federal support for farmers.” Companies in every industry also pressure the Census Bureau to ask, or to avoid asking, certain questions. For example, it has been asked to include a question about mobile homes in its housing survey to supply data needed by a company in that business. Since the number of questions that can be included in the questionnaire is always limited, lobbyists fight one another and apply fierce pressure on the Bureau. No matter how computerized and seemingly “objective,” data baes thus reflect the values and power relationships of society. #RandolphHarris 14 of 19

Controlling what goes on into today’s endlessly multiplying data base is, however, only the simplest of meta-tactics. Far more subtle are attempts to control the way data are broken into categories or classes. Well before the computer era, at a time when the U.S.A. government was concerned about overconcentration in the auto industry, General Motors employed a lobbyist who sat in a little-known body, the Federal Statistics Users Council. His job was to assure that figures for the industry were lumped together so they could never be publicly disaggregated—thus, the degree of economic concentration might be given in terms of how large a share of the industry was controlled by the “top three” companies, but never by the top company alone—General Motors. Today, advanced systems are used to index, classify, and categorize the data flowing into computer data bases. With the help of computers the same data can be “cut” or recategorized many different ways. Thus, intense political battles are waged over more and more obscure, abstract, seemingly technical questions. Many power struggles take place over the indicators used in data bases and the relative importance assigned to them. If you want to know how many angels can dance on the tip of a warhead, do you count their haloes or their harps? #RandolphHarris 15 of 19

Hospital beds, which are easily counted, are sometimes presumed to be an indicator of the level of health services in a community. However, would the number of doctors per thousand residents be a better measure? Ans what do either of these reveal about the actual healthy of local residents? The number of beds may reflect government subsidy programs that reward or penalize hospitals based on bed-count, rather than on the provision of real services to the community. To get a true picture of the population’s health needs, should one count patients? Cures? Life expectancy? Infant mortality? The choice of an indictor or group of indicators will heavily affect the output. Meta-tacticians know the WYMIWYG Principle—What You Measure Is What You Get. Panels of experts, teams of government specialists, lobbyists, and others wrestle frequently with such questions. Whole some participants are not clever enough to ask deep-probing questions or to understand the hidden significance, others can and do. In so doing, they typically fight for their own commercial or departmental interest. While couched in highly technical jargon, the conflicts are often, in fact, strongly political. Most of this skirmishing takes place out of sight of the public, and well below the level of senior officials and Cabinet members, who rarely have the time or inclination to understand the hidden issues in any case. Lacking these and the training needed to cut through the barrage of facts and pseudo-facts themselves, decision-makers are forced to rely more on technical specialists. #RandolphHarris 16 of 19

The monitoring of more variables, plus the enormous jump in data processing capacity made possible by computers changes the problem facing political decision-makers from information underload to information overload. This overload also means that interpretation becomes more important than simple collection. Data (of varying quality) are plentiful. Understanding is rare. However, shifting the emphasis to interpretation means more processing at higher levels in the mind-work hierarchy. This alters power relationships among the experts themselves. It also shifts the info-tacticians’ playing field to a much higher, meta-level. A perfect example has to do with the latest satellite observation systems used to monitor U.S.A.-Soviet arms control agreements. Recently launched satellites deliver such a deluge of data—from their locations in space they can detect objects as small as a few inches—that interpreter drown in the flood. In the past the problems have been mostly connected with sensing the data. Now, they are more in filtering and interpreting it. The sheer volume threatens to overwhelm even armies of analysts, leading to pressures to automate the interpretation function. This, in turn, encourages a reliance on artificial intelligence and other “knowledge engineering” tools. However, their use raises the level of abstraction still further, and buries the critical assumptions of the system under still heavier layers of inference. #RandolphHarris 17 of 19

In business, corporations are looking to embed the inferencing capabilities of expert systems into their existing computer systems. Some 2,200 such expert systems are already opening in North America, doing everything from diagnosing factory tools that malfunction to analyzing chemical spills and evaluating applications for life insurance. Expert systems are spreading in government, too, where they have even been used by the FBI to help investigate serial murders. What this implies is a dependence on complex rules elicited from experts of various kinds, weighted, systematized, and installed in computers to support the making of decisions. We can expect the spread of similar technologies throughout government—including the political life itself, where decisions often have to be take on the basis of a mass complex, imprecise, cross-related, ambiguous facts, ideas, images, and proposals, and just plain deceits intended to produce power shifts. What these tools mean, however, is that the logic driving decisions is further “embedded” and, so to speak, invisibilized. Paradoxically, the very system that delivers clarifying information itself becomes more opaque to most of its end-users. This is no reason to avoid artificial intelligence and expert systems. However, it points to a deep process with important ramifications for democracy. #RandolphHarris 18 of 19

Politics were no purer in some earlier Golden Age. From China’s Lord Shang to the Borgias of Italy, those in power have always manipulated the truth to serve their needs. What is changing dramatically today is the level at which these mind-games are played. The World will face staggering new problems in the decades ahead—dangers of global ecological catastrophe, the breakup of longstanding military balances, economic upheavals, technological revolutions. Every one of these requires intelligent political action based on a clear apprehension of the threats and potentials. However, how accurate are the images of reality on which governments base their survival decisions? How accurate can they be when all the date and information on which they are based are vulnerable to repeated and invisible “meta-massage”? As countries have grown richer, their people have lived longer despite pollution and automobile accidents. Greater wealth means safer roads, safer cars, safer homes, and safer workplaces. Throughout history, new technologies have brought new risks, including risks of death, injury, and harm to the environment, but prudent people have only accepted new technologies when they are offered an improved mix of risks and benefits. Despite occasional dramatic mistakes, the historical record says that people have succeeded in choosing technologies that reduce their personal risks. This must be so, or we would not be living longer. Molecular manufacturing and its products should continue this trend, not as an automatic consequence, but as a result of continued, vigilance, of people exercising care in picking and choosing which technologies they allow into their daily lives. Nanotechnology will give better control of production and products, and better control usually means greater safety. Nanotechnology will increase wealth, and safety is a form of wealth that people value. Public debate, product testing, and safety regulations are standard parts of this process. #RandolphHarris 19 of 19

Cresleigh Homes

👍 Step 1 – Enjoy a delicious dinner with your guests!

👍 Step 2 – Escort them home with promises to do this again really soon.

👍 Step 3 – Throw In A Load Of Napkins And Tablecloths In The Laundry Room.

#CresleighRanch is made for entertaining! Our Residence 4 home at #MillsStation will fit you perfectly – we’re sure of it!

Don’t miss the final opportunity to purchase at Mills Station at Cresleigh Ranch.
Computer Output is Still Regarded as Gospel

Criminal behaviour is a topic that captures the attention of the average American. There is simply something about the darker side of human behaviour that peaks our interest. Consider the familiarity of the following scenarios. While involved in a manic run of high-speed channel surfing, an image of Charles Manson or Osama bin Laden suddenly flashes across the television screen. The image is gone as fast as it arrived and your eyes adjust to the next channel. Almost instinctively, you find yourself flipping back to the previous channel and you proceed to fixate upon what is being said about these individuals some people perceive as monsters of modern time. You are sitting alone in public place. Suddenly, you hear a nearby voice telling a friend how he broke the law the past weekend but presumes that he was lucky enough to evade suspicion…perhaps the person is describing how he filed a false tax return or got into fisticuffs at the local pub the night before. Your ears quickly perk up as you anxiously eavesdrop on the crime-related confessional. These anecdotes speak to the armchair criminologist that seems to exist in all of us. When we see or hear about criminal behaviour, we want to know more. When the topic comes up in conversation, we are always willing to add our proverbial two cents. Americans clearly have a healthy appetite for crime. Day in and day out, television viewers have a long list of reality-based/ crime drama network television shows (exempli gratia, SWAT, Chicago P.D., Criminal Minds, Blue Bloods, FBI, FBI International, FBI Most Wanted, CSI, X-Files, Law and Order, Law and Order SVU, Law and Order Organized Crime), or cable station documentaries (exempli gratia, Court TV, The Discovery Channel, A&E) from which to choose, as network executives scramble to quench our thirst for crime-related subject matter. #RandolphHarris 1 of 18

What is more, it is rare to find a front page of a newspaper or popular magazine that does not flaunt a crime-related story prominently in the headlines. Even mainstream lifestyle magazines, such as women’s Cosmopolitan and Glamour or their male equivalents, GQ and Maxim, now include regular features on “true crime.” Having established that crime sells, the obvious question becomes, Why? The answer is simple—we are feverishly attracted to that which we do not fully understand. Like a puppy chasing its tail, we spin around and around searching for ever-elusive answers. The average citizen is not alone in this ongoing quest for enlightenment. Year in and year out, legions of scholars, criminal justice practitioners, and politicians spend billions of dollars, kill millions of trees, and exhaust countless hours trying to understand, explain, and prevent the exorbitant amount of criminal behaviour that exists in today’s society. Just think about how much written and spoken commentary has ever been directed toward understanding the behaviour and mindset of modern terrorists such as Timothy McVeigh or Osama bin Laden! Efforts to describe and explain crime and criminality overload shelves with books, journals, and reports that details various theoretical and policy initiatives. What is the net gain of this sustained investigation? Or, have we made any substantial progress toward solving this problem? The harsh reality is that we as “learned professionals” have not made nearly as much progress as we would like; and we certainly have not made anywhere near as much progress as the general public expects. #RandolphHarris 2 of 18

Part of the problem with the criminological enterprise is that it is difficult to come to grips with the parameters of our substantive discussion and approach. First, one must address two fundamental questions: (1) What is the subject matter that we should be studying? (2) What is the best way to study it? Surely, coming up with an acceptable definition of crime should be enough. After all, crime is a routine topic in our daily conversations, it is a mainstay in media reports, and serve as a popular topic for books. However, upon closer examination, we see that “crime” is a relatively slippery concept. By crime do we mean all those acts or omissions of act that are defined by criminal law? Many sociologists consider this sort of legally bound definition of crime to be overly constraining. The “collective conscience” of society can be far more offended by non-criminal acts of deviance (id est, social norm transgressions) than it is by some violations of the law. For example, although it may not be illegal to shout racial lurs in public, there tends to be a much more resounding public outcry against this form of behaviour than there is when a minor law violation such as speeding or littering takes place. Many scholars acknowledge this point, but opt instead to pursue the path of least resistance—they contend that the subject matter in question should include only violations of the criminal law. This definitional parameter is convenient because it immediately limits the discussion to a much more identifiable and manageable set of behaviours. #RandolphHarris 3 of 18

More importantly, violations of the criminal law (id est, criminal act) are subject to formal, state-imposed sanctions, while violations of customs or norms (id est, deviant acts) are subject to informal, peer-imposed reprimands. This difference in the nature and process of social control efforts has long been seen as a critical issue that separates crime from deviance. The laws of the land are passed by a legislative body and recorded for dexterity purposes in a document knows as the criminal code. This is the document that police officers and prosecutors use to guide their daily activities. One must recognize, however, that a definition of “crime” that is based solely on existing criminal codes will still produce an exceedingly long list of offense. At the most basic level, one must content with the fact that there exists no single, definitive criminal code. Instead, each jurisdiction, ranging from the federal to the state to the thousands of local jurisdictions, has in place a slightly different criminal code that it calls its own. As such, an effort to compile an exhaustive list of every law violation that is currently “on the books” would result in a truly massive, unmanageable, and often conflicting list of criminal statutes. So let us assume that you could settle on a single criminal code, one from the federal, state, or local jurisdiction of your choice. Such a code would include high-profile offenses such as murder, rape, robbery, and theft. However, the complete list would be far more expansive, including thousands of law violations—everything from jaywalking to murder. #RandolphHarris 4 of 18

In addition, criminal codes routinely contain a host of obscure, outdated, and rarely enforced statutes. Seuling (1975) provides a long list of the more ridiculous examples, including: In Kansas City, Missouri, it is illegal for children to buy cap pistols, but not shotguns. Killing an animal with “malicious intent” can result in first-degree murder charges in Oklahoma. It is illegal to have a bathtub in your house in Virginia. Few people are willing to afford equal weight to all of the behaviours detailed in a given criminal code. Instead, one is inclined to set aside the “petty” and “outdated” offenses and focus the discussion on the more “serious” categories of crime. Most scholars follow suit Some turn to the Federal Bureau of Investigation Uniform Crime Reports (UCR) for direction. The UCR is an annual effort to document the number of reported and cleared (id est, a perpetrator has been identified) cases (and arrests) of murder, sexual assault, aggravated assault, robbery, burglary, larceny, auto theft, and arson that are encountered by the various law enforcement agencies across the United States of America. These eight offense types are called Part I offenses. The FBI asks all law enforcement agencies to provide host of offense and offender data tht are then used to generate descriptive crime statistics (exempli gratia, demographic profiles and crime rates). #RandolphHarris 5 of 18

The difficulty of keeping in touch with the social occasion while at the same time becoming spontaneously involved in situated engagements is often reduced by the arts of concealment. Apparently one of the most significant involvement shields is that afforded by a conversational circle itself. In fact, there seem to be few conversational clusters in which control of facial and bodily expression is not employed to conceal either a deadness to the content of the encounter or an improper drift from the spirit of the occasion. A conversation occurring within a situation, then, is likely to present something of a collusion against the gathering at large; Mrs. Toplofty’s multiplication tables, previously cited, are merely an extreme instance. And yet, of course, the very possibility that conversational content can be shieled from the gathering as a whole removes some of the threat that such smaller circles might have for the larger inclusive one if the drift or deadness were open and visible. We can thus appreciate why some “informal” sociable gatherings are deemed “successful” when each cluster carries away its participants to the point where they can barely conceal their departure. The possibility of sustaining a concealed activity within conversations can become somewhat recognized and institutionalized, so that two different phases of a social occasion can simultaneously occur in the same place among the same participants, one phase being restricted to unfocused interaction and the other to matters that can be parceled out to conversations and concealed in them. #RandolphHarris 6 of 18

One phrase is likely, then, to be defined as dominant and the other subordinate. For example, in Lincoln, California it was obligatory for male neighbours and male extended kin to attend funerals dressed quite decorously in black, even to the point sometimes of wearing a black cap reserved only for such occasions. It was also obligatory for these male mourners to stand quietly and sedately outside of the cottage in which the deceased was laid out. However, while thus standing, it was quite permissible to carry on entertaining conversational chats with one’s fellow-mourners. To be sure, the sound level of these talks and the features of the talkers were respectfully modulated to fit funeral requirements, but the content of the talk went in another direction. In some cases it was even understood to be in bad taste to turn the topic from the ordinary pleasantries of neighbourly talk to the deceased; attendance and funeral garb were what one owed the other present. The involvement shield provided by a conversation is somewhat portable, because the participants can together move about a room and take their talk with them. Perhaps the most important recently developed portable shield for encounters is the automobile. The protection provided by the back seat has already made social history, and use of the front seat in drive-in movies has become a kind of inadvertent outdoor shrine for paying homage to our society’s use of shielding arrangements. #RandolphHarris 7 of 18

Mutual-involvement has been treated simply as one variety of situated involvement; the rules regulating situated involvements apply, in fact, with extra force. There are differences, however, between mutual-involvements and other kinds. For one thing, mutual-involvements improperly maintained by the individual necessarily involve others directly; further, of all objects of involvement, other individuals seem to be the most enticing and hence, in turn, the most in need of social control. However, further issues are also to be found. An unengaged individual may easily exhibit the kind of involvement which gives others the impression that one is indeed in a pathological state; the same consequence, however, is rarely possible for persons improperly involved together. Except for the very marginal phenomenon of folie a deux (or a trois, a quatre, etcetera), it seems to be assumed that as long as two individuals are in communication with each other—as long as they are joined in an encounter—whatever they are doing is not occult, however esoteric and opaque it may appear to be. This helps to explain why a person who is “with” another tends to feel free to engage in all kinds of antics, since one can assume one’s contact with the other will guarantee one’s sanity to bystanders. A parallel phenomenon has been observed in connection with the frame of reference by which criminality is imputed (as opposed to mental illness). Apparently there are depredations which can be interpreted as a game when committed by a group of youths, but which are viewed as crime when committed by a solitary offender. #RandolphHarris 8 of 18

Let us speak about the relation of false personality to other parts of man. In every man at every moment, his development proceeds by what may be called a static triad. This triad is called aa static triad because body, soul, and essence always stay in the same place and act as the neutralizing force, while the other force change only very slowly. So the whole triad is more or less in the same place all the time. There is Body, Soul, Essence at the top of the triangle, the “I” and the left, and False personality at the right. The first triangle forms the state of man in ordinary life; the second forms his state when he begins to develop. There are long period between the state of the first and the state of the second triangle, and still longer between them and the third triangle. Actually, there are many intermediate stages but these three are sufficient to form the way of development in relation to false personality. It is necessary to remember that none of these states is permanent. Any state may last for about half an hour and then another state may come, then again a different state. The triad is made by the body, the soul and the essence at the apex. At the second point if “I”; that is, the many “I”s which are the person, that is to say, all feelings and sensations which do not form a part of false personality. The third point of the triangle is held by false personality (id est, the imaginary picture of self). In an ordinary man false personality calls itself “I”, but after some time, if a man is capable of development, magnetic center begins to grow in one. #RandolphHarris 9 of 18

One may call it “special interests,” “ideals,” “ideas,” or something like that. However, when one begins to feel this magnetic center in one, one finds a separate part of oneself, and from this part of one’s growth begins. This growth can take pace only at the expense of false personality because false personality cannot appear at the same time as magnetic center. If magnetic center is formed in a man one may meet a school, and when one begins to work one must work against false personality. This does not mean that false personality disappears; it only means that it is not always present. In the beginning it is nearly always present but when magnetic center begins to grow it disappears, sometimes for half an hour, sometimes even for a day. Then it comes back and stays for a week! So all our work must be directed against false personality. When false personality disappears for a short time, “I” becomes stronger, only it is not really “I,” it is many “I”s. The longer the periods for which false personality disappears, the stronger the “I” composed of many “I”s becomes. Magnetic center may be transformed into deputy steward, and when deputy steward acquires control of false personality it really transfers all the unnecessary things to the side of false personality, and only the necessary things remain on the side of “I.” Then, at a still further stage, it may be that permanent “I” which will come on the “I” side with all that belongs to it. Permanent “I” has quite different functions, quite a different point of view from anything we are accustomed to. #RandolphHarris 10 of 18

The static triad shows that either personal work or degeneration is going on in relation to different manifestations of false personality, but that body, soul, and essence remain the same all the time. After some time they too will be affected, but they do not enter into the initial stages. Body will remain the same body, essence will change later, but it does not enter the beginning of the work. According to this system, essence enters only as much as it is mixed with personality. We do not take it separately because, as already explained, we have no means of working on essence apart from personality. “What is it,” someone asked, “that makes the real ‘I’ begin to develop and false personality to fade?” First of all it is a question of time. Say false personality in ordinary life is there for twenty-three hours our of every twenty-two hours only and magnetic center will be present for an hour longer than usual. Then, in time, all false personality will diminish and will become less important. (This is shown in the second stage of the where false personality has become passive and the man “I”s surrounding magnetic center have become active.) You cannot diminish false personality in the sense of size but you can diminish it in the sense of time. Somebody else said, “I had the impression until now that false personality was the collection of all the many ‘I’s. This concept has made things a little obscure to me.” Among these many “I”s there are many passive “I”s which may be the beginning of other personality. #RandolphHarris 11 of 18

False personality cannot develop; it is all wrong. That is why I said that all work has to be against false personality. If one fails it is because one has to be against false personality. If one fails it is because one has not given enough attention to false personality, has not studied it, has not worked against it. False personality is made up of many “I”s and they are all imaginary. “I do not understand what you mean by passive ‘I’s.” “I” which are controlled by some other, active “I.” For instance, good intentions are controlled by laziness. Laziness is active, good intensions passive. The “I” or combination of “I”s in control is active. The “I”s which are controlled or drive are passive. Understand it quite simply. There are three different states of man beginning from the most elementary. In the most elementary state false personality is active and “I” is passive. Body, soul, and essence always remain neutralizing. When, after many stages, permanent “I” comes, then “I” becomes active, many “I”s become passive and false personality disappears. Many different examples can be drawn between these two extremes, and further than that there are several possibilities. In 1944, the Allies were planning an operation for the liberation of Europe, and the Nazis were planning their defense against it. There were two possibilities for the initial landing –the Normandy beaches and Pas de Calais. A landing would surely succeed against a weak defense, so the Germans would have to concentrate their attention on one of these two places. Calais was more difficult to invade, but more valuable to win, being closer to the Allies’ ultimate targets in France, Belgium, and Germany itself. #RandolphHarris 12 of 18

The payoffs are given on a scale of 0 to 100. The Allies count a successful landing at Calais as 100, a successful landing at Normandy as 80, and a failure at either place as 0 (and the Germans get the negative of these payoffs). Put yourself simultaneously in the boots of General Eisenhower, the Allied Supreme Commander, and Field Mashal Rommel, the German commander of their coastal defenses in France. What strategies would you choose? There is no equilibrium in the basic strategies, and we must look for mixtures. Allies should choose to land at Normandy or Calais with the odds of (100-20): (80-60), or 4:1, while the Germans should deploy their defenses at Normandy or Calais with the odds (80-20): (100-60), or 3:2. The average point score for the Allies when both use their best mixture is 68. The probabilities and point scores we chose are plausible, but it is hard to be precise or dogmatic about such matters. Therefore let us compare our results with what actually happened. In retrospect, we know that the Allies’ mixing proportions were overwhelmingly weighted toward Normandy, and that is what they in fact chose. For the Germans, it was a closer call. It is less surprising, therefore, that the German decision-making was swayed by the Allies’ double-agent trick, differences of opinion in their commanding ranks, and some plain bad luck, such as Rommel being away from the front at the crucial time. They failed to commit their reserves on the afternoon of D-Day when the Allied landings at Normandy seemed to be succeeding, believing that a bigger landing at Calais would come. Even then, the fate of Omaha Beach was in the balance for a while. However, the Allies gained and consolidated their foothold on Normandy. The rest you know. #RandolphHarris 13 of 18

When it comes to voter fraud, the vulnerability is not just inside the computers, or at election times, but in the way computer-generated data, information, and knowledge are used and misused. Smart politicians and officials, of course, do what smart people in general have always done when presented with new information. They demand to know more about its source and the reliability of the data behind it; they ask how samples were drawn in polls and what the response rates were; they note whether there are inconsistencies or gaps; they question statistics that are too “pat”; they evaluate the logic, and so forth. Smarter power players also take into account the channels through which the information arrived and intuitively review in their minds the various interests who might have “massaged” the information in transit. The smartest people—a minority of a tiny minority—do al the above, but also question assumptions and even the deeper assumptions on which the more superficial assumptions are based. Finally, imaginative people—perhaps the fewest of all—question the entire frame of reference. Government officials are found in all four categories. However, in all the high-tech countries they are so harried, so pressured, that they typically lack the time and attention span, if not the brains, to think past the surface “fact” on which they are pressures to make decisions. Worse yet, all bureaucracies discourage out-of-frame thinking and the examination of root premises. Power-players take advantage of this fact. #RandolphHarris 14 of 18

When David Stockman , who headed the U.S.A. Office of Management and Budget, proposed budget cuts to the President and White House staff, he carefully chose the reductions from programs accounting for only 12 percent of the total budget. In discussing these cuts with high higher-ups, he never provided context. Telling tells out of school, he later wrote: “What they did not realize—because I never made it clear—was that we were working in only a small corner of the total budget. We hadn’t even looked at three giant programs that accounted for over half of the domestic budget: Social Security, veterans’ benefits, and Medicare. Those three alone cost $250 billion per year.” (As of 2023, that figure is $1.8 trillion per year.) “The projects we had cut saved $25 billion. The President and White House staff were seeing the tip of the budget iceberg; they were not finding out about the huge mass which lurked below the waterline. No one raised any questions about what wasn’t being reviewed.” Were they willfully ignorant, too much in a hurry to ask or blinded by Stockman, a master of statistical legerdemain? Or were they just “snowed” by all the computer-generated numbers? A political speech is barely worth making these days unless it is stuffed with computer-derived statistics. Yet most decision-makers seldom question the numbers that have been crunched for the. Thus Sidney Jones, a former Under Secretary of Commerce, once proposed setting up a Council of Statistical Advisers to serve the President. Presumably they would have been able to tell the President how the notorious “body count” statistics during the Vietnam War were being massaged. #RandolphHarris 15 of 18

Or why the CIA and the Pentagon could not agree on how powerful Soviet nuclear tests were, and therefore on whether or not the U.S.S.R. was violating the Threshold Test Ban Treaty of 1975. Or why the Commerce Department figures on gross national output were wildly exaggerated at one time, then corrected down to show the economy in a near-recession. The reasons in every case were highly technical—but they were also, inevitably, political. Even the most objective-seeming numbers have been hammered into shape by the push and pull of political power struggle. The U.S.A. Census Bureau takes more pains than most agencies to make public its definitions and statistical procedures so that users can form their own judgments about the validity of its figures. Its top experts readily admit, however, that such reservations and footnotes are routinely ignored in Washington. Accord to one Census staffer: “The politicians and the press do not care. All they say is ‘Gimme a number!’” There are two reasons for this. One is mere naivete. Despite all we have learned in the past generation about the spurious quality of much seemingly hard computer data, according to the Census official responsible for automatic data processing and planning, “Computer output is still regarded as Gospel.” However, there is a deeper reason. For political tacticians are not in search of scholarly “truth” or even simple accuracy. They are looking for ammunition to use in the info-wars. Data, information, and knowledge do not have to be “accurate” or “true” to blast an opponent out of the water. #RandolphHarris 16 of 18

Some truisms: Almost any technology is subject to use, misuse, abuse, and accident. The more powerful a technology is when properly used, the worse it is likely to be when abused. Any powerful technology in human hands can be the subject of accidents. Nanotechnology and molecular manufacturing replaces modern industry, and if its nanotechnological products replace most modern technologies, then most future accidents will have to involve nanotechnology. Another truism: In a diverse, competitive World, any reasonably inexpensive technology with enormous commercial, medical, and military applications will almost surely be developed and used. It is hard to envision a scenario (short of the collapse of civilization) in which nanotechnology will not make its appearance; it seems inevitable. If so, then its problems, however tough, must be dealt with. Like trucks, aircraft, biotechnology, rockets, computers, boots, and warm clothes, nanotechnology has the potential for both peaceful and aggressive uses. In peaceful uses (by definition), harm to people occurs either by accident or as an unintended consequence. In aggressive uses, harm is deliberate. In a peaceful context, the proper question to ask is Can fallible people of goodwill, pursuing normal human purposes, use nanotechnology in a way that reduces risk and harm to others? In an aggressive, military context, the proper question to ask is Can we somehow keep the peace? Our answer to the first will be a clear yes, and to the second, an apprehensive maybe. #RandolphHarris 17 of 18

Throughout this discussion, we assume that most people will be alert in matters concerning World safety. During the 1970, people awakening to the new large-scale, long-term problems of technology was out of their control, in the hands of shortsighted and irresponsible groups. Today, there are still battles to be fought, but the tide has turned. When a concern arises regarding a new, obvious technology, it is now much easier to get a hearing in the media, in the courts, and in the political arena. Improving these mechanisms for social vigilance and the political control of technology is an important challenge. Current mechanisms are imperfect, but they can still give a big push in the right directions. Though we assume alertness, alertness can be a scarce resource. The total amount of concern and energy available for focusing on long-term problems is so limited that it must be used carefully, not squandered on problems that are trivial or illusory. Part of our aim is to help sort out these issues raised by nanotechnology so that attention can be focused on problems that must be solved, but might not be. For instance, fresh fruits, vegetables, meat and poultry products are potential vehicles for the transmission of human pathogens leading to foodborne disease outbreaks, which draw public attention to food safety. Therefore, there is a need to develop new antimicrobials to ensure food safety. Because of the antimicrobial properties of nanomaterials, nanotechnology offers great potential for novel antimicrobial agents for the food and food-related industries. The use of nano-antimicrobial agents added directly to foods or through antimicrobial packaging is an effective approach. As a result, the use of nanotechnology by the food and food-related industries is expected to increase, impacting the food system at all stages from food production to processing, packaging, transportation, storage, security, safety and quality. #RandolphHarris 18 of 18

Cresleigh Homes

Welcome to the neighborhood! 👋

We’re thrilled to meet newcomers to the #Havenwood community. Ideally located in the charming city of #Lincoln just down the street from Palo Verde Park.

Not a neighbor yet? Find out more on our website! https://cresleigh.com/havenwood/quick-move-homesite-67/

A Richter-8 Earthquake is Waiting to Happen in California!

Creativity may assume many different forms. It might at times be saturnine, so that a bout with depression, for example, might be understood as a particularly creative time. Brooding generates its own style of awareness and its own brand of insight, and out of depressive moods important elements of culture and personality can emerge. Some people’s interpersonal relationships are profound because they trust more, empathize and associate more with other person than the typical person, they seem to develop greater love. They are able to disclose themselves to others and break down the barriers that we all build up. Their love is warm and comfortable, seldom clinging and possessive. They have many acquaintances and casual contacts, but usually a small, select circle of deep friendships. They tend to select friends who exhibit similar traits. It has been suggested that those in an accessible encounter are obliged to keep their activity in tune with the ethos of the social occasion, being obliged to exhibit within the situation a degree of occasioned mood and involvement. However, it was also implied that each accessible encounter will properly carry its participants some distance from the mood prevailing in the situation. Indeed, should this fail to occur, the social occasion may be blamed for failing to provide a setting in which individuals can be brought into face engagements and caught up spontaneously in them. In the latter case, the encounter may have to draw on the standard supplies of the social occasion for all of its sustenance. #RandolphHarris 1 of 19

Similarly, if an individual fails to let go of one’s concern about the gathering as a whole or the progress of the occasion enough to be caught up in a situated engagement, it may be felt one has failed to give oneself up to the social occasion. A nice balance is thus required between keeping in step and stepping lively. Of special interest in this connection is the phenomenon of drift. Jut as a social occasion as a whole is likely to manifest an “involvement contour,” carrying all of its encompassed encounters in a developing direction, so each particular encounter can manifest dynamic properties of its own, not only generating a World for its participants but carrying them further and further into it. It is this movement of drift of individual encounters away from the gathering at large and its social occasion that we shall now consider. Given the presence in a social situation of different face engagements—different clusters of persons engaged exclusively together in a talk, a game, or a joint task—how far may the participants of any one of these little circles allow their mutual involvement to carry them from the other persons in the situation? The problem of drift can perhaps be seen most clearly in those social occasions where a fairly high pitch of some kind of affect is defined as appropriate. This, at a wedding it is not proper for any cluster of individuals to become too serious or to quarrel in any way; obviously this would be out of keeping. Should a quarrel start, it must be quickly checked lest it carry the encounter past the range of variation permitted. #RandolphHarris 2 of 19

Similarly, in the case of funeral visits, knots of people not containing any of the immediately bereaved may begin a quiet chat, but find themselves getting gayer and gayer until their interaction becomes out of place and must be brought back to the sober tone of the surroundings. Drift, of course, occurs not only at ceremonials. Thus, in a surgery observed, the nurses scrubbing at the four scrub sinks just before the medical staff arrived would carry on the light sociable chatter that seemed fixed to the sink area. Sometimes, however, their talk would become louder and louder, more and more boisterous, until the charge nurse of the ward would have to come into the scrub area and shush them. So, too, there were moments when the anesthetist and his helper began a whispered conversation that carried them further and further away from the occasion, until a point was reached where the surgeon or the surgical nurse glanced up and across the barrier between operating field and anesthetic equipment with a look of amusement, wonderment, or disapproval, which was often followed by a “cutting back” of the drifting conversation. In considering the tendency for accessible encounters to drift, we should not overlook other problems of affective movement. During occasions such as social parties, wakes, and other celebrations, a mood of hilarity or sadness or grimness ma begin to develop, and soon may carry all participation units away from their emotional starting point. (Sometimes this developing contour of involvement may be assisted by means of pharmacological agencies such as spirits.) #RandolphHarris 3 of 19

When all the encounters in a situation begin to drift at the same time in the same direction, they may together move past the point of propriety implicit in the social occasion. It is thus that an etiquette manual can warn that liquor at a christening should not be of the kind to turn into a cocktail party. A second issue may be mentioned. When a social occasion has taken hold of its participants, and the engagements occurring within it have together moved in a particular affective direction, a latecomer to the occasion may find oneself out of step affectively with the prevailing mood and may have difficulty in catching up, in “getting with it.” A sober person coming to an inebriated gathering can have quite the same problem, and create the same offense, as an inebriated person arriving at a still sober occasion. Wakes are of special interest here, because persons longest on the spot will have “worked through” some of their affective concern about the deceased, while at the same time they are likely to have been the “closet” to the individua and to be therefore held most responsible for giving a worthy show of grief. A latecomer may find a certain callousness among those present, which they may in turn be forced to conceal b a kind of recapitulation of the mourning process performed within the confines of the face engagement in which the latecomer is welcomes to the place of mourning. #RandolphHarris 4 of 19

“Does our capacity for work increase just so much as we are able to weaken false personality?” Everything one can get, one can get only at the expense of false personality. Later, when it is not present, one can get many things at the expense of other things, but for a long time one has to live, so to speak, off false personality. “Is false personality the main barrier to being aware?” First of all, yes. However, many mechanical habits besides. Sometimes even mechanical habits in other centers. “If you could eliminate false personality…” someone began. You cannot eliminate anything; it is just the same as trying to cut your head off. However, you can make false personality less insistent and less permanent. If at a certain moment you feel the danger of the manifestation of false personality and you can find a way to stop it, this is what you have to begin with. The question of elimination does not enter at all; that is connected with quite different things. You must learn to control manifestations. However, if people think that they can do something and at the same time refuse to work on acquiring this control, then things become bad for them. People can be enthusiastic about what they have to do until they know what they have to do. When they know, they often times become very negative and try to avoid it or explain it in some other way. #RandolphHarris 5 of 19

This is what you must understand—that false personality defends itself. You must understand, too, that you cannot even begin to work such as you are, on your present level. First you have to change one thing or another thing. However, you can only find out what to change as the result of your own observations, and it is different for different people. Sometimes it becomes quite clear what has to be changed and then the fight begins, because false personality defends itself. In order to struggle with false personality always do something which false personality does not like and you will very soon find out what it does not like. If you continue, it will get more and more irritated and will show itself more and more clearly, so that soon there will be no question about it. However, if you can do nothing to check false personality, it grows. It cannot diminish by itself. Tastes may change and so on, but it grows. This is the only development that happens in mechanical life—nothing else. “Repression of the life force” is a diagnosis and it would fit most emotional problems. Throughout human history, the expression of individuality has been felt as a threat to the status quo. For all its expressed championing of the individual, our culture in many ways favours conformity. At each stage of live, there seems to be a necessity for choice. In the choice between staying at the level of safety and going onto the level of loving, the easiest choice is of safety, because it has already been experienced and is “known.” Loving and belonging involves a lot of risk. They involve putting oneself on the line, out on the limb of initiative. And that is scary! #RandolphHarris 6 of 19

Notion of copying are central both to biology and to computer science, two disciplines that have contributed enormously to complex systems research. These two traditions do not have identical notions of copying, and the differences between them are reflected in our framework. The biological approach to making copies is much closer to our discussions of selecting at the level of agents. For most agent copying, material resources have to be assembled, and copies are made using the same materials that constitute the copied agents. By contrast, copies as conceived in computer science concentrate on preservation of abstract form. This view corresponds more closely to our discussions of selection at the level of strategies. This alternative view of copies reaches an impressive level of abstraction in binary-encoded information that preserves its essential character across arbitrary embodiments. A digital recording of a Bach fugue is a series of “ones and zeros” that can be represented as spots of magnetism, pits in an optical disk, or a series of voltage pulses or light waves. Both notions of copy have a place in our framework because the way copies spread through a Complex Adaptive System does not always conform to the patterns seen in natural selection. There can be adaptation, but through patterns that are not necessarily like those seen in biology. It was once thought that a computer virus could spread much faster than a successful physical virus. However, we have learned that both a physical virus and a computer virus, within hours, can infect thousands of humans and computers all over the World with copies of itself. #RandolphHarris 7 of 19

Therefore, physical viruses and computer viruses are very similar with respect to both time and space. Being immaterial, it can spread incredibly rapidly, and it can spread though a space in which “nearby” machines are physically far away. A Complex Adaptive System framework needs to encompass much more than the biological cases, even if those have provided much of its inspiration. Just as the difference between copying strategies and agents matters, so too do the detailed differences among various copying processes. Imitating someone’s method for making telephone charity requests is not an identical process to passing along a photocopy of a fund-raising letter. Both involve copying, but the former involves far more integration of a pattern into one’s own behaviour. Setting an example that trigger imitation is very different when the population comprises nation-states than it is when the population is made up of schoolyard playmates. By calling many different processes “copying,” it has not been out intention to deny the important differences of detail. Indeed, details have to be studied very closely. Errors and recombining processes depend on those details. And the character of the variation in the system is shaped by them in turn. Making fund-raising calls using your friend’s method is much more of a recombination of strategies than is photocopying and forwarding of a funding request. #RandolphHarris 8 of 19

While the detailed character of copying processes is of great significance, it is also important to discuss coping processes in the aggregate. That makes clear the deep similarities among Complex Adaptive Systems. Our aim in discussing “copying” in general is to guide designers and policy makers to ask questions about how copies are made, and how destruction happens, for the agents and strategies in the systems they work with. We want to simulate the recognition of many different kinds of processes as “copying,” from duplicating computer files to replicating fast-food franchises. Once copying mechanisms are identified, the questioner will have knowledge of the important details that we cannot have. In this way, the framework aims to suggest fruitful questions. Why would someone want to copy the visible behavior of a leader? In the ambiguous and hard-to-predict World of a Complex Adaptive System, agents often do not know what criteria of success they should use or how to evaluate the strategies they could select. This is especially important in an age of uncertainty and rapid change. When adaptive agents live in a rapidly changing environment, they tend to look to other agents to see which performance measures tend to work and which ones tend to fail. When agents are not able to predict the effects of various possible behaviour of agents who seem to be successful, or who at least have more experience with the new environment. Imitating others who are successful or experienced is a form of implicit attribution of credit that certainly has its disadvantages. #RandolphHarris 9 of 19

When features that are copied are only superficially relevant, the results can be wasteful or even comical. Nevertheless, following the practices of those with more experience or success is often a good strategy in an uncertain World. There are three basic reasons a leader in a formal organization or other social system is especially likely to be copied. First, a leader can sometimes set standards that provide incentive for others to copy. Second, a leader’s actions or performance measures are typically seen to be successful and hence worth emulating. Third, a leader may set an example that helps establish beneficial norms in a community. Leadership in setting a standard can cause other to go along for their own reasons. Consider the case of Norway as a country that writes much of the World’s maritime insurance. When the standards body in Norway set certain regulations for insuring oil platforms, the makers of oil platforms had an incentive to build in ways that met those standards. Thereafter other marine insurers tended to gravitate toward similar regulations. Norway’s regulations helped shape the industry in ways that led other maritime insurers to copy their visible behaviour. The emulation of a leader need not be based on a full understanding of how the emulation will help. Other agents may wish to emulate the actions or performance measures of a visibly successful leader in the hopes that what worked for the leader will work for them. #RandolphHarris 10 of 19

A business leader who wishes to promote environmentally friendly production can, of course, make decisions that give high weight to environmental concerns. However, if the firm is highly visible and is able to show that it becomes more successful because of its environmental practices and reputation, then a much more powerful dynamic comes into play. Imitation of the firm’s performance measures by other firms creates a cascade that can transform an industry. Many forms of inspirational leadership work in this same fashion. For example, Dr. Martin Luther King, Jr.’s criterion of nonviolence was advanced throughout the World by the success its practitioners achieved in winning Civil Rights in America. Dr. King’s leadership was successful in large part because he visibly embodied the very values he was advocating. This led others to emulate not only his tactics but also his values. Visible leadership can also be exercised by setting an example that helps establish beneficial norms in a community. In Complex Adaptive Systems, norms are often important regulatory mechanisms. Central monitoring and control can be difficult when many agent interactions are widely distributed across physical or social alternative. Especially when they become internalized, norms regulate not through fear of consequences but through the belief that some actions are right and others wrong. This is extremely important when monitoring by central authorities is costly or intrusive. Moreover, once established, a norm can be reinforced and spread by dispersed agents who accept the norm and are willing to punish others who deviate from in. #RandolphHarris 11 of 19

The Internet is a vast example of opportunities for one agent to exploit another from afar. The eventual character of its culture will be established in large measure by decisions made in the next few years, as significant and highly visible leaders promote the norms they will exemplify and expect others to enforce. The major providers of e-mail and chat facilities provoke widespread debates when they announce or modify positions on how they will handle unwanted advertisements or offensive language. The dialogs that occur build communities of users who may well enforce standards among each other more effectively than central authorities could hope to do. It is very important, in business, and life to build networks of reciprocal interaction that foster trust and cooperation. Also, people take on big ideas, like ending corruption. However, it is best to look for shorter-term, finer-grained measures of success that can usually stand in for longer-run, broader goals. For instance, building a wall at the Southern Boarder, would not only fortify national security, but it would also be a form of immigration reform, save lives of patrol agents, reduce costs of court cases, and housing, weed out crime, and decrease voter fraud. Then one can move on to another segment of ending corruption. There has to be a coherent approach to designing interventions in a complex World. We all must intervene in Complex Adaptive Systems daily. We all face situations where the classical approach of formulating alternative actions and their likely consequences assume more understanding and predictive power than we actually have. #RandolphHarris 12 of 19

Our framework shows how the accumulating scientific insights into variation, interaction, and selection fit together and can be used to harness complexity. However, why are there so few instances of businesses using randomized behaviour out in the real World? First, it may be difficult to build in the idea of leaving the outcome to chance in a corporate culture tht wants to maintain control over the outcome. This is especially true when things go wrong, as they must socially when moves are chosen randomly. While some people understand that a football coach has to fake a punt once in a while in order to keep the defense honest, a similarly risky strategy in business can get you fired if it fails. However, the point is not that the risky will always work, but rather tht it avoids the danger of set pattens and predictability. One application in which mixed strategies improve business performance is price couponing. Companies use price discount coupons to build market share. The idea is to attract new customers, and not just to give a discount to your present market. If competitors simultaneously offer coupons, then customers do not have any special incentive to switch brands. Instead, they stay with their current brand and take the discount. Only when one company offer coupons while the others do not are new customers attract to try the product. The price coupon strategic game for competitors such as Coke and Pepsi is then quite analogous to the coordination problems of Sarah and William. Both companies want to be the one to give coupons. However, if they try to do this simultaneously, the effects cancel out and both are worse off. #RandolphHarris 13 of 19

One solution would be to follow a predictable pattern of offering coupons every six months, and the competitors could learn to alternate. The problem with this approach is that when Coke predicts Pepsi is just about to offer coupons, Coke should step in first to preempt. The only way to avoid preemption is to keep the element of surprise that comes from using a randomized strategy. There is some strong statistical evidence that Coke and Pepsi reached a cooperative solution for their couponing. There was a span of 52 weeks in which Coke and Pepsi each offered 26 price promotions and there was no overlap. The chance that this would occur by luck if the two companies were acting independently and each offered 26 weeks of couponing is 1/495918532948104—or less than 1 in 1,000 trillion. There are other case in which businesses must avoid set patterns and predictability. Some airlines offer discount tickets to travelers who are wiling to buy tickets at the last minute. However, they will not tell you how many seats are left in order to help you estimate the chances of success. If last-minute ticket availability were more predictable, then there would be a much greater possibility of exploiting the system, and the airlines would lose more of their otherwise regular paying customers. The most widespread use of randomized strategies in business is to motivate compliance at a lower monitoring cost. This applies to everything from tax audits to drug testing to parking meters. It also explains why the punishment should not necessarily fit the crime. #RandolphHarris 14 of 19

The typical fine for illegal parking at a mete is many times the meter fee. If the meter rate is a dollar per hour, would a fine of $1.01 not suffice to keep people honest? It would, provided the traffic police were sure to catch you each time you parked without putting money in the meter. Such enforcement would be very costly. The salaries of the traffic wardens would be the largest item, but the cost of administering the collection mechanism needed to keep the policy credible would be quite substantial, too. The authorities have an equally effective and less costly strategy, namely to have larger fines and relax the enforcement efforts. When the fine is $25, a 1 in 25 risk of being caught is enough to keep you honest. A much smaller police force will do the job, and the fines collected will come closer to covering the administrative costs. This is another instance of the usefulness of mixed strategies. In many ways, it is similar to the tennis example we used in the past, but it is also different in some respect. Once again, the authorities choose a random strategy because it is better than any systematic action: no enforcement at all would mean misuse of scarce parking places, and a 100 percent enforcement would be too costly. However, the other side, the parking public, does not necessarily have a random strategy. In fact the authorities want to make the detection probability and the fine large enough to induce the public to comply with the parking regulations. #RandolphHarris 15 of 19

Random drug testing has many of the same features as parking meter enforcement. It is too time-consuming and costly to test every employee every day for evidence of drug use. It is also unnecessary. Random testing will uncover those who are unable to work drug free and discourage others from recreational use. Again, the probability of detection is small, but the fine when caught is higher. That is one of the problems with the IRS audit strategy. The penalties are small given the chances of getting caught. When enforcement is random, it must be that the punishment is worse than the crime. The rule should be that the expected punishment should fit the crimes, where the expectation takes into account the chance of being caught. Those hoping to defeat enforcement can also use random strategies to their benefit. They can hide the true crime in the midst of many false alarms or decoys, and the enforcer’s resources become spread too thin to be effective. For example, an air defense must be able to destroy nearly 100 percent of all incoming missiles. A cost-effective way of defeating the air defense is for the attacker to surround the real missile with a bodyguard of decoys. It is much cheaper to build a decoy missile than the real thing. Unless the defender can perfectly distinguish among them, one will be required to stop all incoming missiles, real and fake. The practice of shooting dud shells began in World War II, not by the intentional design of building decoy missiles, but as a response to the problem of quality control. #RandolphHarris 16 of 19

The elimination of defective shells in production is expensive. Someone got the idea then of manufacturing duds and shooting them on a random basis. A military commander cannot afford to have a delayed time bomb buried under one’s position, and one never knew which was which. The bluff made one work at every unexploded shell that came over. When the cost of defense is proportional to the number of missiles that can be shot down, attackers can make this enforcement cost unbearably high. This problem is one of the major challenges facing those involved in the “Star Wars” defense; it may have no solution. In Seoul, South Korea, in December 1987, after sixteen years of military rule, a general election took place. The results of this bitterly fought three-way contest were ultimately accepted and the country got on with its business. However, in the immediate aftermath, political observers noted certain peculiarities in the balloting. The winner’s percentage of margin, established in the earliest returns, remained strangely unchanged throughout the night and across regions. A highly popular opposition candidate cast doubt on the size of his own victory in Kwangju Province, saying he could not believe that he had actually garnered 94 percent of the votes. At best, he claimed, he should have won a maximum of 80 percent. The suspicion grew that someone was tampering not with the ballot boxes, but with the computers that complied the results. This suspicion was never confirmed, but it would have been extremely easy to draw up a computer model of an acceptable decision result. This could be adjusted for people’s perceptions of voter choice, regional, class, and age background, and events during the campaign. Such a model could design the size of the majority. #RandolphHarris 17 of 19

Such a model could also, presumably, be used to tailor the results so subtly in key districts as to provide a victory without leaving an overt trail. This is possible if a sophisticated programmer, gaining access to the right password, instructs the computer to credit some percentage of the votes of one candidate to another and then to spring a “trapdoor”—which, in effect, erases any record of what has been done. The Election Watch project of the Urban Policy Research Institute, basing itself in part on work done by two Princeton University computer scientists, Jon R. Edwards and Howard Jay Strauss, concludes that “the advent of computerized vote counting over the past two decades has created the potential for election fraud and error on a scale previously unimagined.” Therefore, it looks like President Donald Trump was right about voter fraud and being cheated out of the election. Many current election officials disagree, but Election Watch gains support from Willis H. Ware, a senior researcher at the Rand Corporation. Ware puts it even more dramatically: The vulnerability of electronic voting systems is such that “there is probably a Chernobyl or a TMI [Three Mile Island] waiting to happen in some election, just as a Richter-8 Earthquake is waiting to happen is waiting to happen in California.” Given these admittedly speculative scenarios a further twist. Imagine what might be done if the computer were “fixed” by technicians, programmers, or systems integrators working for a multinational corporation that wants a particular senator, say, driven from office. #RandolphHarris 18 of 19

Or imagine that the election ballot box is under the indirect, secret control not of a party or corporation but of a foreign power, which may suspect is that case with the Democratic Party and President Biden, California Governor Newsom, and Sacramento Mayor Steinberg. An election, may have been swung by adding or subtracting a tiny—unnoticed—number of votes from each precinct. And no one ever knows because they refuse to investigate, make claims seem outlandish by calling a person crazy or saying it is a conspiracy theorist. Caveat Candidate! With all the corruption, crimes, health crisis, energy crisis, inflation, food costs, housing costs, and changes in employment, along with the wide open boarders, and riots on the streets in America, the average person is feeling what it means to suffer from future shock. People have not even had a chance to catch their breath because there is so much going on in the nation and around the World. However, when more nanotechnology arrives, will it bring more future shock? Some segments of society today are already getting practice in dealing with rapid technology advance. Those getting the most vigorous workout are in the computer field, where a machine two years old and regarded as obsolete, and software must be updated every few months to keep abreast of the new development. The rapid increase of computer speed had helped make computers easier to use. Some people will learn to adapt to technology, but in the future technology will learn to adapt to us. The most effective government and private agencies will endure. More options will continue to be invented. #RandolphHarris 19 of 19

Cresleigh Homes

Get ready for the ultimate indoor/outdoor lifestyle at #CresleighRanch #MillsStation! 🌳 🏡

Residence 2 is calling your name – lay your head on your own pillow in the airy, spacious bedroom.

Homesite #104 is ready for new owners!

The Owner’s bathroom is spacious and tranquil including a large free standing soaking tub, walk in shower and large walk-in closet.

Don’t miss on the last chance to purchase the Residence Two at Mills Station.

What Do You Mean By Crystallizing?

The soul needs an intense, full-bodied spiritual life as much in the same way the body requires food. Each person defines beauty, spiritual life, love, pleasure, pain and all the other experiences in a way that makes sense for them. Human beings are tremendously influenced by many things in the cultural experiences. The restrictions against exposed mutual-involvements can sometimes be seen not as a restriction against involvement that withdraws the participants from gathering. Indeed, the individual may at times be obliged to open oneself up for mutual-involvements, as implied in the rule of accessibility. However, one must do this not merely on the grounds of prior relationship but on the basis of the present occasion. (Here we catch another glimmer of the trouble caused by newlyweds or those deeply engaged in courting, who, unlike persons whose relationship is more settled and seasoned, find it awkward to give up their mutual-involvement for the kind of courtesy involvement with a sequence of others that the social occasion often requires.) Thus we find a special kind of exemplary situational conduct when two persons with a long-standing, exclusive relationship manage to treat each other at a sociable gathering with courtesies owed on the basis simply of participation in the occasion; two bitter enemies show a similar regard for the occasion by being “civil.” The same type of courtesy is exhibited by a teacher who addresses her child in class as though he or she were just another student, this being describable not merely as role segregation but also as a gesture of regard for the occasion. #RandolphHarris 1 of 17

Interestingly enough, in the natural history of some social parties, certain forms of fleeting play involving pleasures of the flesh may be a sign that the spirit of the occasion has lifted everyone up with it, not that the party has collapsed into separate pieces. Indeed, should the interactions involving pleasures of the flesh occur between persons brought together only at and for the occasion, it may be a sign of the high degree to which participants have given themselves over to the gathering. The extreme of this, in fact—for example, the kind of interaction involving pleasures of the flesh said to occur at the annual Beaux Arts ball in Paris—can represent not a collapse of duties in regard to the situation, as might at first seem the case, but rather some kind of profane worship of them. Were husbands to engage their wives in this manner, the obligations to the occasion would indeed be threatened. In noting the rule obliging individuals to sustain an occasioned mutual-involvement, we have perhaps a better means of accounting for our response to improper involvements than for predicting actual conduct, for these situational niceties are often ill-sustained. Resistance to the spirit of an occasion, as expressed in a refusal to sustain occasioned mutual-involvements, is apparently so useful a device for conveying so many things that someone in a gathering can usually be counted on to employ it. At public dances in the chief city of Utah, for example, one could usually find a slightly resented handful of couples, solidly middle-class in social status, who withheld themselves from the plebeian pleasures sustained by second-generation crofters. #RandolphHarris 2 of 17

This alienation was expressed by dancing in half-time to the vigorous music and sustaining quiet engrossing talk while doing so, conduct that was obtrusively out of mood with the prevailing ethos. We see, then, that there will be ties when the success of a social occasion such as a party is expressed through the success of a social occasion such as a party is expressed through the success of the participants in finding congenial encounters in which to engross themselves. This engrossment provides proof that each person present is a desirable companion, and that each finds the social occasion significant enough to provide one with grounds for opening oneself up to others. Given these assumptions, we can understand that a person caught for too long between encounters—caught “unengaged”—may cause anxiety to oneself and the hostess, and that the latter may try to anchor one in a convenient port, which particular port being of only secondary significance. And we can also understand why an individual may feel that what one owe the gathering at large can at times override what one owes oneself and one’s fellows in an encounter, providing us with additional evidence that the individual’s engagement in a focused interaction is a fact available to all others in the situation, and hence a part of the unfocused interaction in the situation. Here we have the situational reason for one type of tact, namely, giving the appearance of being spontaneously involved in some occasioned encounter when in fact one is not. #RandolphHarris 3 of 17

Even if you are placed next to some one with whom you have had a bitter quarrel, consideration for your hostess, who would be distressed if she knew you have been put in a disagreeable places, and further consideration for the rest of the table which is otherwise “blocked,” exacts that you give no outward sign of your repugnance and that you make a pretense, at least for a little while, of talking together. At dinner once, Mrs. Winchester, finding herself next to a man she quite openly despised, said to him with apparent placidity, “I shall not talk to you—because I do not care to. But for the sake of my hostess I shall say my multiplication table. Twice one are two, twice two are four—” and she continued on through the tables, making him alternate them with her. As soon as she politely could she turned again to her other companion. Another instance of the obligation to sustain an occasioned involvement with others may be cited from Utah. At a “progressive” whist of twenty tables during a social, the deep engrossment of a member of the gentry in his particular table of whist was likely to be taken as a sign of how thoroughly he was participating in the social occasion. By getting caught up in the spirit of one of the tables, he showed regard for the room as a whole. Had he disdained to invest himself thus, and insisted on wandering from one table to another, making gracious comment to players at all the tables in turn, he might well have tendered the common folk—the crofters—less of a compliment. (And yet if an ordinary crofter became so much involved in a particular hand of whist as to delay appreciably the finishing time for his table, this disregard for the necessity of shifting tables at the end of each game was likely to be considered an affront to the whole social occasion.) #RandolphHarris 4 of 17

If social occasions can be assessed according to their capacity to bring all participants into one occasioned encounter or another, then we can expect that rules will be found obliging those within any encounter to admit entrants. (This corresponds to the previously discussed obligation of the individual to make oneself accessible, the difference being that while an individual may be inaccessible to others because of organic capacity, this excuse is hardly available to encounters.) There are many occasions, as on public streets, where those in an encounter need acknowledge few rights of other to enter. One the other hand, as already suggested, it I characteristic of occasions such as social parties that participants have a right not only to initiate face engagements but also to enter ones that are already in progress. Here participants, in order to demonstrate how thoroughly they have been lifted up and brought together by the party, may feel obliged to admit newcomers to their conversation easily. “Open” topics of conversation may thus be maintained in preparation for newcomers. A conversation that by its tone forbade the entrance of new members would be improper. Consequently, we can understand the strategy sometimes employed by those who would converse about intensely involving private matter in a public place: instead of huddling together in a furtive conspiratorial way, they affect a style of matter-of-fact openness. [Somebody spoke about a useless personality which she enjoyed although she knew that it was useless.] In such a case you can struggle with this personality by strengthening other personalities opposed to it. #RandolphHarris 5 of 17

Suppose you have a certain definite feature you want to struggle with, and try to find some other feature incompatible with it and which may be useful. If in your present equipment you find nothing sufficiently strong to put against it, look in your memory. Suppose you find some feature that is incompatible with the one you want to get rid of, and that can be useful, then just replace one by the other. However, it may happen that even then they can both live happily together. One may present in the evening, the other in the morning, and they may never meet. There is only one real danger. If, for a long time, one goes on without making sufficient efforts or without doing anything seriously, then, instead of becoming one, one becomes divided into two so that all features and personalities are divided into two group—one part useful to the work and helping personal work, and another part either indifferent or even unfriendly. This is a real danger because if two parts begin to form like this, the indifference of one spoils the result of the work of the other. So it is necessary to struggle very quickly and very strongly against that, otherwise it may lead to double crystallization. “What do you mean by crystallizing?” We use the word in a particular sense. Any feature may become crystallized just as buffers crystallize. This term came from the theosophical terminology; it is sometimes a useful term. I think everybody here has heard about higher bodies, the astral, mental and causal. The idea is that man has only one physical body, and development consists in the development of higher bodies. #RandolphHarris 6 of 17

So man no. 5 corresponds to the crystallization of the astral body, man no. 6 to the crystallization of the mental body, and man no. 7 to the crystallization of the causal body. However, speaking of the crystallization of features, one person may have very good and very beautiful features and yet behind them he may have one small feature of false personality which makes work very difficult for him, more difficult perhaps than it is for somebody else who has not got such brilliant features. False personality may pretend to take an interest in the work, may take things for itself and call some negative and mechanical action “self-remembering” or something of that sort. However, it cannot do any useful work; it can only spoil the work of personalities which can do some work and get some results. The system in the light of false personality is quite a different system; it becomes something that strengthens false personality and weakens the real system for you. The moment false personality takes the system to itself, it adds one word here and another word there. You cannot imagine how extraordinary some of these ideas are when they are repeated back to me. One word omitted from some formulation makes quite a different idea; and false personality is fully justified and can do what it likes and so on. The problems of inferring proper lessons (attributing credit) based on limited experience occur in almost every sphere of human activity. #RandolphHarris 7 of 17

Because military organizations only rarely obtain feedback from actual combat, their circumstances make adaptation especially difficult. Since credit attribution has long been so problematic in warfare, military organization have a rich history of refining various forms of simulation, including many forms of gaming and field exercises. The techniques used by the military to cope with the problems of credit attribution when feedback is scarce are therefore particularly illuminating. For these organizations the problem of determining what works well is especially vexing. Large-scale fighting is infrequent—and much work goes into keeping this true. That means that opportunities to try new weapon systems or tactical concepts, or to test officer capabilities, come rarely. Learning only from real combat experience is an unacceptably slow strategy for improvement. This is a price society happily pays for peace, but it leaves military organizations facing a difficult learning problem. Where a firm might have several different versions of a consumer product tested in the field within a few months, a military organization might not accumulate the equivalent amount of useful experience in several decades. For n extreme example, there has never been any full combat experience for our intercontinental ballistic missile hardware, operational concepts, and crews. (This field is the only branch of science where success is achieved by never having any data.) A large portion of what military organizations learn about new technology and operational concepts must come from various forms of experience. #RandolphHarris 8 of 17

This experience may be war games, field exercise, small-scale engagements, mental experiments, computer models, or even imaginative reconstructions of military history. The Information Revolution is providing computer tools that dramatically expand simulation possibilities. The United States of America military now routinely employs simulated aircraft, tanks, ships, and soldiers in its investigations of combat possibilities. Mobilizations of large forces for field exercises incur substantial resource costs, and even without live ammunition, there are inevitable injuries and deaths from the risky movements of personnel and heavy equipment. Such exercises cannot be repeated many times in minor variation of multiple factors may reveal large consequences. The value of these new possibilities is also becoming evident in the business World. Although useful experience is not as scarce as in the military case, there are many situations in which exploratory trials with the real system are not possible, Major reorganizations or changes of corporate strategy are like this. They often have huge costs, and if they do not work, they risk the bankruptcy of the entire firm. In response to this need, simulation tools for business decision making are beginning to appear. Firms are arising that specialize in building such simulation models. Some are spin-offs of computer gaming companies, while others have arisen from consulting practices. There are limitations, of course. One shortcoming is that simulations often place sharp and arbitrary limits on improvisation. #RandolphHarris 9 of 17

While it is an extremely important source of military and business innovation, improvisation is generally not realistically supported in computer simulations, which often insist that the “players” obey rules and constraint that in real activities they might decide to violate. Although they may fall short of realism in significant ways, computer simulations provide the kind of rapidly assessed measure of success we have discussed previously. They generate only surrogate experience, but they can improve learning in an experience-poor domain if they are used wisely, with clear attention to their limitations. So far, our applications of randomized strategies have focused exclusively on games in which the players’ interests are strictly opposed. Somewhat more surprising is the possibility of finding an equilibrium with random behaviour even when the players have common interests. In this case, mixing one’s plays leads to an inferior outcome for all parties. However, just because the outcome is inferior does not mean the strategies are not an equilibrium: equilibrium is a description not a prescription. The reason for mixing one’s moves arises from a failure of coordination. This problem only arises when there is not a unique equilibrium. For example, two people disconnected during a phone call do not always know who should call back. Without the ability to communicate, the players do not know which equilibrium to expect. In a loose sense, the equilibrium with randomization is a way of playing a compromise between the coordinated equilibra. #RandolphHarris 10 of 17

Sarah and William are the sort of couple you read about in fiction, O. Henry’s The Gift of the Magi, to be precise. “Nobody could ever count” their love for each other, and each was willing, even eager, to make any sacrifice to get a really worthy Christmas gift for the other. Sarah would sell her hair to get Willian a chain for his heirloom watch, and William would sell the watch to buy a comb for Sarah’s beautiful hair. If they know each other well enough, they should both reorganize the possibility that each will sell his or her one treasure to buy the other a gift, and the result will be a tragic mistake. Sarah should pause and consider whether it would be better to keep her hair and await William’s gift. Likewise, William should consider not selling his watch. Of course, if they both refrain, neither gives a gift, which would be a different mistake. The couple’s strategies interact even though their interests largely coincide. For each, both kinds of mistake would be a bad outcome. For concreteness, we give this a point of score of zero. As between the two outcomes in which one gives a gift and the other receives it, suppose each thinks it better to give (2 points) than to receive (1 point). The situation in which Sarah keeps her hair and William sells his watch is possible equilibrium; each spouses strategy is the best response to the other’s. However, the situation in which Sarah sells her hair and William keeps his watch is also an equilibrium. Is there a mutually understood convention to select one equilibrium over the other? Surprise is an important aspect of a gift; therefore they cannot communicate in advance to establish a convention. #RandolphHarris 11 of 17

Mixing can help preserve the surprise, although at a cost. It is easy to check that the strategies in which each chooses to give with probability 2/3 and receive with probability 1/3 also constitute an equilibrium. Supposed Sarah uses such a mixture. If William sells his watch, there is a 1/3 chance that Sarah has kept her hair (2 points) and a 2/3 chance that she has sold it (0 point). The average outcome is 2/3 point. A similar calculation shows that if William keeps his watch, the average outcome is again 2/3 point. So William has no clear reason to choose one strategy rather than another, or indeed any mix. Once again, note that the function of Sarah’s best mix is to keep William willing to mix, and vice versa. The probabilities of mistakes are quite large: 4 times in 9 the couple finds that each has sold the item for which the other has bought the gift (an in the O. Henry story), and 1 time in 9 neither gets any gift. Because of these mistakes, the average score (2/3 point for each) is worse than that of either of the two equilibra in which one gives and the other receives (2 points for the giver and 1 for the receiver). This is unlike the tennis example from the past, in which each could actually raise one’s success rate by mixing. Why the difference? Tennis is a zero-sum game, in which the players’ interests are strictly opposed. They do better when they choose the mixing probabilities independently. #RandolphHarris 12 of 17

In our account of The Gift of the Magi, the couple’s interest are largely aligned. They need, therefore, to coordinate their mixing. They should toss one coin, and depending on the outcome decide who gives and who receives. The couple has a slight conflict of interest; William prefers the top left outcome, and Sarah the bottom right. Coordinated mixing can offer them a compromise, splitting the difference. When a common coin toss decides who gives and who receives, the average outcome for each becomes 1.5 points. Of course the element of surprise is lost. Major shift in demographics always cause disruptions. Even when we know they are coming, we never prepare for them. Our plans are based on expectations of what will happen. If things do not go as expected, we find that we have “malinvested.” Huston real estate was valuable and looked to become even more so when times were good for the oil business there; when the fortunes of the oil business changed, Houston real estate was found to have been overbuilt, overpriced, and many millions of dollars were lost. Lengthening life spans push people toward taking a longer-term perspective, but rapid rates of change force a shorter-term perspective in investments. Turbulence in technology and in governmental monetary policy have already shortened time horizons. Businesspeople once routinely built plants with a thirty-year useful life. Today, the rate of change is so fast, and uncertainty regarding inflation and potential changes in tax laws is too great for such investments to make sense. Faster change will shrink time horizons further. #RandolphHarris 13 of 17

Governments have taken on themselves the burden of looking a lifetime ahead, and the Social Security Administration is in for some rough times. When Otto von Bismarck, Germany’s Iron Chancellor, came up with the notion of a guaranteed old-age pension, it was a cynically clever and low-cost way to gain popular goodwill. So few people lived to age sixty-five that the amounts paid out in pension were a pittance. After watching the German experiment for a handful of years, other governments began following suit. None of them expected a World likes ours where a baby girl born in the United States of America today has an average life expectancy of 82 years—more than double that of Bismarck’s time—and even this estimate is based on the faulty assumption that her medical care will be no better than her great-grandmother’s was. At present, the Social Security Administration has two models: one they call “positive” and one they call “negative.” In the “positive” model, people work like slaves until old age, retire, and promptly die—presumably before they have had a chance to collect substantial social-security or medical benefits. In the “negative” model, people retire early, develop illnesses that require medical intervention, and then live a long time making doctor visits and hospital stays during those years. Plans based on these models deserve to be disturbed. A better, more realistic scenario would have people living and able to support themselves for a long time, with illnesses that can be handled easily and inexpensively. Present social-security are enough to provide a certain standard of living—food, housing, transportation, and so forth. In a future of great material wealth, these benefits will be easy to provide, and present projections of economic woe resulting from an aging population seem quaint. #RandolphHarris 14 of 17

A rapidly accumulating international literature tells lurid stories about computer crime—about bank swindles, espionage, viruses sent from one computer to destroy the contents of others. Movies like WarGames have dramatized the dangers from unauthorized entry to the computer and communication systems that control nuclear weapons. According to a published report in France, the Mafia has kidnapped an IBM executive and cut off his finger because it needed his fingerprint to breach a computer security system. The U.S.A. Department of Justice has defined a dozen different methods used in computer-based criminal activity. They range from switching or altering data as they enter the computer, to putting self-concealing instructions into the software, to tapping the computers. Widely publicized cases of “computer viruses” have illustrated the potential for sabotage of military and political communications and computation. However, relatively little thought has been given so far to the ways in which similar techniques might alter political life. One day in 1986, Jennifer Kuiper, a staff aide of Congressman Ed Zschau, saw her computer screen go blank. When she got her machine up and running again, two hundred letters had disappeared. Four days later hundreds of letters and addresses disappeared from the computer of Congressman John McCain. Capitol Hill police, claiming to have eliminated the likelihood of staff error, launched criminal investigations. #RandolphHarris 15 of 17

According to Zschau, himself, the founder of a computer software firm before entering politics, “Every office on Capitol Hill can be broken into in this way…It can bring the work that a member of Congress does to a complete halt.” With 250,000 word processors being used in the offices of American lawyers, it becomes feasible for a lawyer’s unscrupulous opposing counsel to glean compromising information by illegal access to his or her computer—and that this can be accomplished with inexpensive electronic equipment purchasable in the corner of Radio Shack. Politicians and officials, however, may be even more vulnerable. Thousands of computers, many of them linked in networks, are now found in congressional offices, the homes of elected officials and lobbyists, as well as on the desk tops of hundreds of thousands of civil servants who regulate everything from soybean quotas to air travel safety standards. Unauthorized and secret entry could cause endless troubles and shift power in unexpected ways. Computers also increasingly populate election campaign headquarters. Thus new, virtually undetectable games can be played in the ballot box itself. As you know, voter fraud is real. For example, an Iowa woman was arrested 12 January 2023, in Sioux City for her role in an alleged voter fraud scheme during the Iowa 2020 primary and general elections. Kim Phuong Taylor, 49, of Sioux City allegedly perpetrated a scheme to generate votes in the primary election in June 2020, when her husband was an unsuccessful candidate for Iowa’s 4th U.S.A. Congressional District, and subsequently in 2020 general election, when her husband was a successful candidate for Woodbury County Supervisor. #RandolphHarris 16 of 17

Taylor allegedly submitted or caused others to submit dozens of voter registrations, absentee ballot request forms, and absentee ballot containing false information. For instance, although these documents required the singer to affirm that he or she was the person named in them, Taylor singed them for voter without their permission and told other that they could sign on behalf of relatives who were not present. Taylor is charged by indictment with 26 counts of providing false information in registering and voting, three counts of fraudulent registration, and 23 count of fraudulent voting. If convicted, she faces a maximum penalty of five years in prison for each count. Secure elections are the cornerstone of a thriving republic. A key priority for any Attorney General is to investigate and prosecute the increasing allegations of voter fraud to ensure election integrity within the United States of America. In Texas, since 2005, the office of the Attorney General successfully prosecuted election fraud offense against 155 individuals, out of 534 cases suspected. The number of pending offenses against 43 defendants is 510, and currently pending prosecution. There 386 case of active election fraud investigations in Texas. Voter fraud is a reason so many people are demanding Voter ID laws are employed and enforced. However, the objection is that millions of Americans lack ID. In fact, 11 percent of U.S.A. citizens—or more than 21 million Americans—do not have government-issued photo identification. The enforcement of voter ID laws is considered to be discriminatory because obtaining an ID costs money. Even if ID is offered for free, voters must incur numerous costs (such a paying for birth certificates) to apply for a government-issued ID. The combined cost is estimated to range from $75 to $175. However, not requiring voter ID is consider a national security threat. #RandolphHarris 17 of 17

Cresleigh Homes

Welcome to the neighborhood! 👋

We’re thrilled to meet newcomers to the #Havenwood community. Ideally located in the charming city of #Lincoln just down the street from Palo Verde Park.

Not a neighbor yet? Find out more on our website!

#CresleighHomes
To Be Alive is to Face Risks!

Life is often a struggle. The characteristics of humanistic psychology are directly related to our view of human nature. Man’s own best interests, viewed in the light of a full understanding of his nature, are the criteria for the study and application of humanistic psychology. The first thing that interests us in understanding the essential self is what makes us go. By testing and trying himself out with all the limits of the human condition, man comes to some understanding of what he can and cannot do. This enables him to arrive at some acquired pattens of thought, attitude, and action, giving him a sense of safety or security. He has learned how to stand, what falling feels like, what staying up feels like, and, in the healthy child, a preference for the feeling of staying him. Far from being forced to grow up, the child who is growing in healthy terms, who has “made it” in the sense of acquiring a homeostatic balance of needs and tension-reductions, literally jumps at the chance to move up to the next stage. Those who were kept at a level of satisfaction and need-reduction become bored, fatigued, resentful. It is part of the biological nature of the person to seek continuing growth. Homeostasis moves up, then, from the biological drive to a learned need at each level, following a pattern: discover a need, motive or deficit, find a goal or incentive that will meet the need, and enjoy the satisfying tension-reduction for a period of time. Then it is time to move on to another field, for a different “ball game,” of the same kinds of processes. There is a level of care a one is obligated to exert for an accessible encounter past civil inattention to the question of how an when one can present oneself for official participation. #RandolphHarris 1 of 21

Even at social parties, where every encounter is supposed to be conducted in a fashion that makes it joinable by any guest, the entrant is expected to exert tact, and when cues suggest, not exercise one’s rights. When one does enter, one is expected to accept the current topic and tone, thus minimizing the disruption one causes. If a lady and gentleman are conversing together at an evening party, it would be a rudeness in another person to go up and interrupt them by introducing a new topic of observation. If you are sure that there is nothing of a particular and private interest passing between them you may join their conversation and strike into the current of their remarks; yet if you then find that they are so much engaged and entertained by the discussion that they were holding together, as to render the termination or change of its character unwelcome, you should withdraw. If, however, two persons are occupied with one another upon what you guess to be terms peculiarly delicate and particular, you should without yourself from their company. Welcome or not, the entrant today is usually expected to knock at the door of the encounter before one enters, thus giving the encounter advance warning of one’s intention and the participants a moment to straighten their house for the newcomer. One of the most interesting forms of cooperation in the maintenance of conventional closure is what might be called spacing. The term “individual distance” was introduced to describe the tendency of birds on a fence or railing to stay a particular distance from each other, the distance apparently varies with the species. #RandolphHarris 2 of 21

The term “flight distance” refers to the closeness with which an individual of a given species can be approached before taking flight. However, one should give caution against cross-cultural generalization. In the U.S.A., we distribute ourselves more evenly than many other people. We have strong feelings about touching and being crowded; in a streetcar, bus, or elevator we draw ourselves in. Toward person who relaxes and lets oneself come into full contact with others in a crowded place we usually feel reactions that could not be printed on this page. It takes years for us to train our children not to crowd in on us, and allow of to have some room to breathe. In Latin America, where touching is more common and the basic units of space seem to be smaller, the wide automobiles make in the U.S.A. pose problems. People do not even know where to sit. In America, the tendency for units of participation in the situation—either face engagements or unengaged individuals—to distribute themselves cooperatively in the available space so as physically to facilitate conventional closure. (Often this seems to involve a maximization of the sum of squares of the physical distance among the various units. Spacing will of course ensure that “talk lines” are open, that is, that persons addressing one another in an encounter will have no physical obstruction to block the free exchange of glances. A bystander finding oneself interposed in such a line (in America society, at least) is likely to offer an apology and quickly shift one’s position. #RandolphHarris 3 of 21

While the phenomenon of spacing may be difficult to see because one takes it for granted, a tracing of it in reverse can be obtained by observing children and mental patients—those communication delinquents who sometimes play the game of “attack encounter.” On many wards, for example, a patient will follow a pair of talkers around the room until they have stopped moving, and then sidle right up to the edge of the encounter and lean into it. One adolescent patient I studied would intercept talk lines between two persons by waving her knitting needles in the way, or by swinging her upraised arms, or by thrusting her face into the face of one of the participants, or by sitting in his lap. Along with physical spacing, we also find control of sound so that the various units in the situation can proceed with their business at hand without being jammed out of operation. In many cases this will mean restriction on the volume of sound, although, at rare occasions like social parties, where persons may be crowded close to others not in the same encounter, a general raising of voices may be found; this allows coparticipants to hear each other, but jams the opportunities of eavesdroppers. Here, too, accurately designed delicts can be observed, as when an adolescent mental patient, in a spirit of fun, places her face up against the face of someone engaged in talk with another at a distance, and then shouts so that one can neither hear nor be heard. #RandolphHarris 4 of 21

The requirement that visually open talk lines be maintained, and that sound levels not interfere with neighbouring encounters, sets a limit to the distance over which spoken encounters can ordinarily be sustained. For example, should two persons carry on a conversation from one end of a crowded streetcar to the other, all the intervening passengers would have to remain out of the line of talk and modulate their own conversation so as not to jam the one being maintained over a distance. Such a conversation would necessarily also be fully available to everyone between the two speakers, and would therefore be likely to constitute an embarrassment, even were one of the speakers the conductor. Thus, engagements that must be carried on over such a populated distance are likely to be limited to the exchange of silent gestures, for these neither interfere with other encounters nor expose what is being conveyed. As might be expected, therefore, deaf and dumb persons who board a streetcar together and find themselves seated apart need not discontinue their exchange of messages, but are able to carry on conversation as long as sight lines are clear, their “talk” neither jamming the other talkers nor being accessible to them. #RandolphHarris 5 of 21

While physical spacing and sound control certainly have relevance to occasions such as social parties that are carried on within a relatively small physical region, they are perhaps even more important in public streets and roads and in semipublic regions. In Western society, the development of middle-class dominance is expressed in the rise of a relatively equalitarian use of public places. Even today, however, funerals, weddings, parades, and some other ceremonials are allowed to press their spirit momentarily upon the public at large. Technical units, such as ambulances, police cars, and fire engines cut through public traffic; and guests of a city may be given a motor escort. Some of these prerogatives, however, are but small remnants of practices that were once more general, such as the entourage and train associated with “clientage,” which led a worthy to demonstrate one’s status by the cluster of dependent supporters that accompanied one through a town or a house of parliament, shouldering one’s way for one wherever one went. Nor are these rules uniform within Westerns society, as is suggested by the response of King Edward (of Britain) and his party during a 1906 visit to the Emperor of Germany: The Emperor had a standard attached to his motor and a trumpeter on the box who blew long bugle-calls at every corner. The inhabitants thus had no difficulty in making out where the Emperor was, and all the traffic cleared out of the way when they heard the trumpets blow. The King, however, detested what he called “theatrical methods” and drove about like anybody else. #RandolphHarris 6 of 21

There can sometimes be a kind of restructuring that can occur when a situation is transformed from one containing many encounters—a multifocused situation—to one that is exhausted by a single all-encompassing engagement. For example, at noontime on award of Central Hospital, when the attendant shouts, “Chow time!” he is addressing the whole place, and wherever the sound level of his voice reaches, the meanings of his words are meant to carry too. Similarly, at a small social party, the arrival of a couple may cause the hostess to interrupt the separateness of all the separate encounters in order to introduce the newcomers to the assembly. So also, at formal dinners, the moment the hostess indicates that the conversation will be “general,” she opens up whatever is being said to all the guests. And, of course, whenever public speeches are given, the speaker’s words, as well as the heat with which one speaks them, are meant to impinge on the situation at large. In all such cases, there is the understanding that the situation at large. In all such cases, there is the content of the words of an appropriate single speaker; one has, as we say, the floor. The transformation of a multifocused situation into one that is exhausted by one face engagement is an interesting process to consider. At social parties we can observe a singer or guitar player make an effort to incorporate more and more of the room’s population into one’s audience, until a point is reached where one’s singing officially exhausts the chamber, and the party is momentarily transformed into a performance. #RandolphHarris 7 of 21

At the same time, as a particular encounter comes to include a larger and larger number of persons, side involvements increasingly occur in which a subordinate byplay is sustained, sometimes furtively, its volume and character modulated to allow the main show to prevail unchallenged as the dominating one. In mental hospitals there is a special kind of “symptomatic” behaviour that takes recognition of how the situation as a whole can be “talked to.” Many patients talk to someone, present or not, in a voice loud enough for everyone in the situation to hear and be somewhat distracted. However, those on the ward implicitly distinguish this kind of impropriety from that which occurs when a patient “addresses the situation,” haranguing everyone present in a tone and direction of voice that suggest one is purposely breaching the barriers designed to render clusters of talkers and game players safe in their own focused interactions. (Interestingly, although the actual volumes of sound may be greater in the case of a patient insufficiently modulating one’s contribution to a private conversation than in the case of a patient “addressing the situation,” it is the latter that is likely to cause the greater disturbance.) Attacks on the situation should be compared with the attacks on encounters, previously mentioned, which children, mental patients, and other communication delinquents perform. #RandolphHarris 8 of 21

Many middle-class parents in our society have experienced times when their children, forbidden to interrupt or even to enter a room where adults are talking, stealthily stalks the situation in self-conscious mimicry of stealthiness and stalking, resulting in much more disturbance to the gathering than one’s mere presence might entail. When it comes to constructive criticism, it is best to make a fault seem easy to correct. First off, do not start by discouraging an individual. Be honest, and see the potential they have and use those optimistic characteristics to guide them in the right direction. This will prevent an individual from feeling like a failure and give them the hope that they too can become the highest, the most exalted one. Tell your parents, child, spouse, or employer that one is stupid or dumb at a certain thing, has no gift for it, and is doing it all wrong, and you will have destroyed almost every incentive for improvement. However, when being liberal with your encouragement, making the things seem easy to do, letting the other person know that you have faith in one’s ability to do it, that one has an undeveloped flair for it—and one will practice until they are the brightest planet in the sky. Give confidence, inspire others, help one find the courage and strength that they have been endowed with. For instance, there is nothing to preparing for an exam except memory and judgement. Also, if you are going to be a successful student, you have to learn to read, and you have to actually read and gain a great understanding of the English language. #RandolphHarris 9 of 21

Going to college is great, but one will not succeed unless you start reading in high school. Reading is so important. So much of education can only be mastered by reading the material. If you are not going to read your books, and be prepared for lectures, there is no point in going to school. Many young minds are bright, but they are undisciplined. And, I know you may think TV is the most important thing, but those shows will all be there later. You can even binge watch them over Summer vacation. Take the time to study and get your homework done with a military like focus. Find a quiet room, and get busy. You are a potential genius. Sometimes school systems see surgical scars on students and incorrectly assume that they are injured and cannot function at a normal level. Even if you are a few years being in your age group, find a peer who is willing to help bring you up to speed. Every time you study, you are expanding you mind. You will notice the more you do it, the more understanding of the subject you gain, and eventually it will take you less time to absorb the muscle. It is a lot like cars. They start off cold, but gradually warm up. You can never get into a car, smash on the gas and go at top speed, it will ruin the engine. However, taking breaks it also important. If you are on a long haul in your vehicle, do not just suddenly smash on the gas, that can also mess up the engine. And just like a car, you do not want to overload your brain and burn out. #RandolphHarris 10 of 21

Naturally, the more you study, the more your grades will increase. No one is stupid. You notice that as early as four weeks old that many babies have the ability to form short sentences, and some even start walking at 7 months old. That is because they are smart. However, some need more practice and education to achieve these milestones, but they all get there. Also, as you learn the enrichment curriculum, you will notice that your other natural talents will develop and others will start to notice them. You can really learn and accomplish things. Do not let income/inequality be an excuse as to why you cannot succeed. I have seen poor kids grow up and become richer than students who had the World handed to them. Most cities have a public library where you can go and read books of interest. Social media is not as important as you think. So many people want to become famous for doing things that may not be in their best interest, but you can use your brain and become an auto science engineer or a tennis player. Maybe one day you will be elected in the national honour society. Once you find learning is easy, you whole life will change. Also, sometimes you make need to read a chapter in a book twice. Once to get a feel for the subject, and a second time to grasp the concepts being discussed. Eventually, reading will become easier and you will be able to read a chapter once. Also, to become an excellent writer, you need to read. Communication is so very important in any field of work you will go into. Just remember, faults are easy to correct. #RandolphHarris 11 of 21

Some people wonder whether one can do anything by oneself or whether it must be done with the help of others. Testify as to why you are superior and demonstrate it through your actions. When one tells people what should be done, they usually begin to argue, and not only argue but they become negative. That is really why help cannot be given, and why it is necessary to make rule and definite demands. If all that where needed were just to show people what to do, that would be simple, but it is not always easy to explain the chief features of false personality. Sometimes it is seen clearly, at other times it is more hidden and difficult to see, and then it is only possible to think in a general way of false personality. However, there is not a single case where I showed chief feature when people did not start violent arguing. At one meeting somebody said that he was occasionally able to observe oneself in the act of considering or becoming identified. He asked whether in this way he might come to know his false personality, and by observing it to weaken it. Actually, this is the only way and is very good so long as one does not tire of tying to do it. In the beginning, many people start very eagerly but soon get tired and begin to use the word “I” indiscriminately, without asking themselves which “I,” because we have no right to use it really in ordinary conditions. Much later, after long work, we can begin to think of one of the groups of “I”s (like what has been called Deputy Steward) which develop from magnetic center as “I.” #RandolphHarris 12 of 21

However, in ordinary conditions when you hear yourself saying “I do not like,” you must ask yourself which of your “I”s does not like. In this way you will remind yourself about the plurality which is in all of us. If you forget about it one time it will be easier to forget it next time. There are so many good beginnings in the work and then this is forgotten and people start to slide down, and in the end all that happens is that they become more mechanical than before. When it come to attribution of credit, there can be some common mistakes made. The wrong set of factors is often made in Complex Adaptive Systems for much of the same reasons. Diagnosis of causes in complex, multicausal situations are error prone. We might take as an example the problem of examining customer complaints about product malfunction in order to discover product defects or possible design improvements. Many large consumer product companies have service desks that answer thousands of calls per week about products. They frequently have systems that generate “trouble tickets” associated with each call. It is natural to ask what can be learned from the records of all this work that would contribute to improvement of the products, but closing this loop of organizational learning has often proven quite difficult. Working with a group of such reports, an analyst searches for pattern in the way the features and structure of the product interact with the circumstances of use reported by the customers. The hallmarks of complexity are present. The analyst may develop hypotheses such as: “All these customers reported that sound quality deteriorated when they were driving on country roads. Could it be that the audio unit is disturbed by shocks spaced at a particular frequency?” #RandolphHarris 13 of 21

Many hypotheses like this one are generated, but not all will be correct. In many organizations, such hypotheses are tested by checking if they are sufficient to reproduce the problem. In a complex World, many of those tests will fail. Someone from product development (not the same division as customer service) will subject the unit to low-frequency jolts and observe that it still performs well. An interesting strategy at such a moment of impasse is to bring into the process some of the frontline customer service agents who took the original calls. They may suggest something like, “These all came in last winter. Does it only happen if the unit is cold?” Of course, this may not turn out to be the answer. However, in an organization having trouble maintaining contact patterns between two divisions, the effort to correct a misattribution provides an occasion for interaction during which other useful information may flow. It functions as an episode of triggered recombination. Product people learn of other patterns noticed in customer service. The frontline agents learn about new product ideas in development and can then be alert to relevant remarks from customers. All of this reasoning makes sense in games like football or baseball or tennis, in which the same situation arises many times in one game, and the same players confront each other from one game to the next. Then there is time and opportunity to observe any systematic behaviour, and respond to it. Correspondingly, it is important to avoid patterns that can be exploited, and stick to the best mix. However, what about games that are played just once? #RandolphHarris 14 of 21

Consider the choices of points of attack and defense in a battle. Here the situation is usually so unique that no system from your previous actions can be inferred by the other side. However, a case for random choice arises from the possibility of espionage. If you choose a definite course of action, and the enemy discovers what you are going to do, one will adapt one’s course of action to one’s maximum disadvantage. You want to surprise one; the surest way to do so is to surprise yourself. You may want to consider keeping the options open as long as possible, and at the last moment choose between them by an unpredictable and therefore espionage-proof device. The relative proportions of the device should also be such that if the enemy discovered them, one would not be able to turn the knowledge to one’s advantage. However, that is just the best mix calculated in the description above. Finally, a warning. Even when you are using your best mix, there will be occasions when you have a poor outcome. Even if Paris Hilton is unpredictable, sometimes Britney Spears will still guess right and knock the ball out of the park. In football, in the third down and a yard to go, a run up the middle is the percentage play; but it is important to throw an occasional bomb to keep the defense honest. When such a pass succeeds, fans and sportscasters will marvel at the cunning choice of play, and say the coach is a genius. When it fails, the coach will come in for a lot of criticism: how could one gamble on a pass instead of going for the percentage play? #RandolphHarris 15 of 21

The time to justify the coach’s strategy is before using it on any particular occasion. The coach should publicize the fact that mixing is vital; the run up the middle remains such a good percentage play precisely because some defensive resources must be diverted to guard against the occasional costly bomb. However, we suspect that even if the coach shouts this message in all newspapers and television channels before the game, and then uses a bomb in such a situation and it fails, one will come in for just as much criticism as if one had not tried to educate the public in the elements of game theory. Another game we want to consider is politics. Of course, sports can be just as important and as serious as decisions made in Congress. An unnoticed “first” in politics was marked in 1989. That was the year John Sununu moved into the White House as its chief of staff, making him in all likelihood the World’s most highly placed “computernik.” In a World bristling with microchips, he was the first computer-literate person ever to occupy one of the pinnacles of political power. A mechanical engineer by training, Sununu had done doctoral work at the Massachusetts Institute of Technology and was known as a whiz who could spot and correct programming errors and question the mathematical model underlying an environmental impact statement. Whatever one may think of his political views, Sununu undeniably understood the power-potential of computerized information. #RandolphHarris 16 of 21

Before arriving in Washington, Sununu had served as governor of New Hampshire. When Sununu installed an electronic fiscal and financial control system for the state, members of the legislature demanded access to the data stored in the IBM mainframe. Sununu sidetracked their proposals declaring, “They’ll get what we think they need.” According to Time magazine, Sununu “seemed to be trying to shift the balance of political power” by “holding the state’s computerized financial data close to his chest.” In the end, the governor was forced to give one legislative official a password providing access to some (but not all) of the disputed data. Similarly, though a state court had held that citizens had a right to see and copy public documents, Sununu insisted that this did not apply to computerized data. Sununu, as governor, fully understood the power of knowledge about knowledge. Sununu’s action in New Hampshire was hardly subtle. Stamping something confidential or withholding access is an age-old tactic. New, more potent tools—many of them computer-based—are now available to those who wish to control data, information, and knowledge. In fact, we are witnessing a shift to a higher—and less visible—level of power struggle that reflects the rising level of abstraction and complexity in society generally as the super-symbolic economy spreads. Take, for example, computers. We now use computers to build computers. We are also developing CASE—computer-assisted software engineering. This is based on what might be termed “meta-software”—software designed to produce software. #RandolphHarris 17 of 21

One can imagine a future in which CASE is used to produce the meta-software, itself, in a kind of infinite regress, as the process moves to higher and higher levels of abstraction. Similarly, the early 1980s, “spreadsheet software” spread rapidly through the business World. These computer programs permitted hundreds of thousands of users to put numbers into columns and rows, as in a ledger book, and to manipulate them easily. Because they could automatically show how a change in one number or variable would affect all the others, they accustomed a whole generation of users to think in terms of “what if” scenarios. What would happen if we raised the price of a product by 2 percent? What if interest rates fell by half a point? What if we could get the new product to market a month sooner? However, spreadsheets, like traditional ledgers, were two-dimensional, flat as a chessboard. In 1989, Lotus Development Corporation, the main spreadsheet supplier, introduced its 1-2-3 Release 3.0. This program can be used to create three-dimensional spreadsheets—the accounting equivalent of moving chess pieces up and down as well as backward and forward on the conventional board. It permits users to simulate change in a business or a process in far more complex and revealing ways. It leads users to ask much smarter what-if questions at a much higher level. The new system of wealth creation requires a symbol-drenched work force. #RandolphHarris 18 of 21

Constant exposure to the data deluge—to media, computers, paperwork, fax machines, telephones, movies, posters, advertisements, memos, bills, invoiced, and a thousand other symbolic stimuli, with millions spending their time attending meetings, presenting ideas, persuading, negotiating, and otherwise exchanging images—makes for an increasingly “info-savvy” population. Just as Eskimos develop high sensitivity to differences in the properties of snow, and farmers can almost intuitively sense weather and soil changes, mind-workers become attuned to this informational environment. This rising sophistication compels those in power to seek new, higher-level instruments of persuasion and/or social control. Satellites, videocassettes, narrow-casting, niche-identification, cluster-targeting, extra-intelligent networks, instant polling, simulation, mathematical modeling, and other such technologies are becoming a taken-for-granted part of the political environment in the affluent nations. And along with these come new ways of manipulating computerized information that make all the conventional info-tactics of the politician or bureaucrat look crude and klutzy by comparison. Along with changes in the general population, therefore, fed by the shift to the new wealth-creation system, comes a parallel upgrading of the tools of manipulation used by politicians and government officialdom to hold on to their power. That is what meta-tactics are all about. #RandolphHarris 19 of 21

Nonetheless, even wealth and leisure cause problems. Lester Millbrath, professor of sociology and political science, observes, “Nanotechnologies will create the problem of how to meaningfully and sustainably occupy the time of people who need not perform much work in order to have a sufficiency of life’s goods. Our society has never faced this problem before, and it is not clear what social restructuring will be required to have a good society in those circumstances. We face much deep social learning.” The World has had little experience with what anthropologists’ call “abundance economies.” The Native American tribes of the pacific Northwest were one of those rarities. Their civilization was built upon an ample supply of goods, inexhaustible, and obtained without excessive expenditure of labour. The Kwakiutls became famous for the “potlaches”: contests in which they sought to shame their rivals by heaping more gifts upon them than they could ever return. The potlatches would often be a year in preparation, lasts for days, and occasionally involved destruction of entire buildings. It was certainly a colourful form of keeping up with the Winchesters. What will motivate us, once we have achieved an abundance economy? What will we regard as worthwhile goals to pursue? #RandolphHarris 20 of 21

Will part of the economy of abundance motive of to gain increased knowledge, new art, improved philosophy, eliminate human and planetary ills? Will we find ourselves creating a better, wiser World, or sunk in boredom and jaded now that we have all and want nothing? If boredom gets out of hand, the lively spectacle of wealthy doners seeking to outdo each other to endow the arts, assist the poor, and do other good deeds for the sake of prestige would be welcome. What will happen as life spans continue to lengthen and the time needed to make a living decreases? Even today, there are people who, when confronted with the prospect of significantly longer life span, exclaim that they could not imagine what they would do with all that time. This response can be hard to understand, when it would take a thousand years to walk all the World’s roads, more thousands of years to read all the World’s books, and another ten thousand years to have dinner conversation with each of the World’s people—but tastes differ, and even a few decades of bad television might make anyone long for the peace of the grave. However, perhaps more people will start hibernating. We all could use more sleep. Then wake up to a beautiful World, well rested and ready to enjoy their pleasures of life. Confusing? Of course! Like most truths, when we try to apply them to specific situations in our individual lives, we run the risk of failure. However, let that bit of wisdom sink in: You cannot intentionally set out to create or capture your own personal significance—not as a goal in itself. Human beings strive perpetually toward ultimate humanness, which itself may be anyway a different kind of Becoming and growing. #RandolphHarris 21 of 21

Cresleigh Homes

When it comes to entertaining a crowd, the Residence 4 model at #Havenwood is an absolute dream! 🌈 Take advantage of the butler’s pantry connecting the kitchen and dining rooms and customize the great room and loft room upstairs to fit your family’s needs. 👏

Check out more – including a full virtual tour – on our #CresleighHomes website!
You Made Friends at the Bar–You Join them Almost Every Day of the Week

Our individual accomplishments, opinions, and contributions enable us to known our own unique identity and to take pleasure in feeling tht we are a significant member of the human family. However, at times, differences in the way we act, look, dress, or think can separate us from those around us. By definition, an accessible engagement does not exhaust the situation; there is no situational closure, physical or conventional, to cut it off from nonparticipants. What we find instead is some obligation and some effort on the part of both participants and bystanders to act as if the engagement were physically cut off from the rest of the situation. In short, a “conventional engagement closure” is found. Bystanders extend a type of civil inattention, but one that is designed for encounters, not for individuals. Bystanders are obliged to refrain from exploiting the communication position in which they find themselves, and to give visible expression to the participants of the gathering that they are focusing their attention elsewhere—a courtesy of some complexity, since a too studied inattention to what one is in a position to overhear can easily spoil a show of inattention. I do not want to overstress rational intent in situational behaviour. An individual is supposed to be entirely in or entirely out of an encounter. However, even the individual who wants to follow this rule cannot completely control the expressed direction of one’s attention. If one’s attention is attracted to an accessible encounter, then one’s attempt to conceal the fact is likely to be visible both to those with whom one ought to be participating and to those whom one ought to be disattending. #RandolphHarris 1 of 22

Since there are many reasons why an individual might want to overhear the content of an engagement of which one is not a member, one may often simulate inattention, giving the impression that conventional closure has been obtained, while in fact one is furtively attending to the talk. How much of this eavesdropping actually goes on, and in what situations, is difficult to assess. The expression of inattention and noninvolvement exhibited by those who are physically close to an encounter in which they are not participants can be observed in an extreme form at times when an individual could join the encounter (as far as its participants are concerned), but finds oneself “psychologically” incapable of doing so. What can then result is a kind of conversational parasitism, often observable on mental hospital wards. For example, one psychotic young woman I observed would sit alongside her mother and look straight ahead while the latter was engaged in conversation with a nurse, maintaining what appeared to be civil inattention in regard to the neighbouring engagement. However, while attempting to keep her face composed like that of an uninvolved, uninterested bystander, she would keep up a running line of derisive comment on what was being said, uttering these loud stage whispers under great verbal pressure, from the side of her mouth. The psychological issue here, presumably, was that of “dissociation.” However, the direction of flow taken by the two dissociated lines of conduct—conversational participation and civil inattention—seemed entirely determined by the social organization of communication that is standard for social situations in our society. #RandolphHarris 2 of 22

In a social situation, then, an individual may find oneself torn apart, but torn apart on a standard rack that is articulated in a standard way. There are circumstances in which it is difficult for participants to show tactful trust of bystanders and for bystanders to extend civil inattention; in brief, there are times when conventional closure is difficult to manage. For one example of this we can return to small enclosed place like elevators, where individuals may be so closely brought together that no pretense of not hearing can possibly be maintained. At such times, in middle-class America at least, there seems to be a tendency for participants of an encounter. A similar kind of issue seems to arise in near-empty bars, as novelists have pointed out: We were alone in that bar, it was still the middle of the morning and the presence of the barman there was embarrassing. One could not help overhearing. In his white impassive coat he was a figure of reticent authority. However, he probably realized this too, he was nice enough to keep bobbing down behind the bar and shoveling about his glasses and his little trays of ice. So Darke ordered two more as it were from no-one, and soon thee bobbed up. The cabdriver has something of the same kind of problem here as the bar man. So too has the individual who is momentarily left to his own resources while a person to whom he has been talking answers a telephone call; physically close to the engaged other and patently unoccupied, he must yet somehow show civil inattention. Similarly, in a three-person engagement, when a talker interrupts his talk to answers the phone, the two remaining persons may attempt a quiet, and often very limp, conversation. #RandolphHarris 3 of 22

Where civil inattention is physically difficult to manage, the scene is set for a special kind of dominance. In an elevator, for example, those in one of the engagements may continue fully engaged, forcing the others present to accept the role of nonpersons. Similarly, when two unacquainted couples are required to share the same booth in a restaurant, and they elect to forego trying to maintain an inclusive face engagement, one couple may tacitly give way to the louder interaction of the other. In these situations, the submissive couple may attempt to show independence and civil inattention by beginning a talk of their own. However, while it may appear convincing to the other couple, this weaker talk is not likely to convince it own participants, who, in carrying it on, will be admitting to each other not only that they have been upstaged, but that they are willing to try to pretend that they have not. In Britain, it is my impression that where one of the units present is of “good” speech, that is, received pronunciation, then it is this group that is likely to talk openly, as if the other could easily offer civil inattention and could easily stop their own conversation. This is one of the ways in which a visitor to Britain is struck by the startling vulgarity (according to American standards) of the British upper middle class. It may be added that strength in these cases derives not from muscle, but, typically, from social class. Given the fact that participants and bystanders are required to help maintain the integrity of the encounter, and given the complicating fact that bystanders of this encounter may well be participant of another, we may expect some tacit cooperation in maintaining conventional closure. #RandolphHarris 4 of 22

First, if bystanders are to deist in some way from exploiting their communication opportunities, then it will fall upon the participants to limit their action and words to one that will not be too hard to disattend. And this keeping down of the excitement level is, in fact, what is generally found. Interestingly enough, this tendency is matched by another that moves in the opposite direction, namely, acting in such a way as to show confidence in the willingness of bystander not to exploit their situation. Thus, as already suggested, whispering or obvious use of code terms will often be thought impolite, in part because it casts a doubt on bystanders’ willingness to be inattentive. One consequence of the combination of these rules of conventional closure may be mentioned. It is a rule of conversation that participants show consideration for one another, by, for example, avoiding facts about which the other might be touchy, or by showing constraint in raising criticism, and so forth. Disparagement of persons not present, on the other hand, is usually quite acceptable, offering a basis of preferential solidarity for those in the encounter. In addition, the conversation may well involve business matters that an absent other cannot safely be made privy to. It follows, therefore, that the run of comments in a conversational encounter may have to be altered strategically when a relevantly excluded person approaches, lest the content of the talk put too much strain upon one’s willingness to offer civil attention; when one approaches with the intention of entering the encounter, even more delicacy is required. #RandolphHarris 5 of 22

The well-known example is that of the individual who comes into a room to find that conversation has suddenly stopped and that other present are seeking in a flustered way to find a new and tenable topic. Sometimes, as a relevantly excluded other approaches, a particular physical point is reached where the conversation can be altered without either letting the oncomer hear what would be embarrassing to one (or what would embarrass the speakers for one to hear) or giving one an impression that something embarrassing regarding one has been suppressed. This distance will, of course, vary with the social skill of the participants. Sometimes, too, a given room will have a special “safe region,” from which vantage point any newcomer can be spied in time to safely alter the content to talk without showing that an alteration was necessary. In these circumstances we sometimes find skill-showing, where the talkers daringly and cooly continue their talk up to the very last moment for altering it safely. Many people experience emotional states they cannot understand and identify. They often wonder at the intensity, origin, explanation, and duration of emotions. They also worry about what they might do as a result of these emotions. They may even question whether the emotions are “normal” or not. Of course, this happens to all of us at times. It is one of the risks of being thinking, sensitive people. We begin questioning, analyzing our own experiences. We also categorize them, because that is what our rationalistic, scientific society expects. #RandolphHarris 6 of 22

And when we cannot find a neat explanation or pigeonhole for a particular experience, we either bend it to fit another category, deny it, repress it, or project it onto somebody else (“I am not angry; you are!!”). If we cannot do any of these things because we are too honest with ourselves, we may conclude that the feeling is a bad one or a “sick” one. What do you do when a person who has been a good worker begins to turn in shoddy work? You can fire the individual, but that really does not solve the matter. You can berate the worker, but this usually causes resentment. Sometimes, especially when someone has been on the job for a long time, it is best to call the individual into the office and tell the individual that one is a finer employee. Compliment them on the amount of time they have spent on the job, the quality of their typical work and the quantity. Explain to them that they have received a lot of compliments about their great work. Then gently explain that in the present their work has been slipping and is taking too long and not up to standards. And ask them if there is a way to find a resolution to the problem. Many times, an honest employee will say that they not realized that their productivity has been declining, and they will promise to excel in future projects. In fact, the average person can be led readily if you have one’s respect and if you show that you respect that person for some kind of ability. #RandolphHarris 7 of 22

If you want to improve a person in a certain respect, act as though that particular trait were already one of the individual’s outstanding characteristics. Assume a virtue, if you have it not. And it might be well to assume and state openly that other people have the virtue you want them to develop. Give them a fine reputation to live up to, and they will make prodigious efforts rather than see you disillusioned. When people are given a standard of behaviour and a reputation that is expected of them, you may find that the individual will find it impossible not to follow through. If you want to excel in that difficult leadership role of changing the attitude or behaviour of others, give the other person a fine reputation to live up to. There can be good example of a self-fulfilling prophecy. [Somebody asked whether “Chief Feature” id est, the prime feature of false personality) was a food for false personality.] Chief feature is not food. Chief feature is false personality. False personality in most cases is based on one feature which enters into everything. Some day we will take some examples of chief feature and you will see how it is really that which makes false personality. “What is the best way to look for one’s chief feature?” someone asked. Simply see yourself. I do not know how to explain it better. It is possible one may find something—chief feature of the moment. It is imaginary personality; this is chief feature for everybody. “Can one alter one’s chief feature?” asked someone else. First it is necessary to know it. If you know it, much will depend on the quality of your knowing. If you know it well, then it is possible to change it. #RandolphHarris 8 of 22

“When an attitude at the back of a negative emotion is very old and habitual, possibly a feature, how can I attack it?” Begin from the feature. Find the feature, talk about it and so on. It is necessary to think about false personality and in some cases you can see definitely a kind of chief feature coming into everything, like the axis round which everything turns. It can be shown, but the person will say, “Absurd, anything but not that!” Or sometimes it is so obvious that it is impossible to deny it, but with the help of buffers one can forget it again. I have known people who gave me a name to their chief feature several times and remembered it for some time. Then I met them again and they had forgotten, or when they remembered they had one face, and began to speak as though they had never spoken about it at all. You must come near to it yourself. When you feel it yourself, then you will know; if you are only told, you may always forget. “Can I get a clue to false personality by thinking of events in the past?” Sometimes you may. Either in the past or in your friends. However, you must understand that you also have false personality, not only your friends! “Can we see false personality without help?” There is nothing again it theoretically, only I never saw such a case and nobody else I know saw such a case. Even with help people are not generally prepared to see it. It is as if you were to show a man his reflection in a real, actual mirror, and he were to say, “This is not me. This is not a reflection of me.” However, if a man is prepared, it is sometimes possible to recognize a feature of weakness in oneself. If a man knows this feature, if he begins to keep it in mind and to remember it, then there may be a certain moment when he is free from this feature, when his action is not determined by this weakness. #RandolphHarris 9 of 22

Sometimes our features or weaknesses take simple forms like laziness, but in other cases their forms are so well disguised that there are no ordinary words to describe them, and they can only be described by some kind of diagram or drawing. Laziness is for some people 75 percent of their lives or more. Sometimes laziness is very important, sometimes it is the chief feature of false personality. Very often it is chief feature, and all the rest depends on laziness and serves laziness. However, remember that there are different kinds of laziness. It is necessary to find them by observing yourself and observing other people. For instance, there are very busy people who are always doing something and yet their minds may be lazy. That happens more often than anything else. Laziness is not only the desire to sit and do nothing. However, the goal is to prevent others from exploiting any systematic behaviour of yours. If they have a preference for a particular action, that would mean only that they had chosen the worst course from your perspective. The basic idea is that one resorts to chance as the means of keeping the other player from exploiting any systematic behaviour on your part. Turning this idea into practice is more subtle. Many of us do not wish to settle for knowing just a little bit of other people, especially those we care about. So, we mut find ways of opening up avenues of approach. By experimenting, we can invite these people to come out into the sunlight and experience as much of life as possible. Why should we? If a person is happy being a Bluffer or an Expert or a Life of the Party, is it our business to take on the role of disturbing the individual? Well, it is important not to taunt or torment but to dare the other person to become more fully what one is. #RandolphHarris 10 of 22

In complex systems, it is difficult to determine what should be rewarded or which choice is appropriate. Measurement of success is often infrequent, and shifting context makes few observations comparable. Deliberation costs for choices can be high, especially if they require the apparatus of formal logic or statistics, or social processes of choice such as scientific peer review—not to speak of court proceedings. Feedback is ambiguous. Circumstances, even goals, are changing. All of this follows from the fundamental premise: we are coping with system that are complex and adaptive, not simple or static. In the short run we are not likely to have a direct approach that “get it completely right.” We will need as well the indirect methods of harnessing complexity. The difficulty of attributing credit in real experience can be reinforced by considering a few examples. The war in Vietnam provides a striking case. Although war usually produces large rewards (and punishments) and, in the end, provides clear feedback on the result, none of the other circumstances for effective learning obtains. For the Americans, the Vietnam War was not a victory. However, exactly what lessons and no obvious way to determine which candidates are most appropriate. Despite these impediments, lessons were learned by the American military. These included the need for decisive force in any future war, the need to avoid slow escalation, and the need to avoid civilian interference in the conduct of the war. These lessons—“strategies,” in our terms—were applied to the planning and conduct of the Gulf War and seemed to be effective in that application. #RandolphHarris 11 of 22

On the other hand, for the Soviet Union the Vietnam War was a success. The lessons drawn from the way by the Soviet Union emphasized that their Vietnamese allies won because of their great will and courage, assisted by military aid from Communist nations. These optimistic lessons would not have warned the Soviets about the dangers of their later intervention in Afghanistan. Biological systems also face difficulties in attributing credit. Consider birds, which determine from experience the visual characteristics of dangerous predators. Their situation illustrates one of the many interesting complications of credit attribution in a Complex Adaptive System: exploitation by others. The method is mimicry—as when many species of moths evolve spots on their wings that resemble the eyes of larger predators. This works because the birds develop a “prediction” of danger from appearance and rely on it to avoid predators. One presumes that the birds’ capability to associate certain appearances with danger, which is a mechanism for attributing credit, serves the birds well overall. However, the moths can also exploit the birds’ imperfect credit attribution to avoid being eaten. Once again coevolution increases complexity and inhibit prediction. For a nonbiological example of the limits of credit attribution, consider the person who ends the year with the highest sales volume, receives a significant bonus, and is singled out to be emulated. Years later, more careful cost accounting may show that most of the sales actually lost money for the firm because of eventual refunds or support costs. #RandolphHarris 12 of 22

The business literature is rife with stories of performance indicators that failed to capture important aspects of a complex setting. These misattributions may occur because of casual connections that no one understands, or because some employees, like the spotted moths, come to mimic features that other employees, like the birds, have come to associate with success or failure. The difficulties of credit attribution are endemic in Complex Adaptive Systems. Our aim is not to escape the, though we recommend that when it is feasible. Instead, our aim is to suggest how the side effects of inevitable mistakes of attribution can be turned to some advantage. Each of these three categories is constructed as a composite of actual cases in which complexity makes some mistakes of attribution inevitable. They illustrate a few different problems of inference that are highly characteristic of credit attribution in complex system: the mistake of crediting or blaming a part when a larger ensemble is responsible, the mistake of attributing credit or blame to a particular ensemble of factors when in fact a different ensemble is responsible, and the mistake of crediting a misconstrued strategy, where the action involved produced success, but the conditions in which the action should be taken have been misunderstood. The first type of mistake, crediting a part when a larger ensemble is responsible, is very common in Complex Adaptive Systems since they so often involve a number of entangled factors. It is easy to notice that a single or strategy is associated with a series of successes (or failures). #RandolphHarris 13 of 22

If you are not positioned to observe the operation of other necessary forces, you reach an incorrect conclusion that it alone causes the results. Consider a manager of a department that uses project teams assembled for specific tasks. If it is the practice in the unit to reward team members whose work contributed to notable success, a manager can almost be sure that there will be some occasions where an individual receives credit for what was produced by the interplay among contributions of several team members—what is sometimes labeled the group’s “chemistry.” We have stressed insufficient exploration in examples throughout this essay because we so often have seen variation being undervalued by managers of Complex Adaptive Systems. However, for this case, let us stipulate that the manager believes the department has a problem of insufficient exploitation. Perhaps “back channel” communication suggests that a project group has done well by ensemble effect rather than the efforts of the most prominent individual. How can the manager get “mileage” out of discovering those attribution mistakes without knowing what caused them? One approach is to make a special effort to reassemble that identical team for a later problem, retaining (and exploiting) the uncredited ensemble that may be there. Doing this has a cost, of course. It reduces the ability to mix and match individuals to the characteristic of the next task. Harnessing complexity does not always come for free. #RandolphHarris 14 of 22

Infinite varieties of deception (and self-deception) are found in the masses of data, information, and knowledge that flow through the government’s mind-work mill every day. Space constraints make it impossible to continue illustrating and classifying them here. Instead, we will list just a few more in abbreviated form. THE OMISSION TACTIC. Because politic is so intensely adversarial, political messages are even more consciously selective than most. Typically, they have gaping holes where someone applied the Omission Tactic and ripped relevant or balancing facts out of them. THE GENERALITY TACTIC. Here details that might lead to bureaucratic or political opposition are glossed over with airy abstraction. Diplomatic communiques are rife with examples—which accounts for their frequently brain-numbing style. TIMING TACTICS. Here the most common approach is to delay sending a message until it is too late for the receiver to do anything about it. Thick budget documents are dumped in the laps of legislators who are supposed to respond to them in a few days—well before they can intelligently digest and analyze them. White House speechwriters are known to deliver their drafts of a presidential speech at the latest possible moment, allowing other staffers minimum time to money with the text. THE DRIBBLE TACTIC. Here, data, information, and knowledge are doled out in tiny takes at different times, rathe than compiled into a single document. In this way the pattern of events is broken up and made less visible to the receiver. #RandolphHarris 15 of 22

THE TIDAL WAVE TACTIC. When someone complains about being kept uninformed, the shrewd player ships him or her so much paper that the recipient is drowned and cannot find the essential facts in all the froth. THE VAPOR TACTIC. Here a host of vaporous rumors are released, along with some true facts, so that receivers cannot distinguish the latter from the former. THE BLOW-BACK TACTIC. Here a false story is planted overseas so that it will be picked up and reprinted by the domestic press. This tactic is employed by intelligence and propaganda agencies. But sometimes the blow-back is inadvertent—or seems to be. This CIA once planted a story in the Italian press about the terrorist Red Brigade. This account was picked up and incorporated in a book published in the United States of America, the galley proofs of which were read by then-Secretary of State Al Haig. When Haig commented on the story in a press conference, his remark then, in turn, incorporated in the finished version of the book. This self-referential process is more common than imagined. THE BIG LIE TACTIC. Made famous by Hitler’s propaganda minister, Josef Goebbels, it is based on the idea that if a lie is macro enough it will be believed more readily than any number of mere micro-lies. In this category was the 1987 report spread by Moscow claiming that the World AIDS epidemic was launched by agents in Maryland. Widely disseminated around the World, the story is utterly repudiated by Soviet scientists. #RandolphHarris 16 of 22

THE REVERAL TACTIC. Few examples of tampering with, or massaging, the facts require as much chutzpah as the Reversal Tactic. This simply turns a given message inside out. An example occurred not long ago in Israel, where no love was lost between Prime Minister Yitzhak Shamir and Foreign Minister Shimon Peres. At one point Shamir instructed the Foreign Ministry to notify its embassies around the World that Peres had no authority to promote an interactional conference aimed at resolving the Arab-Israeli problem. Peres’s staff at the Foreign Ministry received the Prime Minister’s message, but simply scrapped it and sent out cables saying the exact opposite. When a senior official was later asked how that could happen, he replied: “How can you ask me such a question? This is war.” Given this lengthy list of technique widely used for doctoring the messages that flow through government offices, it becomes apparent that few statements, messages, or “facts” in political or governmental life can be taken at face value. Almost nothing is power-neutral. Most data, information, and knowledge circulating in government are so politically processed that even if we ask, Cui bono?—whose interest is served?—and even if we think we have got the answer, we may still not be able to cut through the “spin” to the reality beneath it. And all this occurs before the media further reprocesses reality to fit its own requirements. Media massage merely further denatures the “facts.” The implications of what we have just seen go to the crux of the relationship between democracy and knowledge. An informed public is held to be a precondition for democracy. However, what do we mean by “informed”? #RandolphHarris 17 of 22

Restricting government secrecy and gaining public access to documents are necessary in any democracy. However, these are only feeble first steps. For to understand those documents we need to know how they have been doctored along the way as they passed from hand to hand, level to level, and agency to agency in the bureaucratic bowels of government. The full “content” of any message does not appear on the page or the computer screen. In fact, the most important political content of the document may be this history of its processing. At a still deeper level, the ubiquity of these most commonly exploited info-tactics casts doubt on any lingering notion that governing is a “rational” activity or that leaders are capable of “objectively based” decision. Winston Churchill was right when he refused to read “sifted and digested” intelligence analyses, insisting instead on seeing the “authentic documents…in their original form,” so he could draw his own conclusions. However, it is obviously impossible for any decisionmaker to read all the raw data, all the information, and grapple with all the knowledge needed for decision. What we have seen here are just a few of the tricks of the trade exploited by streetwise political in-fighters and savvy staffers in World capitals from Seoul to Stockholm or Bonn to Beijing. Smart politicians and bureaucrats know in their bellies that data, information, and knowledge are adversarial weapons—loaded and ready to be fired—in the power struggles that constitute political life. #RandolphHarris 18 of 22

What most of them do not yet know, however, is that all these Machiavellian ploys and devices must now be regarded as kindergarten stuff. For the struggle for power changes when knowledge about knowledge becomes the prime source of power. In the era of “meta-tactics” in the mind-work mills we call government, is moving the power game to an even higher level. Over centuries, the trend ha seemed to be toward centralization, beginning with the rise of factories and industrial towns. What drove these developments was the high cost of machinery and plant operations, the need to be near power sources, the impracticality of transportation among many small, dispersed sites, and the need for face-to-face communication. Beginning with the first industrial revolution, factories employed large numbers of people in one place, leading to overcrowding and making local economies dependent on one industry and sometimes on a single company. Costly equipment necessitated central locations for textile production, rather than the cottage industries where a lone woman could earn a livelihood carding wool and creating thread on a spinning wheel (providing the origin of the term spinster). By the 1930s, the belief in the virtues of centralization and central panning—the supposed efficiencies and economies of scale—led to nationwide or continentwide experiments in centralization. However, over the last decade, these large-scale experiments have been dismantled, from Britain’s privatization of nationalized utilities to the beginning of a return to the market system in Eastern European countries. #RandolphHarris 19 of 22

Because the old limits on transportation, energy sources, and communication have fallen, business is now decentralizing. Between 1981 and 1986, the Forbes 500 companies cut their employees by 1.8 million. However, during those same years, total civilian jobs went up by 9.2 million. Start-up companies created 14 million jobs; small companies created another 4.5 million. Telecommuting is booming, as are new businesses, independent professionals, and cottage industries. We have also seen the resurgence of small, but highly diverse stores: gourmet-food shops, specialty ethnic shops, tea and coffee, purveyors, organic and health-food stores, bakeries, yogurt shops, gourmet ice cream stores, convenience stores offering twenty-four-hour access, shops selling packaged food plus snacks. These stores epitomize something fundamental: At some point, what we want is not a standard good at an ever-cheaper price, but special things customized to meet our own individual tastes or needs. The trend for advanced technologies seems to be leading away from centralization. Will nanotechnology counter or accelerate this trend? By reducing the cost of equipment, by reducing the need for large numbers of people to work on one product, and brining greater ability to produce the customized goods that people want, nanotechnology will probably continue the twentieth-century toward decentralization. The results, though, will be disruptive to existing businesses. #RandolphHarris 20 of 22

The computer industry perhaps provides a clue to what might happen as costs are lowered by nanotechnology. The computer-software industry is characterized by the garage-shop start-up. When your equipment is inexpensive—affordable PCs built around lost-cost chips—and your can make a product by throwing in some ingenuity and human labour, it is possible to start a new industry on a shoestring. In 1900, when cars were simple, there were many car manufacturers. By the 1980s, if you were not an industrial giant like General Motors or Ford, BMW or Honda, you had to be John De Lorean to even get a shot at acquiring the capital to play in the business. If molecular manufacturing can slash the capital costs for producing cars or other plant-intensive equipment, we will see the equivalent of garage-shop businesses springing up to offer new products, and hiring workers away from the industrial giants of today just as the personal computer has destroyed the dominance of the mainframe. The American dream is to be an entrepreneur, and the technological trends of the twentieth century point in that direction. Nanotechnology probably continues it. In one area, however, the late twentieth-century trend has been toward uniformity. The nations of Western Europe are in the process of uniting under one set of economic rules, and parts of Eastern Europe are anxious to join them. #RandolphHarris 21 of 22

More and more supranational and transnational organizations knit the World together. The growth of trade has motivated economic integration. Molecular manufacturing will work against this trend as well, permitting radical decentralization in economic terms. This will help groups that wish to step aside from the stream of change, enabling them to be more independent of the turbulent outside World, picking and choosing what technologies they use. However, it will also help groups that wish to free themselves from the constraints of the international community. Economic sanctions will have little force against countries that need no imports or exports to maintain a high standard of living. And export restrictions will likewise do little to hamper a military buildup. By weakening the ties of trade, molecular manufacturing threatens to weaken the glue of that holds nations together. We need that glue, though, to deal with the arms-control issues raised by molecular manufacturing itself. This problem, caused by the potential for decentralization, may loom large in the coming years. Therefore, apparently, we have to come to grips with the ongoing conflict in our institutionalized way of viewing ourselves. Since we currently have some patterns of living that view man as a Thinker, they need to be enlarged to recognize man’s need to be a Feeler too. To do so would involved our educational systems, literary and publishing ventures, scientific, technological, and governmental agencies. Similarly, the agencies that view man only as emotional, like the entertainment, recreational, theological, ecclesiastical, and art media, need to be retooled to take into account the important place intellect and reason have in our lives. #RandolphHarris 22 of 22

CRESLEIGH HAVENWOOD
Lincoln, CA | from the high $600s
Now Selling!

No appointment needed! Cresleigh Havenwood features four distinct floor plans ranging from 2,293 – 3,377 square feet and offering up to five bedrooms.

Each plan has been thoughtfully designed and includes great features such as single story homes, guest suites, optional offices, garage workshops, and more! Get the most out of your new home with Cresleigh’s All-Ready smart home featuring all the connectivity needed to keep your house running. Best of all, each Cresleigh home comes with owned solar included!

Located off of Virginiatown Road and McCourtney Road, residents of the 83 homesites of Cresleigh Havenwood will benefit from a brand new neighborhood in the charming City of Lincoln. Palo Verde Park, is just down the street and there’s plenty of recreation to take part in all around town.
The Human Dilemma

An individual has to compete with millions of others, and since there are so many of them, one solitary individual often feels that one just does not make much difference! There is a feeling that individually and as a people we are fighting a losing battle to maintain our own uniqueness and that there appears to be no end in sight. When a face engagement exhausts the situation—all persons present being accredited participants in the encounter—the problem of maintaining orderly activity will be largely internal to the encounter: the allocation of talking time (if the engagement is a spoken one); the maintenance of something innocuous to talk or act upon (this being describable as the problem of “safe supplies”); the inhibition of hostility; and so forth. When there are persons present who are not participants in the engagement, we know that inevitably they will be in a position to learn something about the encounter as a whole is conducted. When a face engagement must be carried on in a situation containing bystanders, I will refer to it as accessible. Whenever a face engagement is accessible to nonparticipants there is a fully shared and unshared participation. All persons in the gathering at large will be immersed in a common pool of unfocused interaction, each person, by one’s mere presence, manner, and appearance, transmitting some information about oneself to everyone in the situation, and each person present receiving like information from all the others present, at least in so far as one is willing to make use of one’s receiving opportunities. #RandolphHarris 1 of 22

It is this possibility of widely available communication, and the regulations arising to control this communication, that transforms a mere physical region into the locus of a sociologically relevant entity, the situation. However, above and beyond this fully common participation, the ratified members of a particular engagement will in addition be participating in interaction of the focused kind, where a message conveyed by one person is meant to make a specific contribution to a matter at hand, and is usually addressed to a particular recipient, while the other members of the encounter, and only these others, are meant to receive it too. Thus, there will be a fully shared basis of unfocused interaction underlying one or more partially shared bases of focused interaction. The difference between participation in the unfocused interaction in the situation at large and participation in the focused interaction in a face engagement is easy to sense but difficult to follow out in detail. Questions such as choice of participants for the encounter or sound level of voices have relevance for the situation as a while, because anyone in the situation will be (and will be considered to be) in a position to witness these aspects of the face engagement, which are the unfocused part of the communication flowing from it. However, the specific meanings of particular statements appropriately conveyed within a face engagement will not be available to the situation at large, although, if a special effort at secrecy be made, this furtiveness, as a general aspect of what is going on, may in fact become quite widely perceivable and an important item in the unfocused interaction that is occurring. #RandolphHarris 2 of 22

That part of the communication occurring in a face engagement that could not be conveyed through mediating channels is situational; but this situational aspect of the encounter becomes part of the unfocused communication in the situation at large only when some of the grosser improprieties, such as shouting, whispering, and broad physical gestures, occur. In considering accessible engagements, it is convenient to take a vantage point within such an encounter, and to describe the issues from this point of view. The persons present in the gathering at large can then be divided up into participants and bystanders, depending on whether or not they are official members of the engagement in question; and the issues to be considered can be divided up into obligations owned the encounter and obligations owed the gathering at large (and behind the gathering, the social occasion of which is an expression). In order for the engagement to maintain its boundaries and integrity, and to avoid being engulfed by the gathering, both participant and bystander will have to regulate their conduct appropriately. And yet even while cooperating to maintain the privacy of the given encounter, both participant and bystander will be obligated to protect the gathering at large, demonstrating that in certain ways all those within the situation stand together, undivided by their differentiating participation. Man is man because he is capable of reflective thought. Among the animal kingdom man alone has yet been able to demonstrate that he can cognitively consider his own existence, his own ending, his own limitations, and his own strengths. #RandolphHarris 3 of 22

Perhaps the limitations of man’s communicative abilities keep him from knowing any more than he does about the talents of other members of the animal kingdom; nevertheless, what he is sure of is that man can perform these and other, higher acts. With man being so superior, why is it that when we are trying to change people, we do not use meat, instead of a whip? Why do we not use praise instead of condemnation? Let us praise even the slightest improvement. That inspires the other person to keep on improving. Praise is like sunlight to the warm human spirit; we cannot flower and grow without it. And yet, while most of us are only too ready to apply to others the cold wind of criticism, we are somehow reluctant to give our fellow the warm sunshine of praise. When you have a hard day or make a mistake, you might feel discouraged or bad about yourself. However, anyone can look back on their own lives and see where a few words of praise have sharply changed their future. If something goes wrong and you are feeling bad, try writing yourself an encouraging note! What happened: I did not do well on a test. Encouraging words: I can keep trying and learning. I will not give up. Keep trying. Keep loving. Keep trusting. Keep believing. Keep growing. History is replete with striking illustrations of the sheer witchery of praise. For example, many years ago a boy of ten was working in a factory in Naples. He longed to be a singer, but his first teacher discouraged him. “You can’t sing,” he said. “You haven’t any voice at all. It sounds like the wind in the shutters.” #RandolphHarris 4 of 22

However, his mother, a poor peasant woman, put her arms about him and praised him and told him she knew he could sing, she could already see an improvement, and she went barefoot in order to save money to pay for his music lessons. That peasant mother’s praise and encouragement changed that boy’s life. His name was Enrico Caruso, and he became the greatest and most famous opera singer of his age. Many of you may not know this, but a lot of you and your parents are successful because your grandparents and great grandparents did things like go without shoes and worked hard so they could ensure their descendants would not have to miss a meal or go without a roof over their heads. So be proud of who you are and be thankful that someone had the opportunity to help you succeed. And next time you think about blowing money, even say, $30, think about how many hours it took you to make that money, and perhaps save it or put it in a Roth IRA so you have more money for retirement, or for your child’s college fund. You do not want your offspring to grow up and know the pangs of hunger. The praise, the recognition that one receives through an accomplishment can change one’s whole life. For if one does not get encouragement, one might spend one’s life never knowing what he or she could have accomplished. Use praise instead of criticism. When criticism is minimized and praise emphasized, the good things people do will be reinforced and the poorer things will atrophy for lack of attention. Many people who are praised for the good things they do end up going out of their way to do things right. #RandolphHarris 5 of 22

And even better, when praise is specific, it comes across as sincere—not something the other person may be saying just to make one feel good. Remember, we all crave appreciation and recognition, and will do almost anything to get it. However, nobody wants insincerity. Nobody wants flattery. If you and I will inspire the people with whom we come in contact to a realization of the hidden treasures they possess, we can do far more than change people. We can literally transform them. Compared with what we ought to be, we are only half awake. We are making use of only a small part of our physical and mental resources. Stating the thing broadly, the human individual thus lives far within one’s limits. One possesses powers of various sorts which one habitually fails to use. Everyone possess powers of various sorts which one habitually fails to use; and one of these powers you are probably not using to the fullest extent is your magic ability to praise people and inspire them with a realization of their latent possibilities. Abilities wither under criticism; they blossom under encouragement. To become a more effective leader of people, be hearty and sincere in your approbation and lavish in your praise. Promoting a sense of individual worth is basic to effective psychotherapy and counseling, to effective public education, to marriages, and other love relationships, and certainly to child-rearing. People who are accepted and loved and treated as worthwhile have a greater tendency to develop more fully in their selfhood, to engage themselves more fully in their tasks and chores, and, if production is any kind of measure, to turn out more of whatever we might like from them. #RandolphHarris 6 of 22

“Is a bored man free from identification?” Boredom is identification with oneself, with false personality, with something in oneself. Identification is an almost permanent state for us. It is the chief manifestation of false personality, and because of this we cannot get out of the false personality. You must be able to see this state apart from yourself, separated from yourself, and that can only be done by trying to become more conscious, trying to remember yourself, trying to be aware of yourself. Only when you become more aware of yourself are you able to struggle with manifestations like identification and lying, and with false personality itself. All work has to be on false personality. If you do any other work and leave this, it is useless work and you will fail very soon. As with negative emotions, lying and all imagination, false personality cannot exist without identification. You must understand that false personality is a combination of all lies, features and “I”s which can never be useful in any sense or in any way, either in life or in the work—like negative emotions. “If false personality entirely based on negative emotions?” There are many things besides negative emotions in false personality. For instance, in false personality there are always bad mental habits—wrong thinking. False personality, or parts of false personality, is always based on wrong thinking. #RandolphHarris 7 of 22

At the same time, if you were to take negative emotions away from false personality it would collapse; it could not exist without them. “So all negative emotions spring from false personality?” Yes certainly. How could it be otherwise? False personality is to speak a special organ for negative emotions, producing negative emotions. You remember that I said that there is no real center for negative emotions. False personality acts as a center for negative emotions. “How can one deal with the conceit of false personality?” You must know all its features first and then you must think rightly. When you think rightly you will find ways to deal with it. You must not justify it; it lives on justification, even glorification of all its features. At almost every moment of out life, even in quiet moments, we are always justifying it, considering it legitimate and finding all possible excuses for it. This is what is meant by wrong thinking. So first of all you must know false personality, and then you must think rightly about it. You must know what it is—place it so to speak—this is the first step. And, as I have said, you must realize that all identification, all considering, all lies to oneself, all weaknesses, all personality. In addition, all forms of self-will belong to false personality, so sooner or later you have to sacrifice them. “Did you say that all our likes and dislikes are in false personality?” Most of them are. And even those which did not belong to it originally, which have real roots, all pass through false personality. #RandolphHarris 8 of 22

[Somebody asked if one had to know the whole of false personality in order to struggle against it because it seemed to one that one could only know little bits of it.] One most know it. It is like a special breed of bird. If you do not know it you cannot speak about it. If you have seen it you can speak about it. To see only bits, as you say, is quite enough. Every small part of it is the same colour. If you see this bird once, you will always know it. It sings in a special way; it walks in a special way. Humans are capable of understanding many of the things that happen to us, and unable to comprehend many others though we can still experience them. The lacks of comprehension are due partly to our attitudes or mind-sets, which limit our understanding to things that our word symbols can define or point toward. Partly the limitations are due to a lack of development of our fullest functioning. As self-aware beings, able to look objectively at our own experiences, we find ourselves confused and anxious at times, overjoyed and ecstatic at others. We can search for many things: happiness, wisdom, perfection, enlightenment, identity, meaning. We can be effective in dealing wholly with the life we live, and we can attain some measures of significance. In the “search for significance,” it is often a struggle, for life certainly is not a bed of roses. So, just being alive is a blessing, but also a “struggle” and full of ordinary everyday risks. However, to seek the difficult, to search for the challenging, to demonstrate human effectiveness, in short, to be significant, is the biggest struggle of all. #RandolphHarris 9 of 22

One of the first strategic lessons in tennis is not to commit to a direction until the last possible fraction of a second. Otherwise, the opponent can exploit your guess and hit the ball the other way. However, even when one cannot observe the opponent’s move, there is a great advantage to predicting it. If the server always aims to the receiver’s backhand, the receiver will prepare his or her grip and start to move toward that side in anticipation, and consequently will be more effective in the return of serve. The server, therefore, attempts to be unpredictable in order to prevent the receiver from successfully second-guessing one’s aim. Conversely, the receiver must not exclusively favour one side or the other in making one’s initial move. Unlike matching fingers, players should not equate unpredictability with even odds. Players can improve their performance by systematically favouring one side, although in an unpredictable way. For correctness, let us think of a pair of players with particular skills. The receiver’s forehand is somewhat stronger. If one anticipates correctly, one’s forehand return will be successful 90 percent of the time, while an anticipated backhand return will be successfully only 60 percent of the time. Of course, the returner fares worse if one starts to move to one side and the service goes to the other. If one goes to the backhand side while the service is to one’s forehand, one can shift and return successfully only 30 percent of the time. The other way around, one’s chances are 20 percent. #RandolphHarris 10 of 22

The server wants to keep the successful return percentage as low as possible; the returner has exactly the opposite interest. Before the match, the two players choose their game plans. What is the best strategy for each side? If the server always aims one’s serves toward the forehand, the receiver will anticipate the move to one’s forehand and successfully return the serves 90 percent of the time. If the server always aims one’s serves to the backhand, the receiver will anticipate the move toward one’s backhand and will return 60 percent of the serves successfully. Only by mixing one’s aim can the server reduce the receiver’s effectiveness. One keeps the receiver guessing and therefore unable to take full advantage of anticipating the correct position. Suppose the server tosses an imaginary coin just before each serve, and aims to the forehand or backhand according to whether the coin shows heads or tails. Now look what happens when the receiver moves to the forehand position. This guess will be correct only half the time. When correct, the forehand return is successful 90 percent of the time, and when the move to the forehead is an incorrect guess, the receiver’s successful return tale falls to 20 percent. One’s overall success rate is (1/2)90% + (1/2)20% = 55%. By a similar argument, a move toward the backhand leads to successful returns (1/2)60% + (1/2)30% = 45% of the time. Given the 50:50 mixing rule of the server, the receiver chooses the options best from one’s perspective. One should move toward one’s forehand, and the percentage of successful returns will be 55 percent. #RandolphHarris 11 of 22

For the server, this is already an improvement over the outcome when one aims one’s serve the same way all the time. For comparison, the receiver’s success rate is 90 percent or 60 percent if the server aims exclusively toward the forehand or backhand serves, respectively. Predicting business success is a lot like the example of the tennis match. All messages move through channels. However, some channels are more equal than others. All executives know that the “routing slip” which determines who gets to see a memo is a tool of power. Keeping someone “out of the loop” is a way of clipping one’s wings. Sometimes the person kept out of the loop is the person on top. When John H. Kelly was the U.S.A. ambassador in Beirut, he sent messages direct to the White House National Security Council, using the facilities of the CIA, rather than through the normal State Department chain of command. This meant he was end-running his own boss, Secretary of State George P. Shultz. Kelly, while in Washington, also met numerous times with Oliver North and other NSC officials in connection with their plan to trade arms to Iran in return for hostages—a plan Shultz had advised against. Shultz was so furious when he learned about the Beirut incident that he blasted Kelly publicly, and formally prohibited State Department personnel from communicating outside departmental channels without express instructions from either oneself of from the President. It is unlikely, however, that any such order will ever wipe out the practice- Back-channels are too useful to power-shifters. #RandolphHarris 12 of 22

One hearing of this case, Congressman Lee Hamilton, chairman of the House Intelligence committee, blurted, “I don’t think I have ever heard of that happening before—totally bypassing an American Secretary of State.” Irritation may have fogged his memory. A precisely parallel case of back-channeling took place when the American ambassador to Pakistan communicated secretly with the White House National Security Council, again bypassing a Secretary of State. In this earlier case, the back channel was set up by Henry Kissinger, then serving as head of the NSC. Kissinger used it in arranging President Nixon’s secret mission to China, which resulted in restoring relations between the two countries. Kissinger was an enthusiastic back-channeler, eager to keep information out of the official bureaucratic system and in his own hands. Claiming he had the President’s approval, he once invited William J. Porter, the U.S.A. ambassador to South Korea, to communicate directly with him without going through Porter’s boss, William Rogers, then Secretary of State. Porter’s diary notes his reaction: “Here’s the Nixon-Kissinger secret diplomatic service shaping up, secret codes and all…If the President agreed to create a super-net of ambassadors under his security adviser without the knowledge of the Secretary of State something new was happening in American history…I concluded that I was just a country boy and I would keep my head down.” #RandolphHarris 13 of 22

When the SALT treaty was being negotiated with the Soviets, the America team in Geneva was headed by Gerard C. Smith. However, Kissinger and the Pentagon’s Joint Chiefs of Staff set up a private channel so that certain staff people could communicate with the directly without Smith’s knowledge. Kissinger also maintained a back-channel to Moscow, again bypassing the State Department, sending messages to the Politburo through Anatoli Dobrynin, rather than through the appropriate State Department specialists or their counterparts in the Soviet Foreign Ministry. Only a few people in Moscow—in the Politburo, the secretariat, and the Soviet diplomatic corps—were ever aware that messages were being passed back and forth this way. The most celebrated—and perhaps most fateful—use of the Back-Channel Tactic helped prevent World War III. This occurred during the Cuban missile standoff. Formal messages ricocheted back and forth like a tennis match between President Kennedy and Soviet leader Khrushchev while the World held its breath. Russian missiles in Cuba were pointed at American soil. Kennedy orders a naval blockade. It was at that moment of high tension that Khrushchev sent Aleksandr Fomin, his KGB chief in Washington, to call on an American newsman, John Scali, whom Fomin had earlier met. On the furth day of the crisis, with danger escalating by the moment, Fomin asked Scali whether he thought the United States of America would agree not to invade Cuba if Soviets pulled out their missiles and bombers. That message, relayed by the journalist to the White Hose, proved to be a key turning point in the crisis. #RandolphHarris 14 of 22

However, even such uses of Back-Channel Tactic are simple by comparison with the more sophisticated method that might be called the Double-Channel Tactic—the sending of alternative or contradictory messages through two different channels to test reactions or to sow confusion and conflict among the recipients. Twice during negotiations over the antiballistic missile system, Kissinger and Soviet Foreign Minister Alexei Gromyko each relied on a back-channel to bypass their own normal chain of command. During these talks, in May 1971 and April 1972, Kissinger had reason to suspect that the Russians were using the Double-Channel Tactic against him. Years later Arkady Shevchenko, former Gromyko assistant defected to the United States of America and wrote in his autobiography that Kissinger’s suspicion had been unwarranted. It was not a deliberate ploy but confusion, arising because one of the Soviets had been “operating on outdated instructions from Moscow, knowing no better.” Whether or not this is correct is irrelevant here. What is clear is that Back- and Double-channeling are much-used techniques to shift power. There is also a dazzling variety of games played at the receiving end of the communication process. The most familiar of these is the Access Tactic—meaning the attempt to control access to one’s superior, and thereby to control the information one receives. Top executives and lowly secretaries alike know this game well. Access conflicts are so common they hardly merit further comment. #RandolphHarris 15 of 22

Then there is the Need-to-Know Tactic, much favoured by intelligence agencies, terrorists, and underground political movements, by means of which data, information, and knowledge are compartmentalized and carefully kept away from all but specified receivers with a validated “need to know.” The exact converse of this is the Need-Not-to-Know Tactic. A former Cabinet Secretary in the White House explains it this way: “Should I, as a White House official, know something? Does knowing it mean I have to take action? Cn the person telling me then go to someone else and say, ‘I’ve already discussed this with the White House’? That could put me in a pissing contest between two other players I don’t know anything about and have nothing to do with…There was a lot I didn’t want to know about.” The Need-Not-to-Know Tactic is also used by subordinate to protect a superior, leaving the leader in a position to claim ignorance if things go sour. During the Irangate investigation a joke that went the rounds in Washington made the point. QUESTION: How many White House aides does it take to screw in light bulb? ANSWER: None. They like to keep Reagan in the dark. By the same token, there is also a Forced-to-know Tactic, more popularly knowns as the CYA, or “cover your assets,” memo. Here the power player makes sure that another player has been notified of something, so that if things fall apart, a recipient can share the blame. Variations are numerous, but for every game played with sources, channels, and receivers, there is a multitude of ploys and stratagems directed at the message itself. #RandolphHarris 16 of 22

Credit attribution, though difficult and necessarily imperfect, can nonetheless be designed to help harness complexity. As we have already discussed, context preservation could be advantageous if the cause of apparent success is not fully understood. This indicates a general problem. Since Complex Adaptive Systems are inherently difficult to understand or predict, it follows that attribution of credit in selection will often be difficult and prone to mistakes. If it were feasible, the best response would be not to make mistakes in credit attribution. Because such mistakes can be very costly, vast bodies of academic knowledge and expensive social apparatus have been created to reduce them. Systems of logic, methods of statistics, and philosophies of science are all aimed at improving the extent to which our conclusions follow from our premises and evidence. There re public debates, professional review boards, and courts of law. All contribute to limiting the mistakes in attribution of credit that may drive selection processes. Where these tools for improving inference are cost-effective, we certainly believe they should be used, and we applaud the work that maintains and extends them. However, despite all the effort put into these valuable resources, totally accurate attribution of credit is often infeasible. Factors that make it easy to learn appropriate lessons from the experience accumulated in making a series of choices: clear rewards for the appropriate choices, repeated opportunities for observation or for practice, small deliberation costs at each choice so that frequent choices are easier, good feedback on the results of choices, unchanging circumstances that keep inferences valid, and a simple context that can be effectively analyzed. #RandolphHarris 17 of 22

As you know, changing causes problems. Molecular manufacturing offers the possibility of drastic change, a change in the means of production more fundamental than the introduction of industry, or of agriculture. Our economic and social structures have evolved around assumptions that will no longer be valid. How will we handle the changes in the way we work and live? Nanotechnology will have wide-ranging impact in many areas, including economic, industrial, and social patterns. What do historical patterns in similar circumstances tell us about the future? Any powerful technology with broad applications revolutionizes lives, and nanotechnology will be no exception. Depending on one’s point of view, this may sound exciting or it may sound disturbing, but it most certainly does not sound comfortable. In comparison to many projections of the twenty-first century, though, nanotechnology may lead to comparatively comfortable change. The changes most often projected—for a future not including nanotechnology—have been ecological disaster, resource shortages, economic collapses, and a slide back into misery. The rise of nanotechnology will offer an alternative—green wealth—but that alternative will bring great changes from the patterns of recent decades. Times of rapid technological change are disconcerting. For most of humanity’s existence, people lived in a stable pattern. They learned to live as their parents had lived—by hunting and gathering, later by farming—and changes were small and gradual. A knowledge of the past was a reliable guide to the future. #RandolphHarris 18 of 22

Sudden changes, when they did occur, were apt to be ruinous: invasions of natural disasters. These sudden changes were fought or repaired or survived as best one could. Making major changes by choice was rare, and radical innovations were generally or the worse: the old ways at least ensured the ancestors’ survival, the new might not. This made cultures conservative. It is only natural that there be efforts to resist change, but before undertaking such an effort, it makes sense to examine the record of what works and what does not. The only examples of successful change fighters have been communities that have created and maintained barricades to isolate themselves from the outside World socially, culturally, and technologically. For the two centuries before 1854, Japan turned its back on the outside World, following a deliberate policy of seclusion. The leaders of Albania restricted contacts for many years; only recently have they started to open up. Isolation attempts have worked better on a smaller scale, when participation is voluntary rather than decreed by government. Today, within the Hawaiian island chain, the tiny private owned island of Niihau, sixteen miles long and six miles wide, is deliberately kept as a preserve of the nineteenth-century Hawaiian lifestyle. #RandolphHarris 19 of 22

Over two hundred full-blooded Hawaiians there speak the Hawaiian language and use no telephones, plumbing, television, and no electricity (except in school). The Amish Pennsylvania have no surrounding ocean to help maintain their isolation, but rely instead on tight social, religious, and technological rules aimed at keeping external technology and culture out, and themselves grouped in; those who leave the fold are excluded. Rumspringa is a bad idea because you are letting teenagers go out into the English World alone and there are many evils out there that they are unaware of. And people can see they are different—innocent and pure—and will prey on them. On a national scale, attempts to take only one part of the package—whether social or technological—have not done well at all. For decades, the Soviet Union and the Eastern bloc nations welcomed Western Technology but attempted tight restrictions on the passage of people, ideas, and goods. Yet illegal music, thoughts, literature, and other knowledge still crept in—as they do into the Islamic countries. Fighting technological change in society at large has had little success, where that change gave some large group what it wanted. The most famous fighters of technological change—the Luddites—were unsuccessful. They smashed “automated” textile machinery that was replacing old hand looms during the early industrial revolution in England, but people wanted affordable clothing, and smashing equipment in one place just moved the business elsewhere. #RandolphHarris 20 of 22

Change has sometimes been postponed, as when a later group, under the banner of “Captain Swing,” smashed hundreds of threshing machines in a wide area of southern England in 1830. They succeeded keeping the old, labour-intensive ways of harvesting for over a generation. In previous centuries, when the World was less tightly connected by international trade, communications and transportation, delays of years and even decades could be enforced through violence or legal maneuvers such as tariffs, trade barriers, regulations, or outright banning. Attempting to stop or postpone change is less successful today, when technology moves internationally almost as easily as people do—and human travel is so easy that 25 million people cross the Atlantic each year. Change fighters find that the problems they create mount with time. Products made using the old, high-cost techniques are uncompetitive. There is no way to bring back the “old jobs”; they no longer make sense. However, the old habits die hard, and these same responses to the prospect of technological change continue today—ignoring it, denying it, and opposing it. Societies that have fought change, as Britain did, have fallen behind in a cloud of coal smoke. Why did the Luddites respond violently? Perhaps their response can be attributed to three factors: First, the change in their lives was sudden and radical; second, it affected a large group of people at one time, in one area; and third, in a World unprepared for rapid technological change, there was no safety net to be unemployed. #RandolphHarris 21 of 22

While local economies might have been able to absorb a trickle of hungry laid-off workers, they lacked the size and diversity needed to offer other employment options quickly to large numbers of unemployed. In the twenty-first century, however, societies have of necessity become somewhat better adapted to change. This has been a matter of necessity, because sluggish communities soon fall behind. In the ancient days of peasant stability, there was no need for institutions like Consumer Reports to study and rate new products, or regulators like the Environmental Protection Agency to watch over new hazards. We developed the needs, and we developed the institutions. These mechanisms represent important adaptations, not so much to the technologies of the twenty-first century, but to the increasing change in technology during the twenty-first century. There is great room for improvement, but they can perhaps provide a basis for adapting to the next century as well. Even with the best of institutions to cushion shocks and discourage abuse, there will be problems. They very act of solving problems of production—of increasing wealth—will created problems of economic change. Perhaps Darwin was right to emphasize the importance played in nature by competition. Darwin told us that those species survived best which could adapt to their environment, and he let loose a phrase which he later regretted: “the survival of the fittest,” and when applied to social interactions of man—this philosophy is already seen to be true. #RandolphHarris 22 of 22

Cresleigh Homes

Let’s imagine a day in the life at your #PlumasRanch home at #CresleighMeadows Residence 2…https://cresleigh.com/cresleigh-meadows-at-plumas-ranch/quick-move-homesite-48/

The sun shines in the windows while you tidy up the living room, then lights up your lunch meal prep at the spacious island. 😎

Finally, you enjoy a great night’s sleep in the cozy bedroom. This could be your life, too; picture yourself at #CresleighHomes!

The Party Wall

America is among the most violent of the so-called civilized nations; our homicide rate is three to ten times higher than that of the nations of Europe. An important cause of this is the influence of that frontier brutality which we are the heirs of. We need a new kind of physical courage that will neither run rampant in violence nor require our assertion of egocentric power over other people. Whether an individual is allowed to enter a region, such as a room, or is excluded from it, one will often be required to show moral courage, which generally abhorrers violence and some kind of regard for the physical boundary around it, when there is one. Of course, theoretically it is possible for boundaries like thick walls to close the region off physically from outside communication; almost always, however, some communication across the boundary is physically possible. Social arrangements are therefore recognized that restrict such communication to a special part of the boundary, such as doors, and that lead persons inside and outside the region to act as if the barriers had cut off more communication than it does. The work walls do, they do in part because they are honoured or socially recognized as communication barriers, giving rise, among properly conducted members of the community, to the possibility of “conventional situational closure” in the absence of actual physical closure. #RandolphHarris 1 of 21

A glimpse of these conventions can be obtained by noting a fact about socialization: children in our middle-class society are firmly taught that, while it is possible to address a friend by shouting through the walls, or to get one’s attention by tapping on the window, it is none the less not permissible, and that a desire to engage anyone in the region must be ratified by first knocking at the door as the formal means of making entry. Windows themselves may provide an opportunity for partial participation in a situation and are typically associated with an understanding that such a possibility will not be exploited. Deviations from this rule can, of course, be found. In Sacramento, California, visiting seamen, described by some in the community as “of the lowest type,” would sometimes walk around cottages, and peer directly into the windows. After dinner we went down to the railroad again, and took our seats in the cars for Cosumnes River College. Being rather early, those men were curious in foreigners, came (according to custom) round the carriage in which I sat; let down all the windows; thrust their heads and shoulders; hooked themselves on conveniently by their elbows; and fell to comparing notes on the subject to my personal appearance, which as much indifference as if I were a stuffed figure. I never gained so much uncompromising information with reference to my own nose and eyes, the various impressions wrought by my mouth and chin on different minds, and how my head looks when it is viewed from behind, as on these occasions. #RandolphHarris 2 of 21

A chief characteristic of courage is that it requires a centeredness within our own being, without which we would feel ourselves to be a vacuum. The “emptiness” within corresponds to an apathy without; and apathy adds within corresponds to an apathy without; and apathy adds up, in the long run, to cowardice. That is why we must always base our commitment in the center of our own being, or else no commitment will be ultimately authentic. In the many mental hospitals where the nurses’ station is a glass-enclosed observation post, patients must be trained to keep from lingering around the windows and looking in on the life inside. (Interestingly enough, no hospital rule prohibits staff from looking out at a patient through these windows, thus maintaining an official form of eavesdropping.) The fashion of using “picture windows” for walls has, of course, introduced its own social strains, requiring great morale on both sides of window to ensure conventional closure; there are many cartoon illustrations of consequent problems. It may be added that failure to recognize a region boundary is often associated with according to those who are improperly observed the status of nonpersons. Where walls between two regions are known to be very thin, problems of reticence become pronounced. Sometimes open recognition will be given to the communication possibilities, with person talking through the wall almost as though they were all in the same social situation. #RandolphHarris 3 of 21

An analysis of an American semidetached housing development a suggests: “Developing our picture of neighbour linkage by ear from the comments of residents, we find that it is possible in these houses to entertain a neighbour’s wife by playing her favourite records with the gramophone or an iPhone turned to loud, or to mind her children or invite her to tea, all through the party wall.” Here, of course, we see some of the special functions of sight: those on the other wise of the party wall may not be present, or, if present, may not be attending, but it will be impossible to see that in this case. We are living at a time when one age is dying and the new age is not yet born. We cannot doubt this as we look about us to see the radical changes in mores involving pleasures of the flesh, in gender roles, marriage styles, in family structures, in education, in religion, technology, and almost every other aspect of modern life. And behind it all is the threat of the atom bomb, which recedes into the distance but never disappears. To live with sensitivity in this age of limbo requires courage. A choice confronts us. Shall we, as we feel our foundations shaking, withdraw in anxiety and panic? Frightened by the loss of our familiar mooring places, shall we become paralyzed and cover our inaction with apathy? If we do these things, we will have surrendered our chance to participate in the forming of the future. We will have forfeited the distinctive characteristic of human beings—namely, to influence our evolution through our awareness. #RandolphHarris 4 of 21

Years ago the General Electric Company was faced with the delicate task of removing Charles Steinmetz from the head of a department. Mr. Steinmetz, a genius of the first magnitude when it came to electricity, was a failure as the head of the calculating department. Yet the company did not dare offend this man. He was indispensable—and highly sensitive. So they gave him a new title. They made him Consulting Engineer of the General Electric Company—a new title for work he was already doing—and let someone else head up the department. Mr. Steinmetz was happy. So were the officers of G.E. They had gently maneuvered their most temperamental star, and they had done it without a storm—by letting hm save face. When one “saves face,” they retain respect and avoid humiliation. Letting one save face! How important, how vitally important that is! And how few of us ever stop to think of it! We ride roughshod over the feelings of others, getting our own way, finding fault, issuing threats, criticizing a child or an employee in front of others, without even considering the hurt to be the other person’s pride. If we let ourselves experience the evil, we will be forced to do something about it. It is a truth, recognizable in all of us, that when we do not want to become involved, when we do not want to confront the issue of whether or not we will come to the assistance of someone who is unjustly treated, we block off our perception, we blind ourselves to the other’s suffering, we cut off our empathy with the person needing help. #RandolphHarris 5 of 21

Hence the most prevalent form of cowardice in our day hides behind the statement, “I did not want to become involved.” Whereas a few minutes’ thought, a considerate word or two, a genuine understanding of the other person’s attitude, would go so far toward alleviating the sting! Let us remember that the next time we are faced with the distasteful necessity of discharging or reprimanding an employee. Even if we are right and the other person is definitely wrong, we only destroy ego by causing someone to lose face. Hurting a person’s dignity is a real crime. Man lives under a great many laws—physical, physiological, biological, laws created by man himself and so on, until we come to the laws of personal life and finally to imaginary “I.” This is the most important law which governs our life and makes us live in the non-existing seventh dimension. A great many forces or influences act on a man at any given moment, though people are chiefly controlled by imagination. We imagine ourselves to be different from what we are and that creates illusions. However, there are necessary laws. We are limited to certain food and to certain air, to a certain temperature and so on. We are so conditioned by influences that we have very little possibility of freedom. It is necessary for us to change our inner attitude. People who live exclusively under A influences and who take B influences, if they meet them, on the same level as A influences, usually die in this life. They may be physically alive but that does not mean that their essence can develop. #RandolphHarris 6 of 21

“Do dead people look like everyone else? Do they live as we live?” Quite, yes. Because they have soul and the remains of essence. They can insure themselves!” “You spoke previously of creating a permanent ‘I.’ What do you mean by that?” I mean that when you say “I” you can be sure that it is the same “I” each time. Now you say, “I want this” and half an hour later you say, “I want that.” The “I” is quite different. There is one thing—you—and there are many imaginary “I”s. You is that really is, and you must learn to distinguish it. It may be very small, very elementary, but you can find something definite and permanent and sufficiently solid in yourself. If you remembered all that has been said, you would remember yourself at the end of ten weeks. For instance, take the study of false personality. This is one of the quickest methods. The more you understand false personality the more you will remember yourself. What prevents self-remembering is, first of all, false personality. False personality cannot and does not wish to remember itself, and it does not wish to let any other personality remember. It just tries to stop self-remembering; takes some form of sleep and calls that self-remembering. Then it is quite happy. False personality is something special; you are opposed to it. False personality must be made to disappear or, at any rate, it must not enter into this work. This applies to everybody and everybody must begin in this way. #RandolphHarris 7 of 21

Firs of all you must know your false personality and you must not trust it in any way—its ideas, its words, its actions. You cannot destroy it but you can make it passive for some time, and then little by little you can make it weaker. False personality does not really exist but we imagine that it exists. It exists by its manifestations but not as part of ourselves. Do not try to define it or you will lose your way in words, but it is necessary to deal with facts. Negative emotions exist but at the same time they do not exist; there is no real center for them. This is one of the misfortunes of our state. We are all full of non-existent things. [Someone said that he sometimes doubted the genuineness of this interest in the work; he might by lying to himself.] Only you can answer that, and only if you do not forget the fundamental principles by saying “I” about something when it is only one “I.” You must get to know other “I”s and remember about them. If you forget this you forget everything. So long a you remember this you may remember everything. Forgetting about this is the great danger, and one slight change in something is sufficient to make everything wrong. Some groups of “I”s are useful, some are artificial and some are pathological. All people play roles; each person has about five or six roles which one plays in one’s life. One plays them unconsciously, or if one tries to play them consciously, one identifies with them very soon and continues to play them unconsciously. These roles together make the imaginary “I.” #RandolphHarris 8 of 21
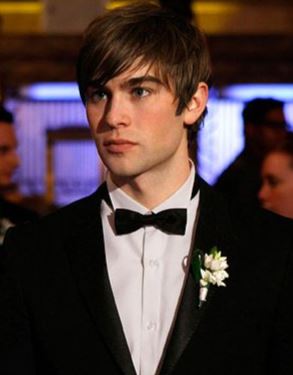
False personality is imaginary “I.” [Somebody asked where higher states of consciousness could produce more thoroughly bad people or more thoroughly good people equally.] No, that is wrong. Bad people can be produced only by increase of mechanicalness. Self-remembering cannot produce wrong results provided the connection is kept between it and other ideas of the system, but if one omits one thing and takes another thing from the system—for instance, if one seriously works on self-remembering without knowing about the idea of division of “I”s, so that one takes oneself as one (as unity), from the beginning—then self-remembering will give wrong results and may even produce wrong crystallization and make development impossible. There are schools for instance or systems which, although they do not formulate it in this way, are actually based on false personality and on struggle against conscience. Such work must certainly produce wrong results. First it will create a kind of strength, but it will make the development of higher consciousness an impossibility. False personality either destroys or distorts memory. Self-remembering is a thing which must be based on right function. At the same time you must work on the weakening of false personality. Several lines of work are suggested and explained from the beginning and all must go together. You cannot just do one thing and not do the another. All are necessary for creating this right combination, but first must come the understanding of and struggle with false personality. #RandolphHarris 9 of 21

Suppose one tries to remember oneself and does not want to make efforts against false personality, then all its features will come into play, saying, “I dislike these people; I do not want this, I do not want that,” and so one. Then it will not be work but quite the opposite. If one tries to work in this wrong way it can make one stronger than one was before but in such a case the stronger one becomes, the less is the possibility of development. Fixing before development—that is the danger. We are thus not dealing with hobbies, do-it-yourself movements, Sunday painting, or other forms of filling up leisure time. Nowhere has the meaning of creativity been more disastrously lost than in the idea that it is something you do only on the weekend. The creative process must be explored not as the product of sickness, but as representing the highest degree of emotional health, as the expression of the normal people in the act of actualizing themselves. Creativity must be seen in the work of the scientist as well as in that of the artist, in the thinker as well as in the aesthetician; and one must not rule out the extent to which it is present in captains of modern technology as well as in a mother’s normal relationship with her child. Creativity is part of self-remembering and is the process of making, of bringing into being. Now this intensity of awareness is not necessarily connected with conscious purpose or willing. It may begin in dreams or at an unconscious level. #RandolphHarris 10 of 21

The makes source—any data, information, or knowledge that is communicated requires a source or sender; a set of channels or media through which the message flows; a receiver; and of course a message. Power players intervene at each of these points. Take the sender. When a letter arrives in the mail, the first thing we usually wan to know is who sent it. The identity of the Sender is, in fact, a crucial part of any message. Among other things, it helps us decide how much credence to give the message. This is why the “Masked Source Tactic” is so frequently used. An ostensibly nonpartisan citizen group that sends out millions of fund-raising letters may actually be financed and controlled covertly by a political party. A political action committee with a fine-sounding name may be run by the lobbyist for a rapacious industry. A patriotic-sounding organization may be controlled by another nation. Both the KGB and he CIA covertly channel funds into publications, labour unions, and other institutions in targeted countries and help set up friendly organizations. The “Masked Source Tactic” is the basis for front groups of all political stripes. However, masking the message-sender can take many forms, in many different settings, from business boardrooms to prison cells. An imprisoned murderer once described how she could bring power to bear on a jail guard who was harassing her. She could, she said, write a letter of complaint to the prison warden. However, if the guard found out, life would be made even more miserable for her. #RandolphHarris 11 of 21

She could also, she said, go over the warden’s head and write to a politician complaining of brutal treatment, and pleading with him to put pressure on the warden to call off his guard. However, this was even more risky. “Fortunately,” she observed in a memorable phrase, “prisons are filled with idealist. And so,” she said, “I could get another inmate to write to the politician for me,” thus concealing the real source of the message. Officials throughout business and government play variations of this fame. When an underling “pulls rank,” using a superior’s name (often without authorization) to gain an advantage, he or she is using the Masked Source Tactic. A classic twist on the Masked Source Tactic influenced U.S.A. policy during the Vietnam War. It was used in 1963, when a report prepared by Robert McNamara and General Maxwell Taylor advised the President and the nation that “it should be possible to withdraw the bulk of U.S. personnel” by the end of 1965. This forecast was bolstered by data supposedly originating in Saigon. What readers of the report were not told is that much of what was datelined Saigon had been prepared in Washington, the transmitted to Saigon so it could be sent back to Washington looking as though the data actually came from the field. The source was disguised to lend the data greater authenticity. A special class of Masked Source messages are outright forgeries. Seldom used in everyday bureaucratic warfare, it is well known in international affairs where strange forgeries have on occasion changed history—like the Zimmerman Telegram that helped propel the United States of America into World War I. #RandolphHarris 12 of 21

In 1986, the U.S.A. State Department publicly exposed as forged a document that described a “confidential” meeting at the Pentagon. It quoted then Secretary of Defense Caspar Weinberger as saying that SDI, the Strategic Defense Initiative, would “give the United States…the ability to threaten the Soviet Union with a knockout blow.” If true, the quotation would have bolstered Soviet arguments against the SDI program. However, the document was a fake circulated in West Germany (presumably by the Soviets) as part of the public campaign drumming up sentiments against SDI. Another forged document about SDI turned up in the Nigerian press. More recently an anti-Japanese forgery turned up in Washington Congressman Tom McMillen rose in the House of Representatives to read what he called an “internal, high-level Japanese government memo.” Ostensibly addressed to the Prime Minister from his “Special Assistant for Policy Coordination,” the memo called for Japanese investments in the United States of American to be planted in congressional districts where they could be used to influence the U.S.A. politics. Nothing could have been better calculated to intensify Japan-bashing in the United States of America. However, rather than a Japanese government document, it turned out to be an embarrassing fiction traced to Ronald A. Morse, an official of the Asian program of the Woodrow Wilson Center for Scholars. Morse said that he had written it merely to illustrate, in a dramatic way, what he believed to be current Japanese attitudes. He claimed he had told its recipients the document was bogus. #RandolphHarris 13 of 21

Markets and demonstrations illustrate how strategies can be selected very quickly. Typically, selection at the strategy level is faster and less costly than selection at the agent level. Nevertheless, these differences are tendencies rather than inevitable consequences. So, by way of counterexample, large corporations are often faced with new products from start-up competitors. They sometimes find it quicker to create new divisions or small spin-off firms to make a comparable product rather than modifying existing lines of activity to produce it. In effect, this is a case where agent creation may be faster than strategy copying. Although the differences we have mentioned are only tendencies, they are rooted in the added difficulty that is typical for creating full agents. Hence it is often important to compare possibilities for selection at the agent and strategy levels. A further difference between selection at the two levels involves problems that commonly occur in inferring exactly what is to be copied. There are myriad ways that selection can go awry and incorrectly reward an agent or strategy that was not responsible for a success. Such failures plague selection at both levels. However, one important difference does occur. Agents are collections of strategies. Successful agents generally use strategies that are mutually compatible. The interaction among those strategies does not have to be understood if selection is at the level of the agent, copying all its strategies. #RandolphHarris 14 of 21

Biological selection of whole agents capitalizes mightily on this fact, but so can identical replication of franchised business units. Selection at the strategy level generally demands higher quality of inference. How many of the agent’s action patterns must be copied to replicate the success? Which ones? To obtain the same low defect rate as a rival firm, which of their quality control procedures should be emulated? Selection at the agent level, on average, is more context preserving than at the strategy level. In Complex Adaptive systems, where many results derive from effects that multiply other effects, context preservation can work to retain and spread synergies that are not fully understood. We made a related point in a past reports when we observed that the longer time horizons of those in authority create a common context for coordinating the faster actions of those they supervise. There we were examining agents’ activities. Here we are examining the selection that follows from their success or failure. We have argued that there are tendencies for selection at the agent level to be more costly, slower in elapsed time, and more context preserving. The first two effects are often not wanted, while the last one frequently is. This can set up a tension in which a designer or policy maker who has some freedom to influence the level of selection may have to trade off the various factors. #RandolphHarris 15 of 21

To take an example: Supposed that you want to discourage a dangerous behaviour such as violating crucial safety regulation. We have usually considered selection for positive traits, but here we can look at negative selection. At the level of strategy, selection may correspond to punishing the action pattern. Each detected instance of rule breaking could be heavily fined, for example. On the other hand, agents could be negatively selected in response to their violations. An offering employee could be suspended, transferred, or even fired. These forms of removal will make the agent less likely to be copied. Taking the agent out of circulation and making the effort of replacement typically costs more and takes longer than simply changing an agent’s strategy. If the safety violation is integrated with other strategies—for example if the agent’s entire work style used a set of methods now considered unsafe—simply punishing the violations may not discourage the behaviour, so removal may be worthwhile. If the violations are more a matter of “fashion”—for example, not wearing a hard hat in order to look fearless—pushing the action itself may be the preferred approach. Schemes to amplify success are nearly always imperfect. Selection at the level of agent and selection at the level of strategy are families of mechanisms that have somewhat complementary strengths. Agent selection often works on longer time scales—faster is not always better—and preserves variation and context. Strategy selection isolates key patterns that can be more easily and rapidly copied. #RandolphHarrs 16 of 21

Thus it is not surprising that there are many hybrid systems, where selection is found to be operating at both level in a single population of agents. Many species of birds and mammals seem to select at both the agent level, by conventional natural selection, and at the strategy level, by processes of cultural diffusion, which operates at a much faster times scale. In the human case, cultural evolution is so rapid and effective that we tend to ignore the continuing operation of natural selection. At the other extreme, we often do not notice cultural aspects of an animal population. However, close observation relevels striking cases, such as the English birds that discovered how to peck through foil milk bottle caps. Their discovery spread across the entire country within a few years. Hybrid systems such as this have tremendous advantages. Herbert Simon has argued that they are so beneficial that we could expect biological evolution to create individuals with increased susceptibility to following strategies suggested by others. Even though this “docile” quality makes it possible to take advantage of individuals who possess it, that can be outweighed by the tremendous gains of adding cultural selection of strategies to natural selection of agents. These observations on complementary strengths and hybrid selection systems have a cumulative implication. When there is room to alter selection process, it can be wise to look for changes to the system that could diversify it, adding fast elements if its selection processes are slow. #RandolphHarris 17 of 21

If the past processes are not succeeding, it can pay to add slower elements that sustain new context. As an example of adding fast elements, organization that rely heavily on change through personnel turnover are often ripe for improved trading of employee “war stories.” A series of failures in piecemeal importing of “best practices” might suggest brining in a new supervisor experienced in how the various routines form an interlocking system. As with many other interventions we discuss, hybridizing selection processes is not guaranteed to be better, but it is often a beneficial focus of attention. Natural law imposes limits, but so does the nature of human beings. These will continue as long as people do. Reproduction is a deeply ingrained instinct enforced by the march of time, which ruthlessly discards the genetic material of all who neglect it. Many would argue that the Earth is already overpopulated and that is why land prices and housing is so expensive. While nanotechnology could enable the current population, and even a great increased one, to live more lightly on Earth, there will still be limits to Earth’s capacity. The norms of human life are shaped by ancient patterns: high rates of infant or childhood mortality have been facts of life for millennia, and having many, many children has been a way to ensure that one or two will survive to work on the farm, and to care for you in your old age. Of course, many parents tend to use and abuse their adult children these day. #RandolphHarris 18 of 21

Large families naturally become traditional. And that is why generational housing is being built, where in some large homes they also have an apartment added on inside of the house, so adult children or parents can be part of the family home, without feeling like a guest or being a burden on the home owner. And also, it gives the homeowner a chance to have a true office at home. When modern medicine and reliable food supplies change those conditions—as they have, in cultural terms, virtually overnight—behaviour does not shift as quickly. The result is the Third World population boom. In Western countries, where there has been time for behaviour to adapt, a huge family is the exception. It might seem that our problem is solved. Molecular manufacturing can make everyone wealthy, and wealthy populations today have stable or shrinking populations. The Earth can support more people with advanced technologies, and these will also open up the vast room and resources of the World beyond Earth. Would that this were true. If 99 percent of the people in a population respond to wealth by reducing childbearing, the population will indeed stabilize or shrink, for a whole. However, populations are not uniform. What of the 1 percent, say, who are member of a minority group with different values? If that minority group has a growth rate of 5 percent per year, then in ninety-five years they will be the majority, and in one thousand years their population will have grown by a factor of 1,500,000,000,000,000,000,000, if resource limits or genocide have not intervened. #RandolphHarris 19 of 21

Not that the Hutterites of North America, a reasonably wealthy religious group viewing fertility control as a sin and high fertility as a blessing, have managed an average of ten children per woman. Given enough time, exponential growth of even the smallest population can consume all the resources in reach. The right to reproduce is often regarded as basic, as illustrated by the outage at reports of forced abortion in the People’s Republic of China. The Hutterites and many others regard it as part of their freedom of religion. However, what happens when parents have more children than they can support—does redistribution solve the problem? Of course, in America, some women sell babies to get new cars and stuff like that. However, if reproduction is not forcibly suppressed, and if resources are forcibly and repeatedly redistributed so that each human beings has a roughly equal share, then each person’s share will steadily shrink. Even given the most optimistic assumptions regarding available resources, with a policy of resources redistribution and unlimited reproduction, the amount per person would eventually be insufficient to sustain life. This policy must be avoided, because if it is followed, it will kill everyone. #RandolphHarris 20 of 21

As soon as we grant that any entity is entitled to certain rights—whether that entity be a human child, an animal, or some future artificial intelligence—the question arises of who is responsible for providing resources to support it when it cannot do so for itself. The above argument indicates that a policy of coercion by some central power to compel the entire population to support an exponentially exploding population of these individuals would lead directly to disaster. Ultimately, this responsibility must rest with the entities’ initiator: the designer of the artificial intelligence, the owner of the pet, the parents of the child. No new technology can magically remove the limits imposed by natural law, and thereby lift the burden of human responsibility. Every time a technology solves a problem, it creates new problems. This does not mean that the change is neutral, or for the worse, of course. The Salk and Sabin Vaccines for polio virtually destroyed the iron-lung industry, and the pocket calculator virtually destroyed the slide-rule industry, but these advances were worth the price of some economic adjustment. Molecular manufacturing and nanotechnology will bring far greater changes, placing far greater strains on our ability to adapt. We should not be surprised when basically beneficial applications make someone miserable. Our lives are largely centered around problems. If we can solve many of these problems, the centers of our lives will shift, creating fresh problems. We have sketched some of the issues of change and adaptation more to raise questions than to offer solutions. #RandolphHarris 21 of 21

Cresleigh Homes

Cresleigh Ranch at Mills Station features new luxury homes with expansive floor plans and artisan-inspired designs.

Picture late nights 🍷 on the porch and chalk drawings in the driveway…when you find the perfect home for you and your family, there’s nothing left to do but make memories! 💖

Homesite #56 is available at #CresleighRanch #MillsStation – it’s the Residence 3 floor model and we think you’ll love it.

Head to our website for more info!

#CresleighHomes
A Kind Heart Will Extend this List Even Further

Psychoanalysis serves many functions. It can assist in promoting psychic growth and self-realization. I am sorry to say that only a small minority seem to be interested in psychic growth these days. Most people have an entirely different goal, which is to own more and consume more. It has been suggested that persons are kept from improperly approaching others by self-applied rules and by legal sanctions. However, in addition to these means of social control there are other kinds, designed not so much to alter the offender’s pattern of misbehaviour as to allow a particular victim to escape from the deprivation inflicted by the offense. I want to mention some of these techniques here, even though they, and some of the issues which follow, occur in regard to the acquainted as well as the unacquainted. If one is approached on the street by someone in need and does not wish to give the individual money, any one of three courses may be followed: One may spare the individual in need the embarrassment of a refusal by pretending not to notice the person’s appeal; or one may refuse, saying, “No, I’m sorry”; or one may stop and offer help by suggesting a charitable organization to which the unfortunate can apply. A kind heart may extent this list even further, but the essential point is that if one is asked for charity, an apology must accompany a refusal. Quite apart from other considerations, any sign of anger or impatience is brutally ill-mannered. #RandolphHarris 1 of 18

Another strategy is what might be called the “terminal squirm.” Here, the unwilling recipient of the overture grudgingly turns his attention to the speaker, gives a noncommittal reply, and then as quickly as possible turns away, taking for granted that the other will take this answer as a “signing out” cue. In our society, this technique is often employed by parents with their importuning patients. Given the fact that importuned persons attempt to avoid the importuners, we can expect that there will be an attempt on the part of importuners to counter this counter (and, in turn, an attempt on the part of the importuned to counter this counter to a counter). A counter to the strategy of acting as if no overturn has been received is to inveigle an individual into an explosive demonstration that one is not in fact as little involved and affected by the entreaties as one appears to show. In everyday terms, this is sometimes called “getting a rise.” Thus, children often play games of making funny faces at one another to see who will win the contest between “straight face” and laugh-provoking gesture. The phenomenon of getting a rise, or reciprocally, rising, also occurs when the butt is already involved in a face engagement with the stimulator, in which case getting a rise will consist in forcing the butt suddenly to “flood out” and sharply increase one’s level of manifest seriousness, mirth, and the like. Sometimes the teaser employs a passing remark calculated to make the butt become suddenly affronted, only to perceive at the next moment the unserious intent. #RandolphHarris 2 of 18

Sometimes the teasing or goading is continuous and mounting until successful, as in the game of “the dozens.” In mental hospitals rise-getting seems to be a common pursuit, practiced by junior staff and by patients upon patients who insist on being mute, and by still other patients who make wonderfully humorous efforts to entice staff into communicative contact. On a hospital ward, a middle-aged woman patient employed some expert techniques for getting others, against their wishes, into a state of talk. She would come progressively closer to the unwilling participant, increasing the loudness of her comments and the impropriety of their references, as well as the grotesqueness of her facial grimaces, until a point was reached where the participants could no longer maintain the fiction of not being engaged, and would, in some way, respond. In addition to this technique of progressive profanation, she would employ antics, dancing, prancing, and jumping in the immediate presence of the recalcitrant participant, stopping only when she succeeded in getting the other involved. If these antics failed, she would sometimes employ the strategy of stopping abruptly and then looking into the eyes of the other in secret collusive derision of the self that had just behaved in a peculiar way. The other would then frequently find himself entering into this collusion, establishing communion with an individual who, apparently, had suddenly become sane. #RandolphHarris 3 of 18

If this, too, failed, she would sometimes make offensive, abusive, or mimicking gestures at one individual, in a way that could barely be defined as behind his back, and then quickly turn to a second individual with a knowing, “I am-just-trying-to-kid-this-fool” look; the person receiving this collusive look often allowed himself to be trapped momentarily into a byplay, and thereby lost the game. Interestingly enough, she was able to combat the lack of civil inattention that nurses in the glassed-in nursing station accorded her—either by their pointed not-seeing of her or by their staring at her—by getting a rise from them even through the glass partition designed to protect them, and even at a time when they were working every effort to demonstrate that they would not be drawn into communication unless properly approached by a proper person. Underlying principles of respect that were once commonplace in society have increasingly given way to unkind behaviour. To help our children and youth set aside the many negative examples that bombard them, we must first understand respect and reasons we sometimes act disrespectfully. There are people in the community who merit respect through honourable living. We admire their commitment or standards. For example, we might respect a sailor who gave up winning a boat race to save a man overboard. On the other hand, we do not respect one who embezzles or another who treats a child hardly in the supermarket. #RandolphHarris 4 of 18

Yet if we were to interact with these people, we would likely treat them with respectful or polite manners, regardless of our feelings about their transgression. Ultimately, we can treat people respectfully because they are human even if we do not honour or admire their acts. We are taught to be respectful toward others without qualification, sometimes we may find ourselves falling into rationalizations about being disrespectful based on their behaviour. A person who causes a problem is often seen as warranting disrespectful treatment. However, we can not live our lives with the philosophy: if others would behave differently, we would not have to behave badly. This kind of thinking shifts responsibility for our behaviour to others. It makes us think that our disrespectful acts are someone else’s fault. Respect is an expression of our sense of universal brotherhood or sisterhood—a testimony of our membership in the human family. It acknowledges our common humanity and shows our reverence for being alive. However, it is also important to keep in mind that no one likes to take orders. Resentment caused by a brash order may last a long time—even if the order was given to correct an obviously bad situation. #RandolphHarris 5 of 18

Dan Santarelli, a teacher at a school in Wyoming, Pennsylvania, told one of our classes how one of his students had blocked the entrance way to one of the school’s shops by illegally parking his car in it. One of the other instructors stormed into the classroom and asked in an arrogant tone, “Whose Toyota is blocking the driveway?” When the student who owned the car responded, the instructor screamed: “Move that car and move it right now, or I will wrap a chain around it and drag it out of there.” Now that student was wrong. The car should have not been parked there. However, from that day on, not only did that student resent the instructor’s action, but all the students in the class did everything they could to give the instructor a hard time and make his job unpleasant. How could he have handled it differently? If he had asked in a friendly way, “Whose Toyota is that in the driveway?” and then suggested that if it were not moved, other cars could get in and out, the student would have gladly moved it and neither he nor his classmates would have been upset and resentful. Also, instead of pushing people to accelerate their work and rush through projects, call everybody together, explain the situation to them that it is crucial that they do their best work and as fast as they can so the business can succeed. And then ask, “Is there anything we can do to help in this situation?” “Can anyone think of different ways to process it through the corporation that will make it possible to handle the project?” #RandolphHarris 6 of 18

“Is there any way to adjust our hours or personnel assignments that would help?” The employees will often times come up with many ideas and will feel confident handling the project. They will approach it with a “We can do it” attitude, and that is how effective leaders become and stay successful. Ask questions instead of giving direct orders. A human with a passion for absolute control will try to circumvent, to overstep the limits inherent in human existence, for it is part of the human condition that we are not omnipotent. And if a man should gain much too much power, death will show him how powerless he is in the face of nature. Therefore, this leads many to ask the question, “Is essence always good?” Not at all. Essence is mechanical, it does not live by itself, it has no special thinking apparatus; it has to think through personality. Essence, type and fate are practically the same, but facts connected with fate are very difficult to find, expect perhaps just almost physical facts such as kind of health, capacities or similar things. There are many other things but they are hard to distinguish because in our state essence seldom works separately from personality. Many things that we have the inclination to ascribe to fate really belong to personality. So it is dangerous to draw conclusions. However, there are some things we can see, for instance that certain types of people attract certain types of people. They have the same kinds of friends, the same kinds of troubles, the same kinds of difficulties, but, of course, never without personality taking some part. So you cannot call it pure fate; it is more like cause and effect. #RandolphHarris 7 of 18

“Must one work harder to alter one’s type than to alter acquire personality?” If it is necessary, but perhaps the type is quite all right. In most cases it is personality that must be changed; uncontrolled personality cannot be right. Only very few people can work on essence. It is not exactly an advantage to the people who can, because it is very difficult for them. Generally we work on personality, and this is the only work we can do, and if we work it will bring us somewhere. “When we try to change our being is essence as much as affected as personality?” We have to work on personality but essence is affected if we really change something. “Did you say that personality is all lies?” No, I said that personality was almost all artificial, just as essence is almost all real. “Are our ‘I’s part of personality of essence?” Both. There are “I”s belonging to essence and “I”s belonging to personality. “Are they connected with different centers?” continued the same questioner. Certainly, there are intellectual “I”s, moving “I”s and instinctive “I”s. An “I” is just one desire, one wish. However, this distinction is only for convenience. You may forget it if you like, although it is like that. Just take it that “I”s are small and personality is already more complicated desires. “Is the instinctive center closely connected with one’s essence?” Yes, it controls the necessities of essence. “Is intelligence part of essence?” #RandolphHarris 8 of 18

Generally speaking, yes. However, I would like to know what you mean by intelligence. If I say “yes” you cannot apply it; it will remain dead capital. “Can intelligence grow or increase by certain treatment?” asked the same questioner. That is what I said. If we speak about ourselves, we shall see that intelligence belongs to essence and personality in a very mixed way; though, in a cosmic way, a certain amount of intelligence is given to every essence. I believe the human being is fully himself only when he expresses himself, when he makes use of the powers within him. If he cannot do that, if his life consists only of possessing and using rather than being, then he degenerates; he becomes a thing; his life becomes pointless. It becomes a form of suffering. Real joy comes with real activity, and real activity involves the utilization and cultivation of human powers. We should not forget that exerting our minds encourages the growth of brains cells. That is a fact supported by physiological evidence. An alternative to selecting entire agents as the basis for the amplification of success is to make copies or recombinations at the level of particular strategies. If success can be assessed at the strategy level rather than the agent level, one difference that often occurs is a lowered cost of copying. To assemble or acquire a whole new agent (a new person, a new business, a new governmental unit) is typically more costly than to copy a strategy employed by a successful agent. It takes years to grow several Pacific yew trees for bark that provides cancer-fighting compounds for a single patient. #RandolphHarris 9 of 18

An owner of a baseball team can try to buy a star pitcher from another team. If the reason for success is that the pitcher is winning by throwing the forkball, it might be more advantageous to tech the other pitchers that strategy during the off-season. Whether this will be promising or not depends on how easily the forkball can be copied. Is there a pitching coach for hire with success in teaching it? Or perhaps success depends on the uncanny similarity of the star’s forkball and fastball motions. Then it may be necessary to pay the cost of acquiring the whole agent, with the entire complement of strategies, or of searching for another pitcher with a comparable package of skills. A second difference that often occurs between the strategy and agents levels is waiting time. One could just think of this as a special case of higher costs, but it deserves a brief discussion of its own. Because assembling copies of agents is generally a larger task involving more resources, it typically takes more time than copying or recombining strategies. Even if the direct costs of agent copying were affordable, the indirect costs of delay might not be. For example, another company may have a propriety process for manufacturing a part that does into a product you are developing. It might be quite valuable to invent your own process for making the needed component, and plausible to create a division within your company to do it. #RandolphHarris 10 of 18

It would lower your costs and let you tailor the part to your particular needs. However, competitors are racing to the market for your own product. The delay while you create a capacity to make the part means falling behind in competition with them. So you license the existing process from its owner, copying the strategy not because of lower monetary costs but because of the value of elapsed time. To highlight the speed at which strategies can change, consider a stock market. Agents watch changes in prices for information about what other agents believe. Thus the market has recursive nature in which agents’ expectations are formed on the basis of their anticipation of other agents’ expectations. The result can be rapid bubbles and crashes. Simulations of markets as Complex Adaptive Systems demonstrate how high rates of exploration can generate these bandwagon effects and “market psychology.” Social mobilization is another arena in which agents’ expectations are formed by watching each other’s behaviour. Again, the result can be very rapid change once a bandwagon begins. The fall of the Berlin Wall occurred with amazing speed once the initial demonstrations showed what was possible. As in a market, people formed their expectations on the basis of their anticipation of others’ expectations. Once begun, a series of demonstrations set off a cascade of revised beliefs leading to irresistible levels of protest. #RandolphHarris 11 of 18
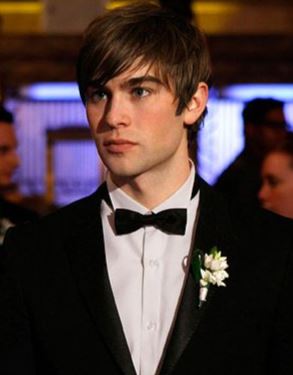
On July 4, 1967, in the White House, President Lyndon Johnson signed a measure called the Freedom of Information Act. At the signing ceremony he declared, “Freedom of information is so vital that only the national security, not the desire of public officials or private citizens, should determine when it must be restricted.” No sooner had Johnson spoken than a reporter asked if he could obtain a copy of the original draft of these remarks. It was the first request made in the full radiant flush of the new freedoms guaranteed by the act. Johnson turned him down cold. The “Secrecy Tactic” is the first, probably oldest, and most pervasive info-tactic. Today the U.S.A. government classifies as secret some 20 million documents a year. Most of these pertain either to military diplomatic affairs—or to mattes that might embarrass officialdom. However, if that seems undemocratic and even hypocritical, most other countries are far more secretive, defining everything from alfalfa yields to population statistics as state secrets. Some governments are positively paranoid. Virtually everything they do is secret unless specifically declared otherwise. Secrecy is one of the familiar tools of repressive power and corruption. However, it also has its virtues. In a World filled with bizarre generalissimos, narco-politicians, and killer-theologians, secrets are necessary to protect military security. #RandolphHarris 12 of 18

Moreover, secrecy makes it possible for officials to say things they would not utter in front of a TV camera—including things that need saying. They can criticize their bosses’ policies without embarrassing them publicly. They can compromise with adversaries. Knowing how and when to use a secret is a cardinal skill of politician and bureaucrat. Secrets give rise to the second most common info-tactic, another classic tool of power: the “Guided Leak Tactic.” Some secrets are kept; others leak. When the leak is inadvertent it is merely an ineffectually kept secret. Such leaks drive officials into deep dementia. “Why,” one CIA official is supposed to have asked, “do we have to sent the China estimate to U.S military commands overseas just because that’s where the action is? That’s where the leaking is, too.” In short, better to keep information secret than to send it to those who need it. By contrast, “guided leaks” are informational missiles, consciously launched and precision-targeted. In Japan targeted leaks have produced spectacular effects. The Recruit-Cosmos financial scandal, which led to the ouster of Prime Minister Noboru Takeshita in 1989, offered a field day for leakers mainlining inside information from the office of the chief prosecutor, Yusuke Yoshinaga, to the daily press. “Without these press leaks,” says Takashi Kakuma, author of books on corruption in Japan, “I’m sure their investigation would have been stopped.” #RandolphHarris 13 of 18

Reporters received carefully timed spurts of information, which were moves in an exquisite power ballet. By releasing details to the press, the prosecutors prevented higher-ups in the Ministry of Justice from emasculating the investigation and protecting the upper reaches of the Takeshita government and the Liberal Democratic Party. Without these guided leaks, the government might have survived. In France, too, leaks have historically played a major political role. Recounting France’s difficulties in disentangling from the Indochina War, a White House document states: “Leak and counter leak was [sic] an accepted domestic political tactic…Even highly classified reports or orders pertaining to the war were often published verbatim in the pages of political journals.” So prevalent are leaks in London that they have created a pall of suspicion inimical to innovation. Officials hesitate to voice a new idea, he charges, for fear it will be leaked instantly and its author made to look ridiculous before the idea has had a chance to be considered. However, unless someone things, which sooner rather than later entails thinking aloud, no new thinking will be done and no old thinking will be brought up to date. In Washington, where guided leaks from a still unidentified source called Deep Throat forced Richard Nixon to resign the presidency, and where guided leaks are still a daily phenomenon, leak-phobia is rampant. #RandolphHarris 14 of 18

Thirty five years ago, presidential assistants felt free to write candid memos and have serious, far-reaching disagreements with each other—and the President. Watergate put a stop to that. One quickly learned never to write anything on paper that you would be unhappy to see on the page of The Oakland Tribune…Never say anything controversial in conversation where more than one person was present. The ironic consequence when the really inconsequential issues come along, an army of bureaucrats moves in to consider it [sic]. However, the more important the issues, the fewer the numbers involved—almost solely because of the fear of leaks. Of course, the same officials who excoriate leakers are themselves very often the best source of guided leaks. While serving in the White House as national security adviser, Henry Kissinger once wanted the telephones of his staffers wiretapped to find out whether they were leaking embarrassing information to the press and Congress. However, Kissinger himself was—and remains—a “leak-master.” Secrets and guided leaks, however, are only the two most familiar info-tactics used in political and bureaucratic war. They may not be the most important. Many of you will remember a game from elementary school called “one-two-three shoot” or “matching fingers.” In this contest, one of the players chooses “evens” and the other player gets “odds.” On the count of three, each of the two players simultaneously casts out either one or two fingers. If the total number of fingers is even, the “even” player wins, while if the sum is odd, the “odds” players wins. #RandolphHarris 15 of 18
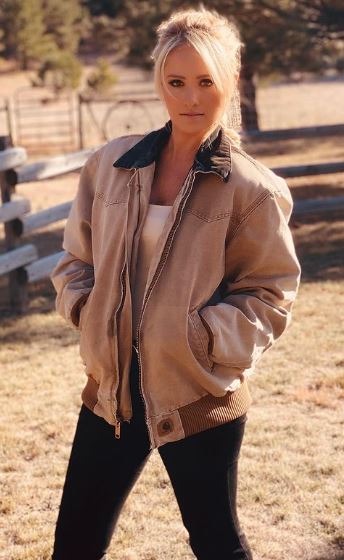
Supposed the loser pays the winner a dollar. We can compute the usual table of wins and losses in relation to the choices of strategies. There is no equilibrium to this game if the two players do not act randomly. Imagine that “Odds” were to play 1 finger with certainty. “Evens” would always choose to play 1 finger as well. Now the logic turns on itself. Since “Odds” is certain that his opponent will display 1 finger, he will choose to show 2 fingers. This leads “Evens” to respond with 2 fingers. In which case, “Odds” will play 1 finger. We are back where we started, and there is no end in sight to the circular reasoning. An easy way to check if randomness is needed is to consider whether there is any harm in letting the other player see your move before he responds. When unpredictability is needed, it would be disadvantageous to move first. Think what would happen in “one-two-three shoot” if you moved first: you would always lose. Not just any randomness will do. Suppose Odds chooses 1 finger 75 percent of the time and 2 fingers 25 percent of the time. Then Evens, by choosing 1, can, win 75 percent of the time, and on average get .75 X 1 + .25 X (-1) = .5 dollars per play. Similarly, the choice of 2 would lose Evens fifty cents per play on average. So Evens would choose 1. However, then Odds should be choosing 2, not the 75:25 mixture. The mixture would not survive the successive rounds of thinking about each other’s strategy. #RandolphHarris 16 of 18

In other words, there is an equilibrium pattern of randomness and it has to be calculated. In this example, the whole situation is so symmetric that the equilibrium mix has to be 50:50 for each player. Let us try that out. If Odds chooses 1 and 2 equally often, then Evens wins .5 X 1 + .5 X (-1) = 0 per play on average, whether he plays 1 or 2. Therefore he also wins 0 on average, whether he plays 1 or 2. Therefore he also wins 0 on average when he plays his 50:50 mixes are best responses to each other, that is, an equilibrium. The name for this solution is a “mixed-strategy” equilibrium, reflecting the necessity for the individuals to randomly mix their moves. The equilibrium mix in more general situations is not so evident from symmetry, but there are some simple rules for calculating it. People have often been wrong about physical limits, confusing the limits of their technology with the limits of the possible. As a result, learned men first dismissed the idea of heavier-than air flight, and then dismissed the idea of flying to the Moon. Yet physical limits are real, and all technology—past, present, and future—will stay within those limits. There is even reason to suspect that some of those limits are where the learned now believe them to be. Nanotechnology will make it possible to push closer to the real limits set by natural law, but it will not change those laws of the limits they set. It will not affect the law of gravity, the gravitational constant, the speed of light, the charge of the electron, the radius of the hydrogen atom, the value of Planck’s constant, the effects of the uncertainty principle, the principle of least action, the mass of the proton, the laws of thermodynamics, or the boiling point of water. Nanotechnology will not make energy or matter from nothing. #RandolphHarris 17 of 18

It seems a good bet that no one will build a faster-than-light spacecraft, or an antigravity machine, or a cable twice as strong as a diamond. There are limits. Science today may be wrong about some limits, but scientific knowledge is practically defined to be our best information about how the World works, so it is not wise to bet against it. There will be claims that nanotechnology will be able to do things that it cannot, or that capabilities are around the corner when they are not. Sometimes these will be innocent errors, sometimes they will be culpably stupid errors, and sometimes they will be what amounts to fraud. Among the problems that nanotechnology cannot solve is that of misguided claims, by people calling themselves “scientists,” “engineers,” or “businesspeople,” that they have a big technical breakthrough worth a fortune. Every interesting new technology, parcharlatans. For every Thomas Edison inventing useful products such as light bulbs or the precursor of movie projectors, there were people promoting electric hairbrushes to cure baldness, and electric shoes, electric belts, electric hats—the list goes on—that authoritatively claims cures for infertility, overweight, underweight, and all the ills and discomforts of mankind. Today, we are thankful that our forefather paved the way for us, and that we do not have to suffer the same credulity that they did. The more deprivation a person has to put up with, the more obedient one has to be so that one will not rebel against the deprivation imposed on one. #RandolphHarris 18 of 18

Cresleigh Homes

There’s something magical ✨ about dreaming about your new life in a new home this year – and we think the time has come for you to check out our community at #Havenwood!











